Don’t Ghost Your Network—Begin Your Security Maturity Journey
Is your security keeping up with the rapidly changing threat landscape? If not, your security is becoming more obsolete by the day—and more vulnerable to scary things like hackers and ransomware by the second. When a company is fully protected with the most up to date hardware, software, monitoring, and consistent patching it begins to reach security maturity.
Security maturity is a consistent state of awareness concerning your network security and can only be achieved when you:
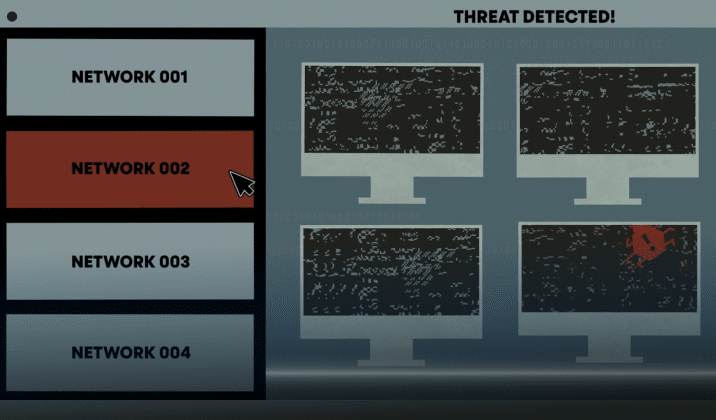
- Have an SOC to monitor and remediate threats
- Have looped vulnerability management
- Employ active defense with security intelligence from multiple sources to protect applications, networks, servers and workstations
- Are willing to adapt your security environment to new and changing threats on a constant basis, and more.

Be Proactive
Instead of relying on a passive security model—or worse, waiting until after a companywide infection—take an active role in your company’s security. The main goal of security maturity is to avoid or reduce the number of security incidents haunting your network. It’s kind of like painting San Francisco’s Golden Gate Bridge. As soon as the painting crew gets from one end to the other with a fresh coat of paint, it is time to start again to repaint the bridge. Security maturity requires constant action and change as your organization adapts to protect against the latest evolving threats.
We all observed remote work access change security and IT on a mass scale in 2020, and security changes continue to become more necessary as bad actors and threats become more and more dangerous to your business as it continues to grow and change—and more dangerous for your customers to do business with you.
October WSJ headlines highlight a Chicago healthcare system, one of the largest in the U.S., being the victim of ransomware that is forcing it to shut down electronic records, systems, and cancel patient appointments. It is now working with law enforcement and outside cybersecurity experts to remediate. A security maturity journey is hard to make on your own, and a good partner can ensure you are meeting the highest security standards possible. Here at Aunalytics, we include security in everything we do because we believe it is a basic building block of IT.
Find A Trusted Security Partner
Without a secure network, you cannot even begin to consider moving further into a security maturity journey. Fortunately, a partner can give you the peace of mind that you will be working with a talented security team that is watching your network 24/7/365, helping to ensure bad actors are caught and eradicated before your company is compromised.
A standard, one size fits all security solution simply doesn’t work anymore—it often leaves cracks, holes, and even chasms for hackers and cyberattacks to slip through. You can improve your journey from cybersecurity to security maturity with a trusted partner.
Click here to learn more.
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Investing in digital transformation technologies can be a waste of money if your company forgets one important point. That point is, no matter how cutting edge the tech or tool may be, people are needed with specific technical expertise in order to derive true business value from these investments.
Unlike large enterprises, mid-market companies often try to find this expertise in their IT manager, hoping a jack-of-all-trades approach will take care of it. This is an unfortunate mistake, since it would require the IT manager to have unusual command over a long laundry list of duties, from data integration, ingestion, and preparation to data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on-premises environments. This is not just a tall order for a mid-market IT manager to pull off, but likely an impossible one.

