Staying Secure: Recent Security Breaches and Essential Prevention Strategies
The increasing reliance on digital technologies has led to the increased frequency of security breaches. Recent incidents have highlighted vulnerabilities across several industries, emphasizing the importance of robust cybersecurity measures. Here, we examine some notable security breaches that have recently made headlines, detailing the “how” and the responses taken to mitigate future risks.
Microsoft Azure and Executive Accounts
In a significant cyberattack on Microsoft Azure in January 2024, hackers exposed the accounts of hundreds of Microsoft senior executives to unauthorized access, with the use of phishing attacks and malicious links. The attackers used a password spray attack to break into the accounts, which is when an attacker tries several passwords across multiple user accounts to avoid detection systems. This breach allowed unauthorized access to Microsoft email accounts, leading to the exfiltration of sensitive emails and attached documents. The attackers also targeted source code and infrastructure, emphasizing the importance of heightened vigilance against sophisticated phishing tactics.
One extremely effective way to ward against this type of attack is to create strong passwords and change them regularly to prevent them from being hacked, as well as using multi-factor authentication.
Bank of America Third-Party Data Breach
Attackers understand that large banks have robust cybersecurity measures to protect their networks. However, many third parties lack similar resources and may not yet prioritize cybersecurity education or infrastructure. This makes them more likely to be targets for cybercriminals seeking vulnerabilities to exploit when sharing data with major institutions. This incident underscores the critical need for financial institutions to strengthen third-party vendor security protocols and ensure robust data protection measures.
The ransomware group LockBit orchestrated a breach targeting Bank of America in February 2024 via its third-party vendor, Infosys McCamish. Personal information—including names, Social Security numbers, and account details of over 57,000 individuals—was compromised.
Ascension Ransomware Attack
Such attacks necessitate comprehensive cybersecurity strategies to safeguard critical healthcare infrastructure and ensure uninterrupted patient care. Moreover, ensuring robust disaster recovery plans and reliable backups can get services back on track faster, which is particularly crucial for healthcare systems, because extended delay can directly impact patient care and safety.
Ascension, the owner of 15 hospitals in Michigan, fell victim to a ransomware attack in May 2024 that disrupted electronic health records systems, phone systems, and scheduling processes. Non-emergency procedures and appointments were suspended, highlighting the operational impact of cybersecurity incidents on healthcare services.
New York City Metropolitan Transportation Authority (MTA) Cyberattack
In 2020, research showed that municipalities, which are already vulnerable targets for cybercrime, faced 44% of global ransomware attacks—equating to approximately 133,496,000 incidents. An April 2021 cyberattack on the New York City Metropolitan Transportation Authority (MTA) compromised 18 systems, including those controlling train operations and safety mechanisms. This breach posed serious implications for public safety and operational continuity.
Following the attack, MTA swiftly implemented federally recommended security enhancements and mandated password changes and VPN switches for employees and contractors, illustrating proactive steps to fortify cybersecurity defenses.
Moving Forward: Prevention Procedures
Preventing security breaches requires a multi-faceted approach that empowers teams and safeguards organizational assets. Regular training sessions are essential to educate employees on identifying phishing emails, creating robust passwords, and understanding the importance of safeguarding sensitive information. This measure ensures everyone understands their role in preventing data breaches.
Strengthening asset management through classification, organization, automation, and continuous monitoring helps maintain an up-to-date inventory, facilitating informed decision-making and enhancing troubleshooting capabilities. Effective management and monitoring of access rights, supported by IAM, routine account audits, SSO, and multi-factor authentication, are also critical for ensuring only authorized personnel have access to certain resources.

Another strategy to prevent security breaches is implementing robust firewalls and antivirus software services, which can serve as the frontline defense against malicious threats. Regular updates to these defenses are crucial to identifying and addressing vulnerabilities promptly. Additionally, implementing automated data backup systems across multiple locations provides a safety net against data loss and physical damage, ensuring business continuity even in the face of unforeseen incidents. By integrating these preventive measures into comprehensive cybersecurity strategies, organizations can effectively mitigate risks and protect sensitive information from increasingly sophisticated cyber threats.
At Aunalytics, we are committed to preventing security breaches—protecting customer data is our top priority. We adhere to stringent security protocols, including regular employee training, robust encryption measures, and continuous monitoring of access controls. Our goal is to ensure our clients are utilizing the latest security technologies and best practices to stay protected, while having the right backup and disaster recovery strategies in place to get their businesses back up and running as quickly as possible in the event of a cyber event or disaster scenario.
How State and Local Governments Can Use Technology to Overcome Economic Challenges
How State and Local Governments Can Use Technology to Overcome Economic Challenges
At present, state and local governments are confronted with significant challenges stemming from the current state of the economy. This includes a decrease in tax revenues, sustained high inflation, and a shortage of proficient IT personnel, who are vital to their day-to-day operations. Industry experts consider technology as an effective solution to address inadequacies during challenging economic periods.
Fill out the form below to receive a link to the article.
Aunalytics is a data platform company. We deliver insights as a service to answer your most important IT and business questions.
How State and Local Governments Can Use Technology to Overcome Economic Challenges
How State and Local Governments Can Use Technology to Overcome Economic Challenges
At present, state and local governments are confronted with significant challenges stemming from the current state of the economy. This includes a decrease in tax revenues, sustained high inflation, and a shortage of proficient IT personnel, who are vital to their day-to-day operations. Industry experts consider technology as an effective solution to address inadequacies during challenging economic periods.
Local and State Government Cyberattacks Prove that Security is a Necessity
Cyberattacks are a constant threat to organizations of all sizes. State and local governments are no different, having experienced significantly more cyberattacks than they did in previous years, and are at very high risk of bad actors slipping into their networks. To gain a better understanding of the current attack environment and track changes over time in ransomware trends, Aunalytics security partner Sophos commissioned an independent, vendor-agnostic survey of 5,600 IT professionals across multiple industries in mid-sized organizations across 31 countries. While it’s true cyber insurance has been playing a greater role in helping organizations improve their ability to recover from attacks, survey responses clearly indicate that ransomware poses a rising threat to government organizations.
Government Cyberattacks Increase From Previous Years
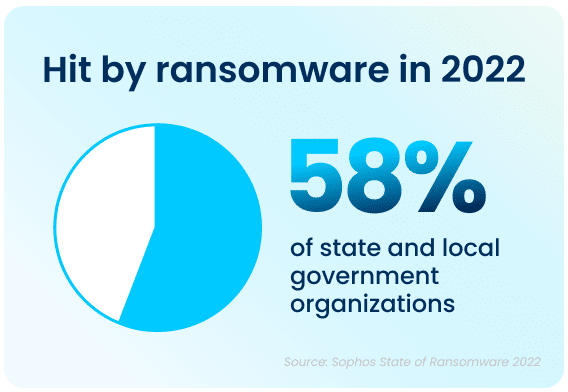
Ransomware attacks have increased significantly over the past year—58% of state and local government organizations surveyed were hit by an attack in 2021, up 70% from 2020. Bad actors are now considerably more capable of attacking organizations and executing harmful tactics at scale. The Ransomware-as-a-Service (RaaS) model is one cause of last year’s increased attacks, as the required skill level for bad actors to hamper the day-to-day operations of an organization has gone down significantly.
