Aunalytics Brings Its Portfolio of Managed Services, Enterprise Cloud, and Data Cleansing Solutions to Taste of IT Conference in Ohio
Leading Data Management and Analytics Company to Join More Than 400 IT Professionals for a Day of Networking and Learning
South Bend, IN (November 15, 2022) – Aunalytics, a leading data management and analytics company delivering Insights-as-a-Service for mid-market businesses, will feature its managed services, enterprise cloud, and data cleansing portfolio at the Taste of IT Conference on November 16, 2022. The one-day event, which will be attended by more than 400 IT professionals, will be held at the Sinclair Conference Center in Dayton, Ohio.
Aunalytics provides IT and security expertise to mid-market businesses in the areas of financial services, healthcare, manufacturing and professional services. The company’s Secure Managed Services offering combines mission critical IT services leveraging zero-trust end-to-end security to ensure data is protected regardless of a user’s location. Aunalytics provides managed components that offer stability and security, and its next-generation managed services offering is powered by a data platform that provides data-driven IT answers and embedded security that focuses on people and access.
The full suite of managed IT and integrated security services empowers businesses with a complete, all-encompassing approach that includes 24/7/365 monitoring and management, a synchronized network security platform, workstation and server patching, internet protection, email filtering and security, Office 365 management and security, multi-factor authentication, data and device encryption management, and security awareness training.
The company delivers advanced security for defending against modern threats through a team of engineers and analysts with expert skills and toolsets and, in regulated industries, Aunalytics provides the additional technology and controls required to manage risk. Its team of experts is dedicated to analyzing ever-changing rules and regulations and helping users to create processes and policies for data protection and meet compliance requirements within those industries that are regulated.
Aunalytics’ Enterprise Cloud offering is comprised of infrastructure solutions that provide a highly redundant and scalable platform for hosting servers, data, analytics and applications at any performance level. With the Aunalytics® Cloud Storage and Compute solution, users are assured the highest levels of security, accessibility, expertise, scalability, and savings. Aunalytics’ data centers, located in Northern Indiana and Southwest Michigan, meet the most rigorous standards for security, weather protection, temperature and humidity controls, fire suppression and more.
As data continues to expand exponentially, the challenge of data cleansing is rapidly becoming more difficult, as well as expensive. Aunalytics’ Aunsight™ Golden Record turns siloed data from disparate systems into a single source of truth across the organization. Powered with data accuracy, the cloud-native platform cleanses data to reduce errors, and Golden Record as a Service matches and merges data together into a single source of accurate business information, giving users access to consistent, trusted data across the organization in real-time. With this self-service offering, users can unify all their data to ensure enterprise-wide consistency and better decision making.
“IT executives want practical, real-world knowledge about business changing technology and management solutions that are absolutely critical to drive their businesses forward,” said Robert Lizotte, Local Market Leader, Columbus Region, Aunalytics. “As digital transformation continues to be a high priority for many organizations, our portfolio of managed services, enterprise cloud, and data cleansing solutions provides the tools they need to accelerate their digital transformation journeys. We look forward to participating at a Taste of IT and demonstrating how Aunalytics can help IT professionals advance their business success.”
Tweet this: .@Aunalytics Brings Its Portfolio of Managed Services, Enterprise Cloud, and Data Cleansing Solutions to Taste of IT Conference in Ohio #ToIT22 #Datamanagement #Informationtechnology #Managedservices #Enterprisecloud #Datacleansing #Dataplatform #Dataintegration #Dataaccuracy #Digitaltransformation #ITsecurity #Securitytechnology
About Aunalytics
Aunalytics is a leading data management and analytics company delivering Insights-as-a-Service for mid-sized businesses and enterprises. Selected for the prestigious Inc. 5000 list for two consecutive years as one of the nation’s fastest growing companies, Aunalytics offers managed IT services and managed analytics services, private cloud services, and a private cloud-native data platform for data management and analytics. Aunalytics’ data management platform is built for universal data access, advanced analytics and AI – unifying distributed data silos into a single source of truth for highly accurate, actionable business information. Its DaybreakTM industry intelligent data mart combined with the power of the Aunalytics data platform provides industry-specific data models with built-in queries and AI for accurate mission-critical insights. To solve the talent gap that so many mid-sized businesses and enterprises located in secondary markets face, Aunalytics’ side-by-side digital transformation model provides the technical talent needed for data management and analytics success in addition to its innovative technologies and tools. To learn more contact us at +1 855-799-DATA or visit Aunalytics at https://www.aunalytics.com or on Twitter and LinkedIn.