At the same time, it’s unreasonable to expect that most mid-market firms can hire an entire division of data experts—who each need to be highly compensated—in order to achieve the organization’s digital transformation goals. Even if a mid-market player could afford it—which is unlikely to make economic sense—these talent resources are scarce and in high demand.
If you’re still wondering whether your IT manager’s skill set, leveraged by your in-house IT technicians, can properly run the gamut required to achieve value from your data technology investments, consider that the person in this position would need the ability to master a wide range of skill sets, from cloud architecture, database engineering, and master data management to data quality, data profiling, and data cleansing. More specifically, your IT manager would need to take on five additional specialized roles for technical talent that are critical for achieving value from data technology investments.
These roles are:
Chief Data Officer/Chief Digital Officer
A chief data officer (CDO) is focused on—you got it—data. Most mid-market companies understandably don’t have a CDO, which means they don’t have anyone who assures regulatory compliance for data handling while managing and exploiting information assets, reducing uncertainty and risk, and applying data and analytics to drive cost optimization and revenue objectives. For IT managers to fulfill a CDO role, they’d have to be equipped to bring a global perspective to company data, help their organization gain competitive advantage over peers, and manage data and analytics. They’d also need the ability to secure data, transform it into valuable business information, lead digital transformation initiatives, and use data for growth and operational efficiency.
Cloud Engineer
The primary job of a cloud engineer is to keep cloud data centers operational and secure for ecosystem users to be able to store and access their data. Cloud engineers are experts in minimizing downtime, managing access to data, managing compute and storage, and setting up cloud architectures for clients, tenants, and containers. They also monitor data center hardware, servers, networks, and communications systems for operational continuity and efficiency.
Data Security Expert
Mid-market firms also need a way to channel the talents of a data security expert, CISO, or cybersecurity director to ensure cyber-security for the company’s data. Data security experts must keep current on emerging threats while executing data security strategies to fend off and remediate attacks. This involves a wide range of duties, including working closely with the IT team to run the company’s Security Operations Center (SOC), constantly monitoring servers, networks, and workstations for security threats, and staying up to date on the changing compliance laws and regulations for the business, to name a few. While larger IT teams have bandwidth to fill cybersecurity needs inhouse, many midmarket IT teams do not have capacity for the 24/7/365 monitoring and security edits needed to thwart attacks, let alone bandwidth for executing on mitigation and response strategies needed to overcome them.
Data Engineer
A data engineer’s primary job is to prepare data for analysis or operational uses, which involves integrating data from different sources, as well as implementing and executing data profiling, cleansing, transforming, and normalizing data. Data engineers also work with data in motion and use master data management to ensure data consistency across an organization. Finally, a data engineer is your go-to technical resource for database construction and management, helping to optimize the company’s data ecosystem.
Data Scientist
It should be clear now why a mid-market IT manager should not be expected to take on these additional professional roles, but in case there’s any doubt, keep in mind that a data scientist is also needed. Data scientists develop algorithms and leverage deep learning models to analyze data with artificial intelligence and machine learning. The data scientist creates the “brain” of the data analytics solution to position it for providing accurate answers based on business information. Data scientists also mine data to find opportunities for business growth and efficiency. Ideally, the data scientist uses tools that enable non-technical business users to query data sets without having to write SQL or other code.
Master of One
If you’ve correctly determined that your mid-market IT department does not have enough time to absorb these data roles into their regular duties of keeping your company systems stable and responding to help desk tickets from your team, don’t despair. There’s a viable solution for mid-market businesses with this dilemma: they can partner with data experts who provide a side-by-side model coupling technology with talent. This allows the mid-market to efficiently compete, leveraging the necessary skillsets to achieve digital transformation success.
What does successful mid-market digital transformation require? The key is to have a cloud-based data center, a cloud native data management platform, and cloud native analytics, thus shifting the burden of procuring and maintaining the infrastructure to a third-party vendor in the data industry. Instead of attempting to reinvent the wheel in house, mid-market players should ensure they’re partnered with the right infrastructure to maximize the data-center capabilities, and data storage and management, for effective digital transformation.
Mid-market firms can gain the benefits of working with a wide range of experts including cloud engineers, data engineers, security experts, data scientists, and other highly skilled technical resources if they establish a partnership with a data platform company. By opting for this type of side-by-side expert help, the mid-market can achieve true business value—without needing to hire an entire data team.
Bridging the Mid-Market Talent Gap for Digital Transformation
Bridging the Mid-Market Talent Gap for Digital Transformation
To achieve business value from data technology investments, mid-market companies need the right technical expertise and talent. Yet many mid-market firms push this onto their IT manager, assuming that since it is technology related, IT has it. This is a mistake because most IT departments do not have time for data analytics. They are busy full time keeping company systems stable and secure, and providing support to your team members. This by necessity results in IT deprioritizing data queries over crucial cybersecurity attack prevention. Business analysts and executives get frustrated waiting for data query results, and the data is stale or the business opportunity has passed by the time query results are in.

But even if your IT team had time for it, it still is a mistake to rely on traditional technology administrators for data analytics success. This is unless your IT department has expertise across a wide range of skill sets, from cloud architecture, database engineering, master data management, data quality, data profiling, and data cleansing. What’s more, your IT manager would need to have command over data integration, data ingestion, data preparation, data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on premises environments.
When you read this laundry list of needs, it becomes clear that most mid-market IT departments lack the specialized experts needed to derive business value from their data. Unlike larger enterprises that have the resources to hire skilled staff for these roles, the mid midsize organization requires another option that provides access to the right tools, resources, and support. One that integrates, enriches and is trained in utilizing AI, machine learning, and predictive analytics to achieve more useful results.