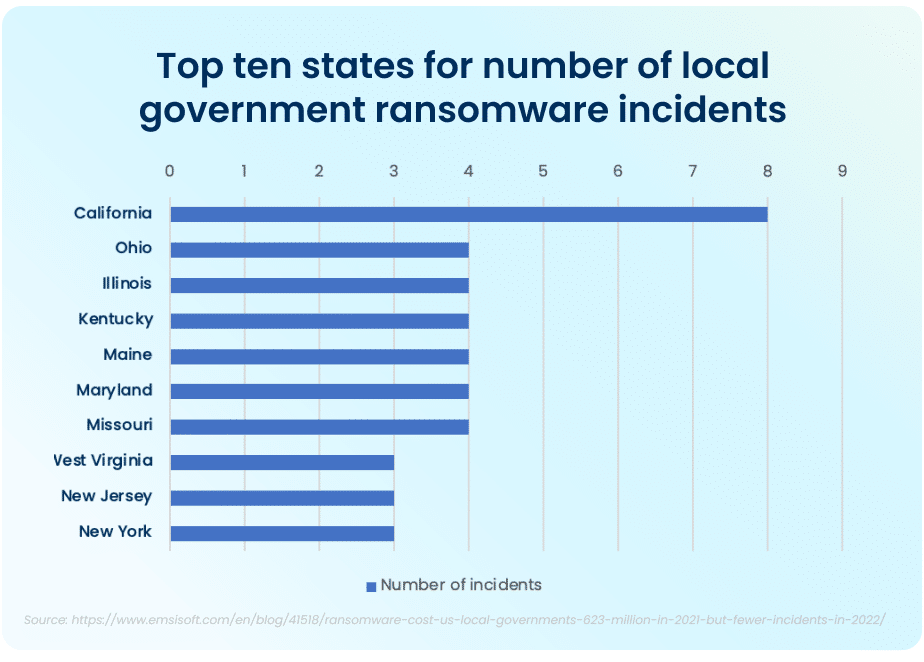
The top ten states that had to deal with the maximum amount of total ransomware attacks in the public sector in 2021 were California, who experienced the most attacks total, Ohio, Illinois, Kentucky, Maine, Maryland, and Missouri. While California took the lion’s share of attacks, with 8 major ransomware incidents, the other six states had four major incidents each.
FBI Cyber Division Survey Lists Examples of Ransomware Attacks
The Federal Bureau of Investigation (FBI) Cyber Division lists examples of several ransomware attacks that impacted state and local government organizations in their 2022 Private Industry Notification. This list contains evidence showing the impact these attacks can have on local communities.
For example, in January 2022, following a ransomware attack, a US county had to take all their systems offline and close all public locations in order to run an emergency response plan and restore all their data from backups. This action disabled all the cameras in the local county jail and deactivated automatic doors, resulting in severe safety concerns and a complete lockdown of the facility. A different county had their data—with residential and personal data—held ransom in an attack. When the ransom was not paid, all of the data was posted on the Dark Web in retaliation.
Rising Complexity of Ransomware Attacks
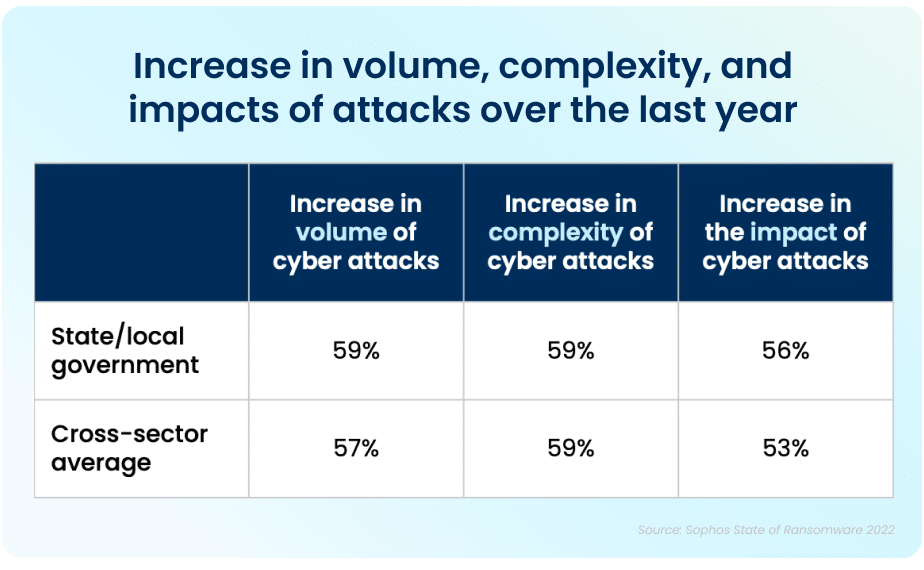
Apart from the rising prevalence of these attacks, the sheer complexity of each attack is also on an upwards trajectory. While the manufacturing and production industry reported the lowest rate of ransomware attacks, over half of all respondents reported their organization was injured by bad actors. The reality is that every organization is at high risk of cyberattack. In 2021, 59% percent of government organizations who experienced cyberattacks saw the complexity of the attacks increase, while a similar 59% saw an increase in the overall volume of cyberattacks.
Data Recovery Rates Are Improving
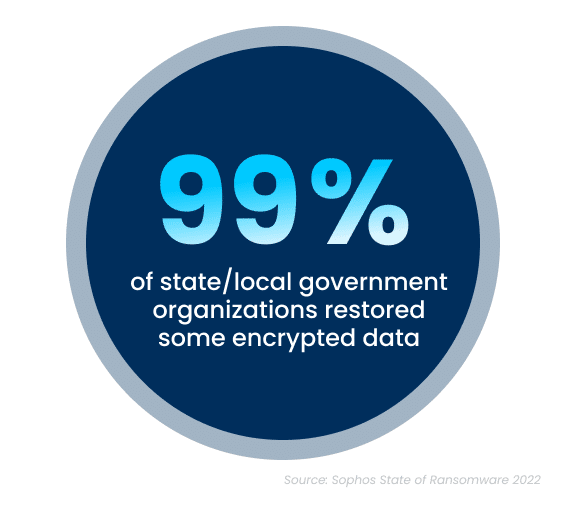
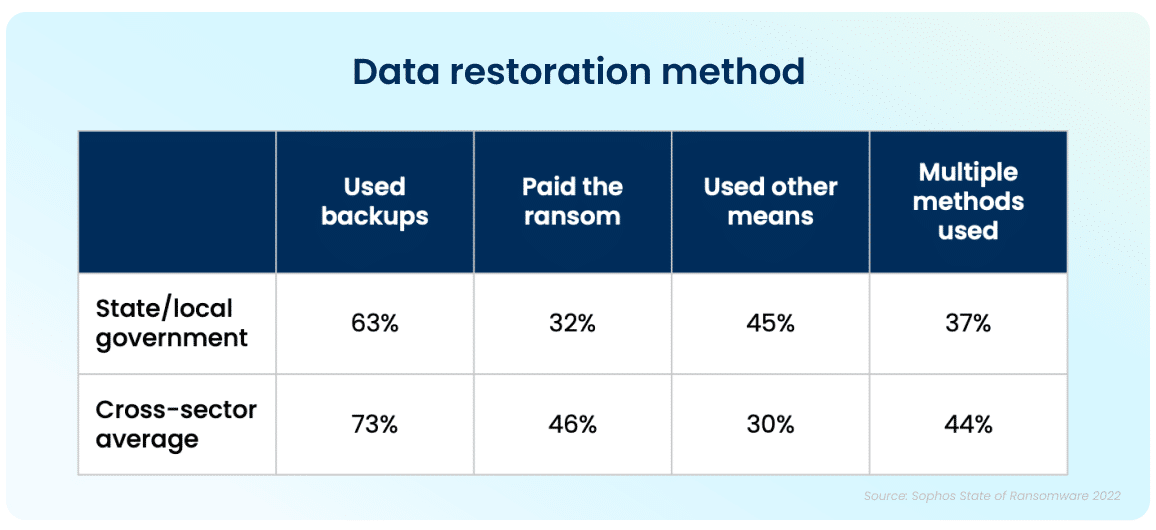
While the increase in cyberattacks paints a bleak picture, there is a silver lining to this dark cloud. Ninety-nine percent of government organizations were able to get at least some of their encrypted data back. The top method used to restore data was performed via existing backups, which were used by 63% of organizations whose data was encrypted in an attack. Unfortunately, despite the utilization of backups, 32% of the affected organizations still had to pay a ransom to ensure that more of their data was restored.