PR Contact:
Denise Nelson
The Ventana Group for Aunalytics
(925) 858-5198
dnelson@theventanagroup.com
Cloud or On-Prem Servers—Which Is Better for Your Company?
Every organization needs to manage its data to get its desired business outcomes. For a company to access its data and use it in day-to-day operations, dashboards, reporting, and data analytics, it either needs a cloud or on-premises solution to facilitate compute, storage, and data management strategies.
What’s The Difference Between The Cloud And On-Premises Data Storage?
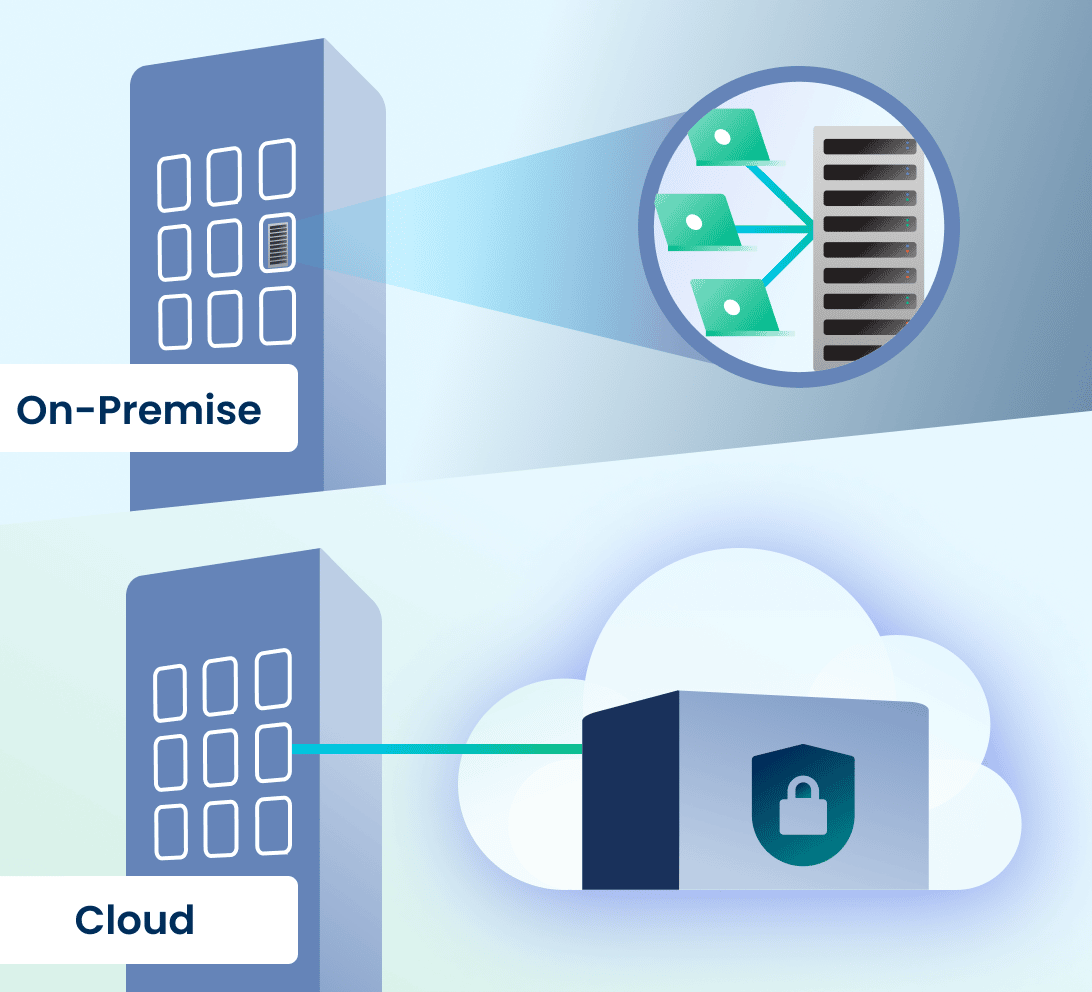
An on-premises data server is hardware that you maintain on your company’s premises for storing, processing, and accessing information through your organization’s networks. An in-house IT department is needed to maintain, turn over/replace, and upgrade the hardware, keep it stable and operational, and secure it.