To read more, please fill out the form below:
Bridging the Mid-Market Talent Gap for Digital Transformation
Bridging the Mid-Market Talent Gap for Digital Transformation
To achieve business value from data technology investments, mid-market companies need the right technical expertise and talent. Yet many mid-market firms push this onto their IT manager, assuming that since it is technology related, IT has it. This is a mistake because most IT departments do not have time for data analytics. They are busy full time keeping company systems stable and secure, and providing support to your team members. This by necessity results in IT deprioritizing data queries over crucial cybersecurity attack prevention. Business analysts and executives get frustrated waiting for data query results, and the data is stale or the business opportunity has passed by the time query results are in.

But even if your IT team had time for it, it still is a mistake to rely on traditional technology administrators for data analytics success. This is unless your IT department has expertise across a wide range of skill sets, from cloud architecture, database engineering, master data management, data quality, data profiling, and data cleansing. What’s more, your IT manager would need to have command over data integration, data ingestion, data preparation, data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on premises environments.
When you read this laundry list of needs, it becomes clear that most mid-market IT departments lack the specialized experts needed to derive business value from their data. Unlike larger enterprises that have the resources to hire skilled staff for these roles, the midsize organization requires another option that provides access to the right tools, resources, and support. One that integrates, enriches and is trained in utilizing AI, machine learning, and predictive analytics to achieve more useful results.
Achieving Digital Transformation
Digital transformation has been defined by some as the integration of digital technology into all areas of a business, fundamentally changing how employees operate and deliver value to customers. Some of the challenges midsize businesses have with building an internal team to initiate this concept are employee pushback, lack of expertise to lead digitization initiatives, improper organizational structure, the absence of a digitization strategy and limited budget. As an alternative to building an internal operation, a more efficient way for mid-market businesses is to leverage the skillsets of experts by partnering with a consolidated group of experts, leveraging a side-by-side model that couples technology with talent. Look for solution providers that offer the following:
- Powerful cloud data centers paired with engineers skilled in architecting cloud-based applications and processes that better serve critical business requirements. These data centers are optimized for true multi-tenancy, built on seamlessly integrated hardware and software, offer business-driven configurability, world-class security and performant systems.
- Active Monitoring and Thoroughly Integrated Security. Monitoring and security should be pervasive across system infrastructure to defend against cyberattacks and provide remediation when required. Business customers will also expect full-time monitoring and on-demand help desk to address unexpected events. The data management platform underpinning applications should be monitored by experienced data engineers with success in building data warehouses, data lakes, and data pipes. They should also be able to integrate, cleanse, and transform data into decision-ready and analytics-ready business information.
- High ROI Business Insights that Drive Results. Data analytics investments need to provide real business value by giving actionable insights and finding opportunities within your data. With this in mind, data analytics should include access to data scientists and business analysts versed in your industry. These experts should be equipped to design AI-powered algorithms that answer the most pressing questions based on real-world business challenges.
Mid-Market Data Transformation for Enterprise-Class Results
Ensuring the right mix of hardware, software and resulting services are available to maximize the data center capabilities—and their ability to manage and protect data—is crucial to effective mid-market digital transformation. To compete and drive value, the cloud data center provider must deliver at all levels, with customizable business intelligence solutions powered by an effective data management platform that is secure and compliant. Successful mid-market digital transformation thus requires a shift of responsibilities for infrastructure procurement and maintenance to a third-party provider backed by experienced staff and best-in-class infrastructure.
When implementing a digital transformation project, your company gains from the many benefits this brings, such as a higher return on your IT investment, increased employee and customer experience, and greater business agility. This is further enhanced by leveraging experienced cloud engineers, data engineers, security experts, data scientists, and other highly skilled technical resources—achieving true business value from the investment. And by partnering with experts, your company’s time, resources, and innovation can be focused on its core competencies.
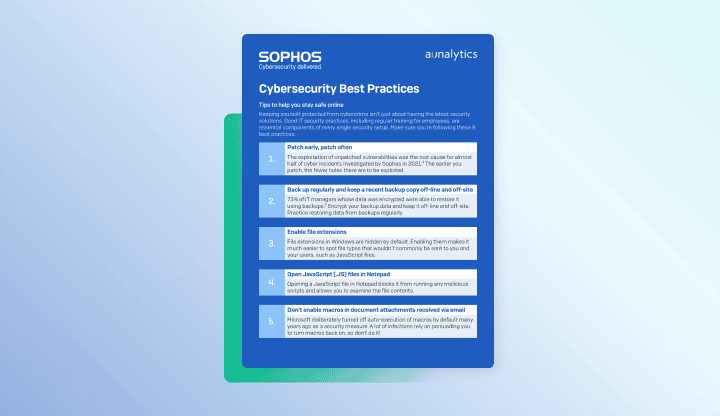
Cybersecurity Best Practices - PDF
Cybersecurity Best Practices
Tips to help you stay safe online
Best Practices for Securing Your Network from Ransomware - PDF
Best Practices for Securing Your Network from Ransomware
Elevate your protection against ransomware and other network attacks
Cybersecurity for you - PDF
Cybersecurity for you
Enterprise-class IT protection for the small- to mid-size company