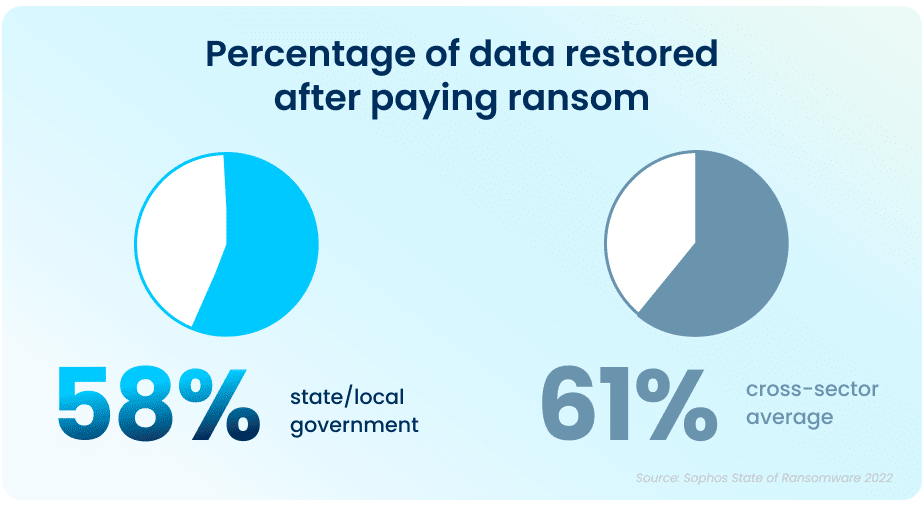
While paying a ransom typically allows organizations to get some data back, it is proving to be less effective than in years past. On average, in 2021, organizations that paid a ransom only got back 58% of their data, a considerable drop from 70% in 2020.
In April and June 2022, respectively, the states of North Carolina and Florida were the first states to prohibit state and local government organizations from paying ransoms to any bad actors. Arizona, Pennsylvania, Texas and New York are considering similar legislation. While the exact impact of this cannot be determined yet, this is expected to dissuade ransomware attacks on all organizations.
This highlights the importance of employing multiple methods to restore data—utilizing backups in particular can improve the speed of recovery and increase the amount of data that can be recovered in the event of an attack.
But It Doesn’t End There
The Sophos State of Ransomware In State and Local Government 2022 survey has revealed that ransomware continues to be an imminent threat for state and local government organizations. For many, choosing to work with an experienced partner with expertise in cybersecurity not only improves your chances of getting approved for the right amount of cyber insurance coverage, but can also ensure that companies see a higher return on investment, and improved ability to both prevent and mitigate attacks in the future. Aunalytics provides Disaster Recovery Services, which is further coupled with a comprehensive backup and archival strategy. This allows state and local government organizations like yours to remain confident so that you are prepared should you encounter a disaster event. We partner with industry leaders to replicate your critical infrastructure so you are prepared for anything.
How An End-to-End Analytics Solution Helps You Avoid Hidden Costs
As the new year approaches, digital transformation should be at the top of every mid-market organization’s to-do list. As organizations begin to understand the value of business analytics for their daily operations, the need for an end-to-end analytics solution becomes evident. Yet, many companies struggle to obtain the right analytics solutions to fit their specific needs.
Unfortunately, the analytics solution market can be difficult to navigate. Since building an analytics tool in-house is incredibly time-consuming and very costly, many mid-market companies would be better served by working with a solution provider who can provide both the tools and talent necessary to achieve their business goals.
Digital Transformation Roadblocks
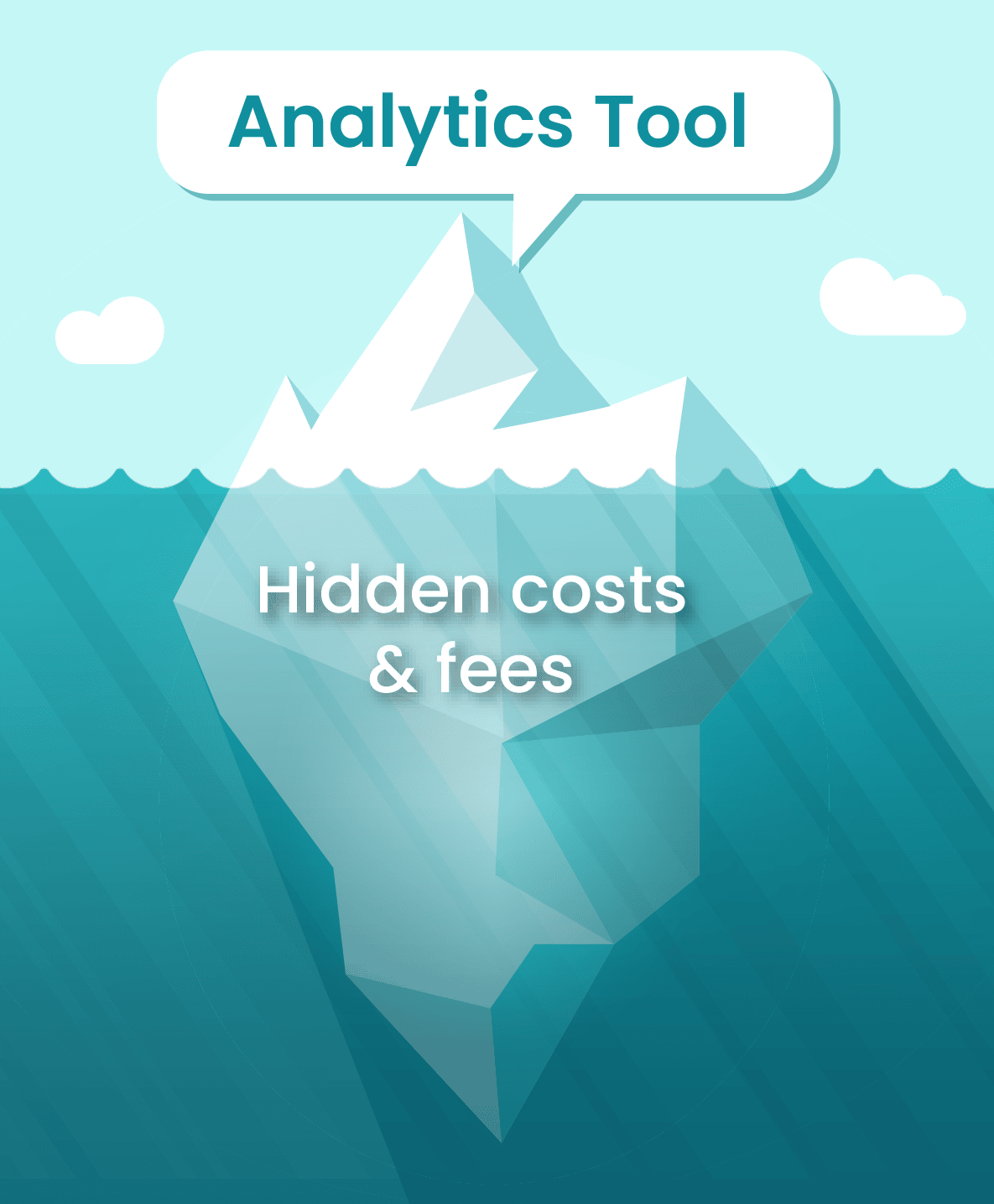
One major roadblock in the pursuit of digital evolution is determining how much an analytics solution is going to cost. Analytics solutions are complex, and when an analytics company gives a quote, they often fail to mention additional add-ons their solution needs to be functional. For instance, charges for a third-party cloud to host your analytics solution and individual charges for connectors that allow your disparate data sources to flow into the solution are the most common up-charges.