A cloud storage solution run by an expert and backed by a cutting-edge data center provides the same functions as an on-premises server and more. It does not exist on your company’s premises and the data on it is accessed through the internet. All updates and maintenance tasks are performed by the cloud provider, who owns and operates its own hyper-secure data centers to safeguard your data in case of failure, cyberattack, or outage. Like on-premises servers, access to cloud data can be set by administrators to be permission-based to allow access only by authorized personnel.
On-Premises vs. Cloud—Which Option Best Suits Modern Business Needs?
There are more factors when choosing between using a cloud computing solution or keeping servers on-premises, including customizability and scalability, security concerns, and the budget for your organization’s data management strategy. While on-premises data servers regularly require hardware upgrades in your physical locations to expand alongside your business’s growing needs, a cloud storage and computing solution with access to highly advanced data centers is scalable based upon your workload. Unlike an on-premises server that can take a lot of time and money to set up and ready for operation, cloud service providers ensure you can access your cloud for computing and storage needs almost instantly.
In some mid-sized companies, server rooms tend to be used for multiple purposes, which means that they are sometimes unlocked, unsecured, and allow for unauthorized access that compromises data security. Many mid-sized companies do not have 24/7/365 monitoring of their server rooms, specialized climate controls needed for a data center, and do not consistently deploy or regularly schedule hardware upgrades to keep the systems reliable before something goes down.
One mid-market employee shares the story of a server closet that her company had in a previous workplace. For starters, it could be accessed by nearly every employee of the company. She recounted that the IT department placed portable dehumidifiers in the room to keep moisture down. The IT department’s regular practice was to empty the server closet dehumidifiers in the office’s kitchen sink. Unfortunately, a new IT employee happened to trip while carrying one of the dehumidifiers and spilled water all over the server room. Every employee of the company was affected—they found out that the work they had done since the last backup, which happened to be 5 days ago, had disappeared. Even worse, their servers were down for several days after the incident, further impacting their daily business operations.
Although in the past, people feared that cloud would not be secure, or a company would lose control over its data—cloud has proven to be more secure than on-premises hardware. First, cloud vendors host their own data centers and because this is their main business, they have cutting-edge climate control environments to protect their clients’ data. Cloud vendors adhere to frequent hardware replacement turn-over schedules to keep uptime maximized and cloud operations state-of-the-art. Cloud vendors monitor their data centers 24/7/365, are security experts, and have strict controls in place in order to service clients in highly regulated industries with rigorous data security needs. For most mid-sized businesses, it is more cost effective to rely upon the expertise of a cloud vendor for data security and uptime than to host and maintain its own servers, stay on top of the latest security threats, and staff its data center (or data closet) for monitoring to prevent downtime and security breaches.
Large enterprises often can afford to build their own data centers providing them an alternative to an external cloud provider. However, this is incredibly expensive and can set organizations back by USD $10-25 million on yearly setup and operation costs. This infrastructure also takes a lot of time to be implemented and in today’s fast-paced business environment, this might not be entirely acceptable for decision-makers.
Yet, even for enterprises, on-premises solutions no longer make the most sense. Most modern business applications are cloud-native. Cutting-edge data analytics solutions are cloud-native and connect and integrate data sources using cloud technologies. Clouds are better suited for analytics than on-premises hardware, due to scalability and ability to absorb compute spikes (instead of having to invest in hardware with capacity for compute spikes as machine learning algorithms converge—which leads to excess capacity at other times).