Your organization could get stuck with unexpected licensing fees or overage charges from a third-party cloud provider. Worse yet, you may end up piecing together various technologies, while lacking the adequate technical talent to keep the solution functioning and show actionable results. To achieve value from your investment, it is vital to look for a partner that can provide you with a solution where extra charges do not come into play. Budgets are an integral part of the decision-making process when it comes time to choose a solution provider.
With hidden costs, figuring out how a particular solution is going to fit into your budget becomes increasingly difficult. The most effective solution is opting for a partner who can provide your company with an end-to-end analytics solution.
Why Mid-Market Organizations Need End-to-End Analytics Solutions
To compete with larger institutions, mid-market organizations need to leverage their existing local data to gain insights to better serve their clients. An end-to-end solution ensures you do not end up with a solution your team cannot utilize to achieve your business goals and thrive in an increasingly competitive market.
It is a known fact that mid-market businesses struggle with retaining talent for data management, IT, security, and advanced analytics. Opting for an end-to-end solution gives you access to a team of experts who will always be by your side, assisting you every step of the way.
With Aunalytics, you get the technology and the expertise required to complete your journey from disparate data to actionable business results. Using our platform, your entire organization can reap the benefits of having a reliable and robust data platform.
Aunalytics Provides a Complete, End-to-End Analytics Solution for Mid-Sized Organizations
Aunalytics offers an end-to-end analytics solution that includes the right technology paired with experts who work by your side to help you accomplish your business goals. The technology, combined with the technical talent necessary to fully utilize it, will help your organization achieve true value from your investment. End-to-end analytics solutions provide you with insights from your data so you can concentrate on critical business decisions. No longer do you have to worry about overages, licensing costs or other additional charges. Aunalytics has the answers to your business and IT questions.
The Aunalytics Data Platform is a robust, cloud-native data platform built for universal data access, powerful analytics, and AI. It includes the following components:
- Aunalytics Enterprise Cloud provides a highly redundant, secure, and scalable platform for hosting servers, data, analytics, and applications at any performance level.
- Aunsight Golden Record integrates and cleanses siloed data from disparate systems for a single source of accurate business information across your enterprise.
- Daybreak Analytics Database provides daily insights powered by Artificial Intelligence (AI) and Machine Learning (ML) driven analytics, industry intelligence, and smart features that enable a variety of analytics solutions and timely actionable insights that drive strategic value across your company.
This end-to-end platform enables your business to extract answers from your data without having to worry about additional charges that might break your budget. Our solutions are secure, reliable, and scalable, all according to your business’ needs. Aunalytics solutions seamlessly integrate and cleanse your valuable data for accuracy, ensuring data governance and employing Artificial Intelligence (AI) and Machine Learning (ML) driven analytics to glean customer intelligence and timely actionable insights that drive strategic value.
Using our solution, team members across your organization can reap the benefits of having an end-to-end analytics solution to make data-driven decisions. Company executives can view data cleansed into an accurate golden record that is streamed in real-time to enable better decision making for the entire organization. Your organization’s marketing team can have access to aggregated data that reveals a 360-degree view of your customer, including insights into customer behavior, that empowers them to run data-driven campaigns to the right customer, at the right time, with the right product. Your IT department can ensure that you are functioning at peak efficiency by analyzing the data collected to scale resources and identify potential roadblocks and bottlenecks. Those are just a few departments that would benefit—think about how powerful a real-time analytics solution could be across your entire organization.
Ransomware Attacks Pose An Increasing Threat to Businesses of All Sizes: The State of Ransomware 2022
Cyberattacks are a constant threat to organizations of all sizes. To better understand how the current attack environment and track how ransomware trends have changed over time, Sophos commissioned an independent, vendor-agnostic survey of 5,600 IT professional in mid-sized organizations across 31 countries. This survey was conducted in January and early February 2022. The results highlighted the increasing threat that ransomware poses, and the increased role cyber insurance is playing in driving organizations to improve their cyber defenses.
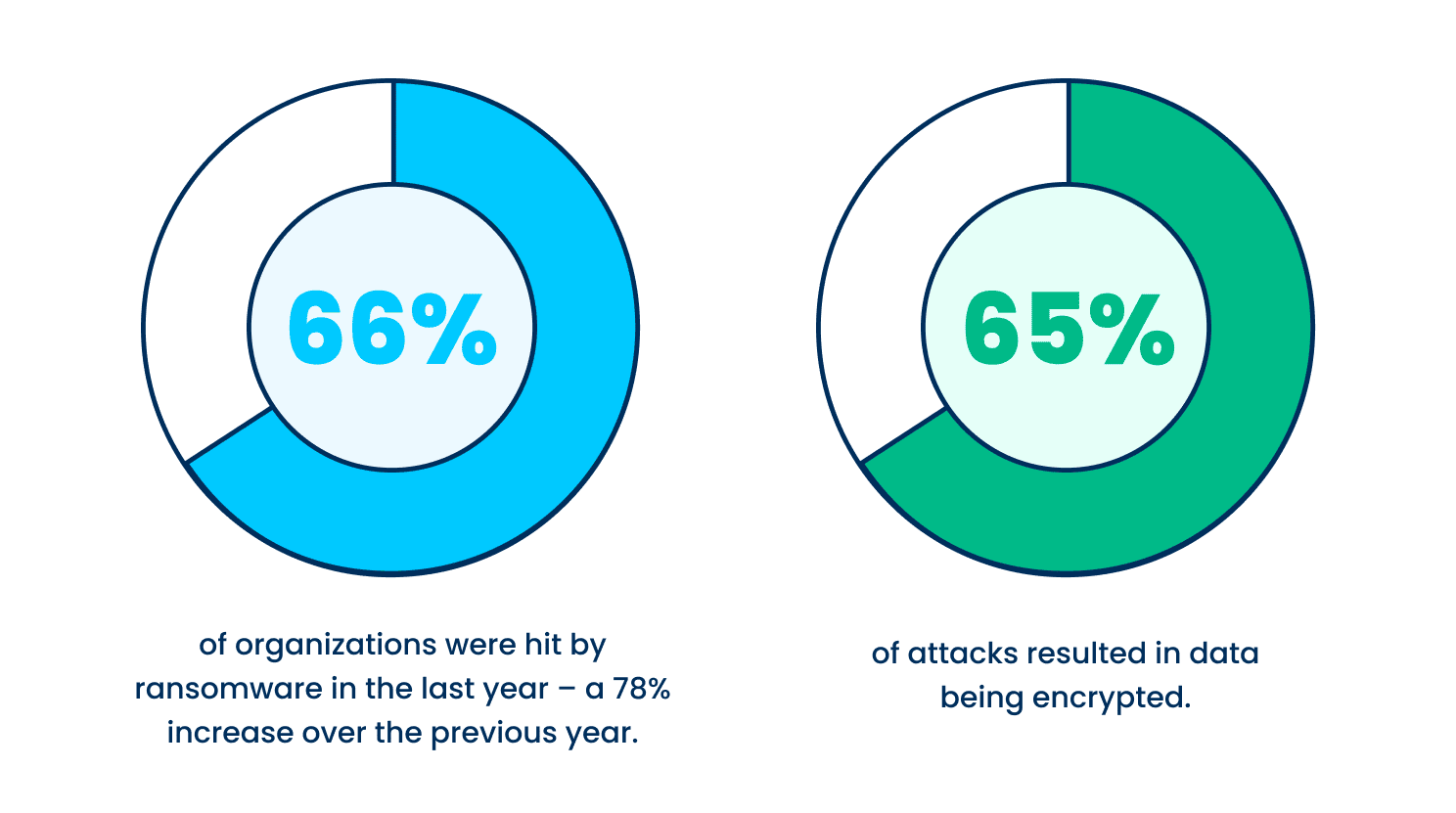
Cyberattacks are up from last year
Ransomware attacks have increased significantly over the past year—66% of organizations surveyed were hit by an attack in 2021, up 78% from the previous year. This is due in part to the ease at which bad actors are able to deploy attacks. The Ransomware-as-a-service mode has reduced the skill level needed to attack.