According to Insights for Professionals, 63% of senior IT leaders and company executives who were surveyed expected to invest in cloud infrastructure-as-a-service in 2022. Considering the state of on-premises servers, which are becoming an obsolete technology that require an IT department to keep a constant eye on it, cloud technology is a natural progression in infrastructure for better data management. Gartner reports by 2025 almost 85% of companies will have moved to a cloud-first approach. Cloud technology has now evolved to a point where it provides better stability and security at a more economical price than on-premises solutions.
Mid-Market Company Considerations
Many organizations are operating in hybrid and multi-cloud environments. This means that they have some data in on-site servers, some data in cloud based line of business applications (relying on the application provider for data storage in whichever cloud the application vendor uses for its product), and many have some data in a public cloud.
However, mid-market companies have added considerations when choosing a cloud solution. Most public cloud service providers do not offer data management services. You need to do this yourself. Yet, mid-market companies often do not have this expert talent in-house. For success, mid-market companies need a cloud hyper-scaler that also provides data engineering services to build data connectors and pipelines, warehouses, data lakes, and the like. This skill set is different from a typical IT employee. Hyper-scalers—who can help organizations with data management, transform data from disparate sources into a decision and analytics-ready status, and bring transactional data into the forefront using a cost-effective cloud solution—tend to be private cloud vendors. For this reason, private cloud solutions make more sense than public cloud for mid-sized organizations.

A side-by-side partnership with an experienced cloud-native data platform company will have a measurable and positive impact on mid-market company data management strategies, with built-in access to technical resources and experts, so that your company does not need to hire new FTEs to support data management. Rely on the data management companies for data management so that your company can focus on your main line of business.
Aunalytics’ high performance private cloud provides a highly redundant and scalable platform for hosting servers, data, analytics, and applications at any performance level. Aunalytics delivers data management in a side-by-side service model, bringing companies the technology and the talent needed for data management success. To learn more about our Enterprise Cloud solution, click here.
Don’t Ghost Your Network—Begin Your Security Maturity Journey
Is your security keeping up with the rapidly changing threat landscape? If not, your security is becoming more obsolete by the day—and more vulnerable to scary things like hackers and ransomware by the second. When a company is fully protected with the most up to date hardware, software, monitoring, and consistent patching it begins to reach security maturity.
Security maturity is a consistent state of awareness concerning your network security and can only be achieved when you:
- Have an SOC to monitor and remediate threats
- Have looped vulnerability management
- Employ active defense with security intelligence from multiple sources to protect applications, networks, servers and workstations
- Are willing to adapt your security environment to new and changing threats on a constant basis, and more.

Be Proactive
Instead of relying on a passive security model—or worse, waiting until after a companywide infection—take an active role in your company’s security. The main goal of security maturity is to avoid or reduce the number of security incidents haunting your network. It’s kind of like painting San Francisco’s Golden Gate Bridge. As soon as the painting crew gets from one end to the other with a fresh coat of paint, it is time to start again to repaint the bridge. Security maturity requires constant action and change as your organization adapts to protect against the latest evolving threats.
We all observed remote work access change security and IT on a mass scale in 2020, and security changes continue to become more necessary as bad actors and threats become more and more dangerous to your business as it continues to grow and change—and more dangerous for your customers to do business with you.
October WSJ headlines highlight a Chicago healthcare system, one of the largest in the U.S., being the victim of ransomware that is forcing it to shut down electronic records, systems, and cancel patient appointments. It is now working with law enforcement and outside cybersecurity experts to remediate. A security maturity journey is hard to make on your own, and a good partner can ensure you are meeting the highest security standards possible. Here at Aunalytics, we include security in everything we do because we believe it is a basic building block of IT.
Find A Trusted Security Partner
Without a secure network, you cannot even begin to consider moving further into a security maturity journey. Fortunately, a partner can give you the peace of mind that you will be working with a talented security team that is watching your network 24/7/365, helping to ensure bad actors are caught and eradicated before your company is compromised.
A standard, one size fits all security solution simply doesn’t work anymore—it often leaves cracks, holes, and even chasms for hackers and cyberattacks to slip through. You can improve your journey from cybersecurity to security maturity with a trusted partner.
Click here to learn more.