Not only are attacks more prevalent, but the attacks themselves are becoming more successful and more complex. In 2021, 65% of attacks resulted in data being encrypted, up from 54% in 2020. Fifty-nine percent of organizations who experienced cyberattacks saw the complexity of the attacks increase, while 57% saw an increase in the volume of cyberattacks overall.
Data recovery rates are improving
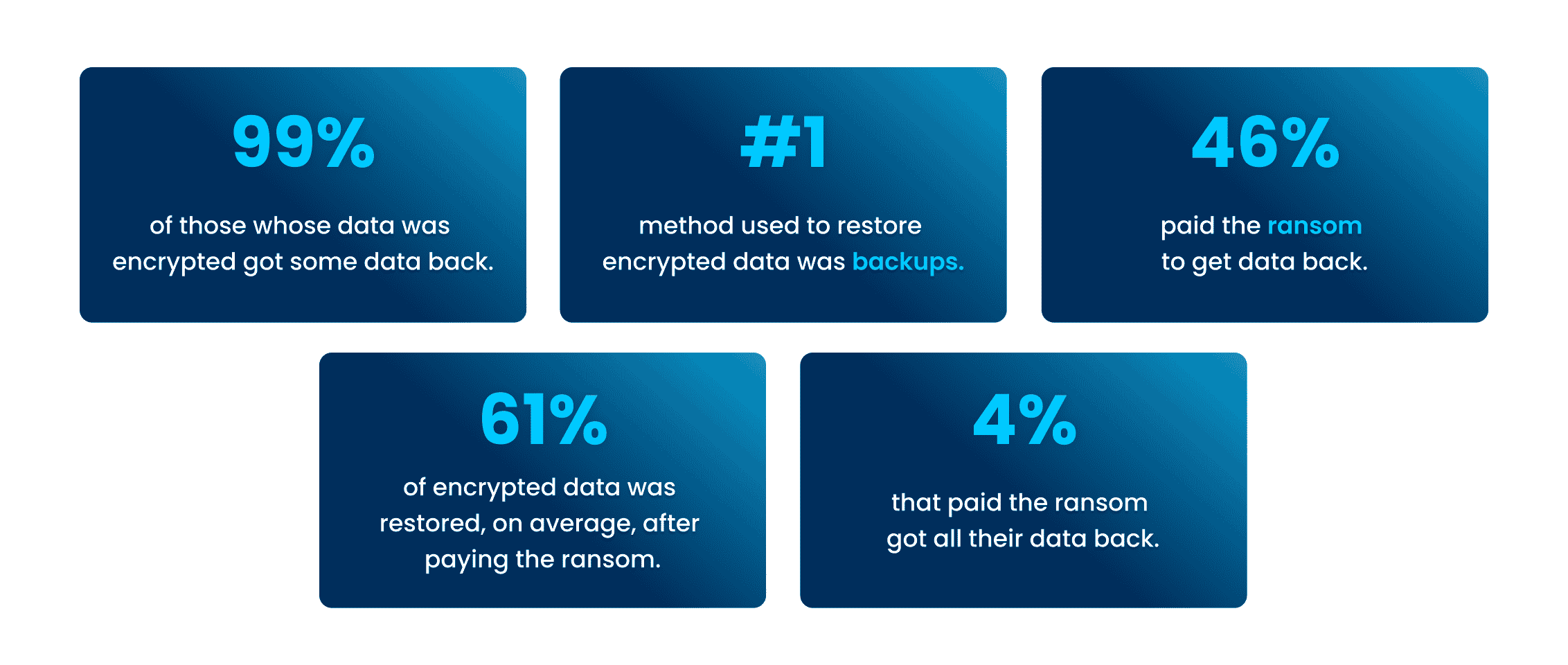
Despite the increase in attacks within the past year, there is some good news. Almost every organization surveyed (99%) were able to get some encrypted data back—up from 96% in 2020. The top method used to restore data was backups, which was used by 73% of organization whose data was encrypted in an attack. In addition to backups, a large portion—forty-six percent—paid a ransom to have their data restored.
Unfortunately, while paying a ransom typically allows organizations to get some data back, it is less effective than in years past at restoring data. On average, organizations that paid a ransom only got back 61% of their data, down from 65% the previous year, while only 4% of those that paid the ransom got ALL their data back in 2021, down from 8% in 2020. This highlights the importance of employing multiple methods to restore data—utilizing backups in particular can improve the speed of recovery and increase the amount of data that can be recovered.
Ransom payments have increased
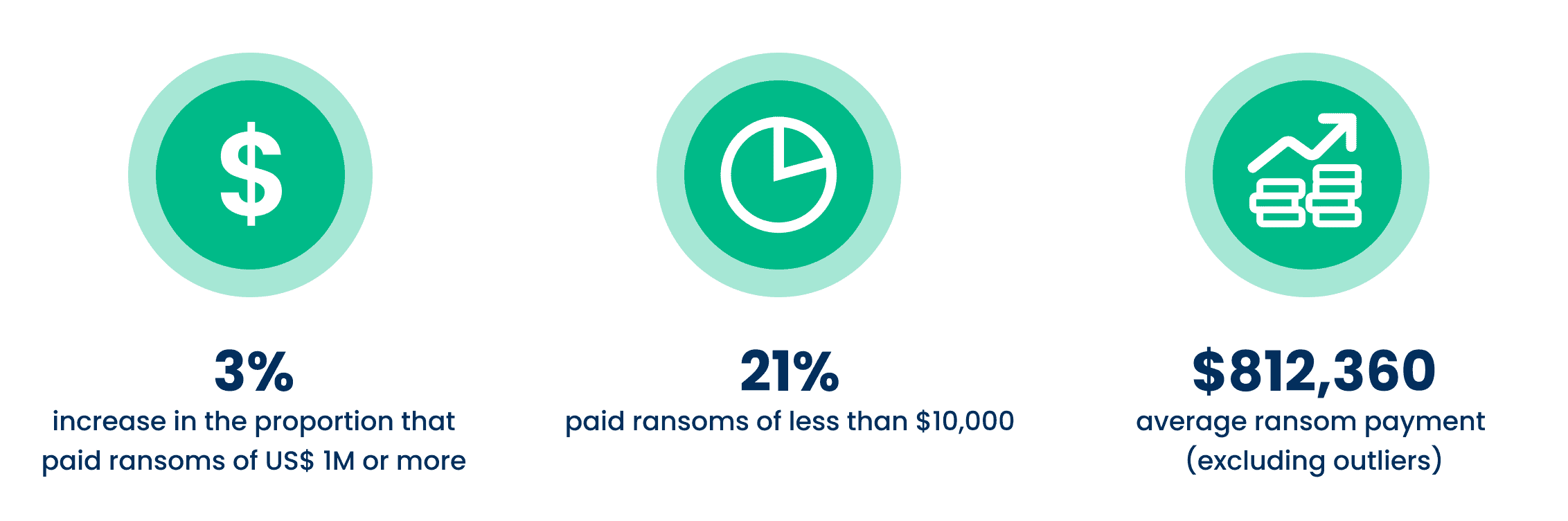
Not only are ransoms less effective at restoring data than in previous years, but the amount of the payments themselves have increased considerably. Between 2020 and 2021 there was a threefold increase in the proportion of victims paying ransoms totaling US$1 million or more. The percentage paying the lowest ransom amounts decreased over that same time—from one in three (34%) to one in five (21%).
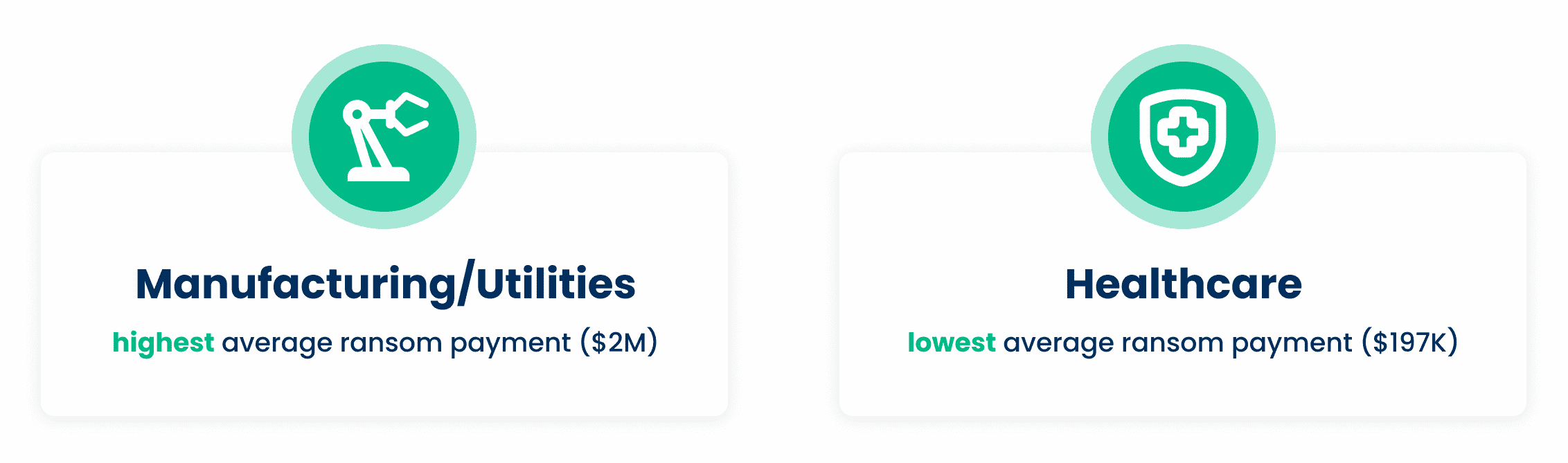
The average ransom payout increased 4.8X from 2020 data, from an average of US$170K to US$812,360 in 2021. However, the average ransom amount varies greatly across industries, with manufacturing and utilities coming in at the top of this survey with an average of US$2.04M and US$2.03M, respectively, while healthcare and local/state government had the lowest average ransom payments at US$197K and US$214K, respectively.
Ransomware greatly impacts companies, both economically and operationally
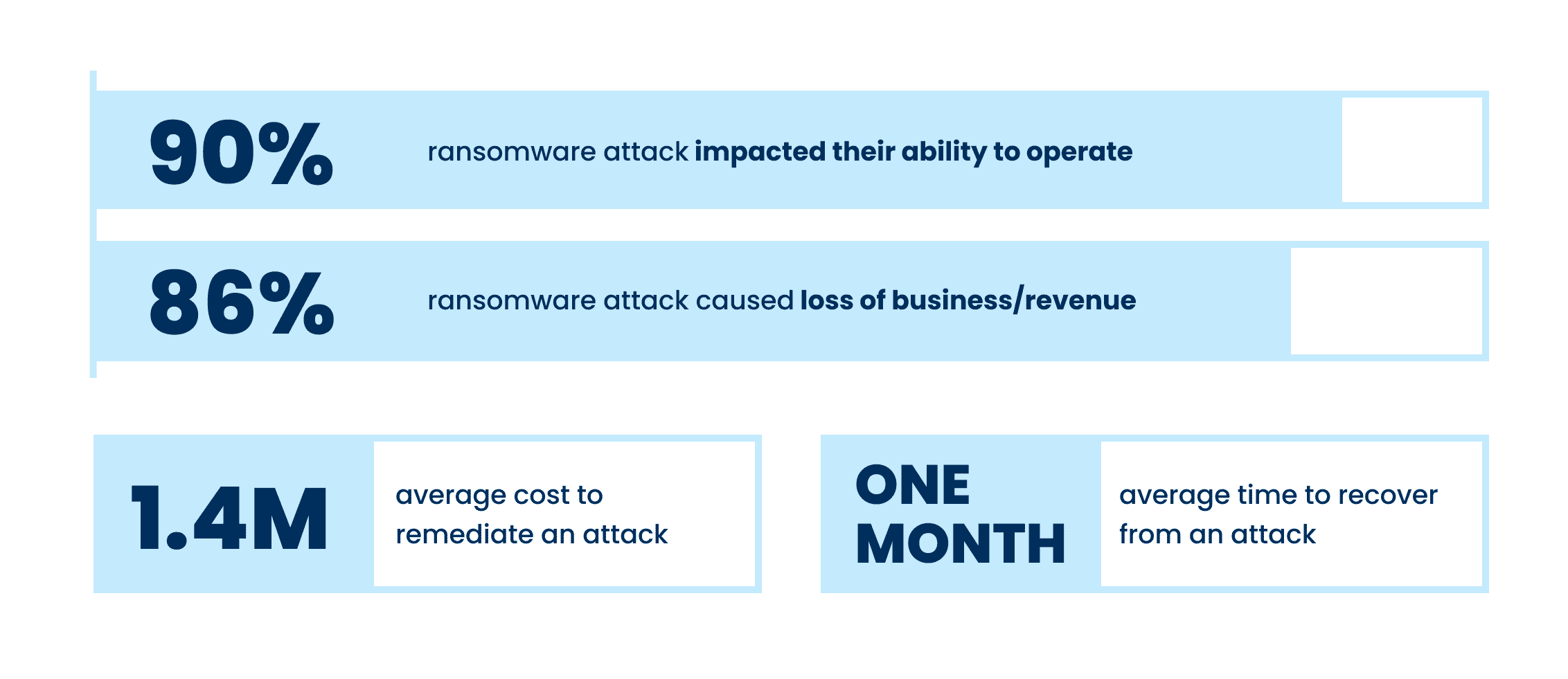
Even when some of all data is able to be restored after a cyber attack, the costs of loss productivity or inability to operate at all can be substantial. Of those hit by ransomware last year, 90% said their most significant attack impacted their ability to operate, while 86% said it caused them to lose business and/or revenue. The average cost to remediate an attack in 2021 was US$1.4M, which, thankfully was down from US$1.85M in 2020. This was due in part to cyber insurance providers being better able to guide victims through an effective response more rapidly.
Although there have been improvements in total recovery time over the years, it still took, on average, one month for organizations to fully recover from the most significant attacks. Those in higher education and central/federal government had the slowest average response times, at around 2-5 months, while manufacturing and financial services were the quickest, with the majority being able to recover in one month or less.
Despite the huge economic costs of ransomware attacks, many organizations are putting their faith in defense that don’t actually prevent ransomware—only more quickly mitigate its effects. Seventy-two percent of organizations in the survey who weren’t hit by ransomware in the past year and didn’t expect to be hit in the future cited backups and cyber insurance as reasons why they don’t anticipate an attack. Neither of these elements actually prevent attacks in the first place.
Simply having security resources in place does not necessary mean that they are effective. Of those surveyed who were hit by ransomware in the last year, 64% said they had more cybersecurity budget than they need, and 24% said they had the right amount of budget. Many of these organization also said they had more headcount or the right amount of headcount (65% and 23%, respectively. This reveals that despite having ample resources—both personnel and technology—organizations will not achieve a high return on investment without a combination of the right technology and expertise to use the technology effectively.
Cyber insurance drives changes to cyber defenses
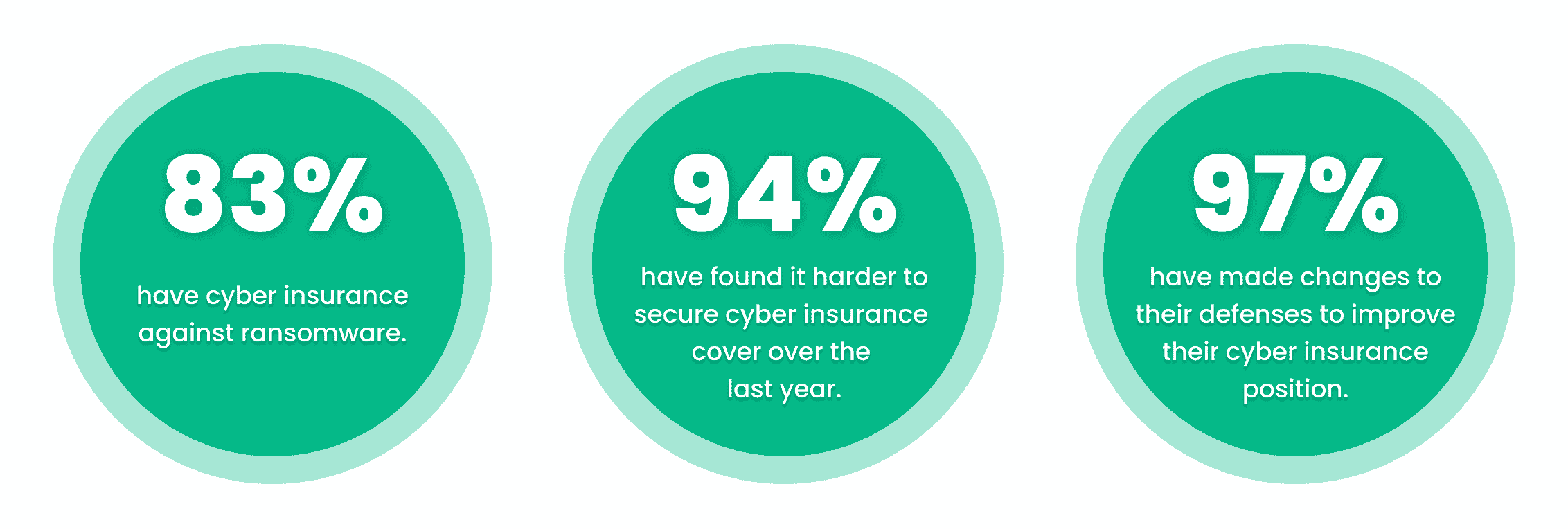
Thankfully, organizations do not have the shoulder the burden of ransomware costs all on their own. The survey found that four in five mid-sized organizations had insurance against ransomware attacks. However, 34% said there were exclusions/exceptions in their polices. Organizations that had been previous hit by ransomware attacks in the past were much more likely to have cyber insurance coverage against ransomware. However, many respondents indicated that securing coverage has changed in the past year, or gotten more difficult to obtain:
- 54% said the level of cybersecurity they need to qualify is now higher
- 47% said policies are now more complex
- 40% said fewer companies offer cyber insurance
- 37% said the process takes longer
- 34% said it is more expensive
As a result, 97% of organizations that have cyber insurance have made changes to their cyber defense to improve their cyber insurance position. 64% have implemented new technologies/services, 56% have increased staff training/education activities, and 52% have changed processes/behaviors.
Conclusion
The survey has revealed that ransomware continues to be an imminent threat for organizations of all sizes across industries. For many, choosing an experienced partner with expertise in cybersecurity not only improve their chances of getting approved for the right amount of cyber insurance coverage, but can ensure that they see an higher return on investment and improved ability to prevent and mitigate attacks in the future.
Government Agencies Need Proactive Security Plans in Place to Defend Against Ransomware
Cyberattacks are increasing across all industries, but for state and local governments and government agencies, the threat is imminent. Attackers are becoming more sophisticated and use a wide variety of tactics to infiltrate organizations. Now, more than ever, a proactive security posture is imperative to avoid the loss of sensitive data and costly downtime.
The Stats
With 58% of local and state governments reporting a ransomware attack within the last year, government agencies became one of the most heavily affected groups – second only to academia – in 2021, according to the FBI.
It’s not cheap when government offices fall victim to a ransomware attack. Often agencies are attacked by complex cyberattacks that are difficult to detect and even more difficult to remove while keeping your data safe and your services uninterrupted.
Ransomware isn’t uncommon, but that doesn’t stop your agency from going down for an extended period of time—downtime that cost local and state government entities an estimated $623,700,000 in 2021, reports EMSISOFT in an August, 2022 article.
The Solution
A Security Operations Center (SOC) is becoming a necessity for government agencies of all levels. With the government sector being a prime target for hackers and cyberattacks, it’s imperative that proactive security is in place to protect your confidential data. With a continually increasing threat landscape, having security that can stand up to the worst of bad actors is a must. An SOC takes care of things for you.
Why an SOC? An SOC can answer threats before they slip into your network and servers—before important data has been stolen by the bad actor. Does your organization have an SOC? If not, your agency is falling behind and your security is not up to date, meaning it may not protect you from all cyberattacks that will try to injure your network.
SOCs can be expensive and complex to build, and even harder to fill with talent. Even with the short supply of talented security engineers, most entities cannot afford to compete with the money big names like Microsoft, Google, and Facebook offer, but it doesn’t mean you should go without an SOC.
Getting Help
FedRAMP certification is a long, difficult process, upon which a service provider becomes an expert in providing a secure platform to manage credentials, vendors, workforce, and more. A FedRAMP certified company can best protect your data and uphold your privacy, security, and confidentiality.
Aunalytics is proud to be one of a select few to be FedRAMP ready certified in the Midwest, meaning we have achieved compliance to meet FedRAMP security standards.
With the security standards that FedRAMP certification requires—and a proven history of working with local governments throughout the Midwest – we have tools and talent to protect your data with the most up to date security practices with our Advanced Security service. With an ever-changing landscape that always includes threats, a trustworthy security partner can help keep your data safe, using 24/7/365 threat and vulnerability scanning, allowing us to find and stop bad actors before they ever access your network.
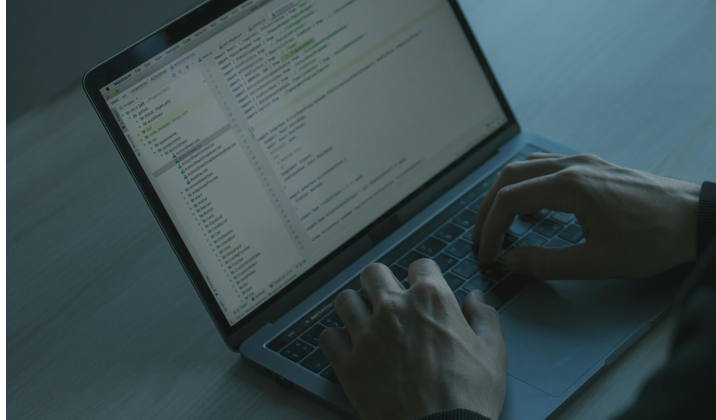
Workstation and Server Patching Allows for Better Security, Helps Curb Cyberattacks
 A “patch” is a set of changes to a computer program designed to update, fix, or improve it. Typically, patches are meant to improve the functionality, performance, or usability of a program. Patches can include everything from bug fixes for glitches in the programming to security patches for vulnerabilities.
A “patch” is a set of changes to a computer program designed to update, fix, or improve it. Typically, patches are meant to improve the functionality, performance, or usability of a program. Patches can include everything from bug fixes for glitches in the programming to security patches for vulnerabilities.
It’s easy for something—or someone—to slip through the cracks in your security. As a result, this leaves your organization vulnerable to attack without the right security patches. In a world where ransomware costs a company an average of $4.54 million per attack—before the cost of paying the ransom—patches are essential to the security of any organization, from midsized companies to large enterprises. Undoubtedly, patches give your network the security it needs most.
Why patch?
Patching ensures your servers and workstations have thorough protection from the latest security threats—stopping threats as they emerge. Therefore, threats that would have taken out your company for an extended period are no longer a concern with proper security patching.
But patching can be difficult to manage, keep track of, and update promptly. Setting up and coordinating manual patching across an organization can feel like a nightmare, taking days to organize, schedule, and execute across your entire company.
Crucial for Company Security
Workstation and server patching is crucial, stopping devastating malware attacks, like WannaCry, in their tracks. McKinsey cites good patch management as a top proactive maintenance measure that can help your organization prevent cyberattacks.
Knowing the priority level for patch installment can be confusing, leading to poor patch management. Therefore, enlisting the help of a partner to employ security patching best-practices can be a boon to many organizations. Since Aunalytics is well-versed on patching, patch installments are timed to avoid as many bugs as possible, and patches are prioritized in order of importance. Patching keeps those who would hurt your business at arm’s length—and with Aunalytics, you don’t have to worry about patching your workstations and servers yourself, you will have a trusted partner to back you up.
We believe security is so important that we embed it into our Advanced Security offering, helping your business thrive at no additional cost to you. Gain peace of mind and eliminate technical worries with Aunalytics.
2022 Mi-GMIS Fall Conference
2022 Mi-GMIS Fall Conference
Boyne Mountain Resort, Boyne Falls, MI
Aunalytics is Proud to Attend the 2022 Mi-GMIS Conference as a Silver Sponsor
Aunalytics is proud to participate in the 2022 Michigan Government Management Information Systems (Mi-GMIS) Conference as a Silver Sponsor. Aunalytics will be sponsoring the Vendor Happy Hour on Monday, September 19th from 4-6pm, and will also be showcasing our Secure Managed Services IT offering as well as our Advanced Security solution at our exhibit booth.

Aunalytics Extends Its Presence in Greater Columbus Area
Leading Data Platform Provider Joins One Columbus Organization to Help Foster Economic Development in the 11-County Region, and Is a Featured Presenter at a Cybersecurity Forum in Sydney on August 19
South Bend, IN (August 17, 2022) - Aunalytics, a leading data platform company delivering Insights-as-a-Service for mid-market businesses, announced today its membership in One Columbus, the economic development organization for the 11-county Columbus, Ohio region. With an office in Bellefontaine, Aunalytics is committed to contributing its resources to foster the economic well-being of the broader Columbus region.
Working with local and state partners, One Columbus serves as the business location resource for companies across Central Ohio and around the world as they grow, innovate, and compete within the global economy. Its mission is to lead a comprehensive regional growth strategy that develops and attracts the world’s most competitive companies, grows a highly adaptive workforce, prepares its communities for the future, and inspires corporate, academic and public innovation throughout the greater Columbus area.
“As with other regions of the country, the organizations in the Greater Columbus area are interested in increasing their competitive advantage through digital transformation,” said Robert Lizotte, Ohio Local Market Leader for Aunalytics. “As a member of One Columbus, we look forward to demonstrating how this shift can be accomplished in a more secure and efficient way to drive a higher return on business initiatives.”
Aunalytics also announced that its Chief Security Officer, Kerry Vickers, will speak in Sydney, Ohio at the Sydney Shelby Chamber of Commerce cybersecurity forum, “Do You Have a Plan?” on August 19, at 8amET. Vickers is one of nine subject matter experts who will outline the threats and the measures that can be taken to mitigate cyber invasions which occur on a daily basis, to organizations large and small.
Tweet this: .@Aunalytics Extends Its Presence in Greater Columbus Area #Cybersecurity #FinancialServices #Banks #CreditUnions #Dataplatform #DataAnalytics #Dataintegration #Dataaccuracy #AdvancedAnalytics #ArtificialIntelligence #AI #Masterdatamanagement #MDM #DataScientist #MachineLearning #ML #DigitalTransformation #FinancialServices
About Aunalytics
Aunalytics is a data platform company delivering answers for your business. Named a Digital Innovator by analyst firm Intellyx, and selected for the prestigious Inc. 5000 list two years in a row, Aunalytics provides Insights-as-a-Service to answer enterprise and mid-sized companies’ most important IT and business questions. The Aunalytics® cloud-native data platform is built for universal data access, advanced analytics and AI while unifying disparate data silos into a single golden record of accurate, actionable business information. Its DaybreakTM industry intelligent data mart combined with the power of the Aunalytics data platform provides industry-specific data models with built-in queries and AI to ensure access to timely, accurate data and answers to critical business and IT questions. Through its side-by-side digital transformation model, Aunalytics provides on-demand scalable access to technology, data science, and AI experts to seamlessly transform customers’ businesses. To learn more contact us at +1 855-799-DATA or visit Aunalytics at https://www.aunalytics.com or on Twitter and LinkedIn.
PR Contact:
Denise Nelson
The Ventana Group for Aunalytics
(925) 858-5198
[email protected]