Aunalytics Highlights Security Priorities as Cybersecurity Awareness Month Concludes
Company Recommends Cybersecurity Solutions to Better Protect Organizations Against High-Risk Cyber Attacks
South Bend, IN (October 28, 2022) – Aunalytics, a leading data management and analytics company delivering managed IT and data platform services for mid-sized and enterprise businesses, today highlighted top security priorities to follow when reinforcing defensive security strategies against malicious cyber threats. The guidance is provided as Cybersecurity Awareness Month comes to a close in October, after a month of focus on the subject.
According to Check Point Research (CPR), “2022 began with a massive exploitation of one of the most serious vulnerabilities on the internet, the Apache log4j, and continued with full blown cyber warfare from the Russia-Ukraine war. The second quarter of 2022 saw an all-time peak, where global cyber-attacks increased by 32%, compared to Q2 2021. The average weekly attacks per organization worldwide reached a peak of 1.2K attacks.”
In response to the rising number of attacks, Aunalytics is providing guidance and solutions to strengthen, educate and defend business IT systems and data from attack. These include having a comprehensive Vulnerability Management (VM) solution, Security Awareness Training, and beginning a Security Maturity Journey – all backed by Aunalytics’ expert cybersecurity team.
Aunalytics cybersecurity solutions experts recommend the following:
- Vulnerability Management (VM) – Replaces manual efforts to protect the network from bad actors using high quality equipment and tools that are typically limited to enterprise organizations. Without a VM solution in place, it is exceedingly difficult to find individuals who have slipped into the network. A VM solution is overseen by security professionals and discovers devices on a network, determines if they are vulnerable and fixes any underlying issues, while concurrently protecting the network as fixes are implemented.
- Security Awareness Training – Security management and training are crucial for businesses to avoid digital disasters. Security awareness training is necessary to educate employees about the digital dangers in their environment and how to properly deal with them. Aunalytics provides expert knowledge and toolsets that employees need in order to better protect the organization.
- Security Maturity Journey – If system security is not keeping up with the rapidly changing threat landscape, it will become obsolete and more vulnerable to bad actors. Security maturity means adapting and improving security as the environment changes and grows. It means taking strategic actions like deploying active defenses with the help of security intelligence from multiple sources. Businesses can evolve from a legacy security state to security maturity with the help of a trusted partner.
The growing threat of cybercrime is a risk to any organization connected to the Internet. Attacks can arrive in forms that include phishing, spear phishing, ransomware attacks, zero-day attacks, known vulnerability exploits, sensitive data breaches, brute-force attacks and more. Secure Managed Services by Aunalytics offers peace of mind in knowing that IT environments are monitored and managed at all times with the goal of eliminating the risk of data exfiltration or infrastructure downtime.
“End-to-end protection requires actions and defenses that consider the entirety of systems and software throughout an organization. It also means educating employees so they are ‘security aware’ to help reduce the number of threats that may enter through vulnerable endpoints,” said Steven Burdick, VP, Sales, Cloud & Managed Services. “Aunalytics protects organizations on their security journey, deploying a defensive cybersecurity framework that provides the technology and expertise for better security posture.”
About Aunalytics
Aunalytics is a leading data management and analytics company delivering Insights-as-a-Service for mid-sized businesses and enterprises. Selected for the prestigious Inc. 5000 list for two consecutive years as one of the nation’s fastest growing companies, Aunalytics offers managed IT services and managed analytics services, private cloud services, and a private cloud-native data platform for data management and analytics. The platform is built for universal data access, advanced analytics and AI — unifying distributed data silos into a single source of truth for highly accurate, actionable business information. Its DaybreakTM industry intelligent data mart combined with the power of the Aunalytics data platform provides industry-specific data models with built-in queries and AI for accurate mission-critical insights. To solve the talent gap that so many mid-sized businesses and enterprises located in secondary markets face, through its side-by-side digital transformation model, Aunalytics provides the technical talent needed for data management and analytics success in addition to its innovative technologies and tools. To learn more contact us at +1 855-799-DATA or visit Aunalytics at https://www.aunalytics.com or on Twitter and LinkedIn.
PR Contact:
Denise Nelson
The Ventana Group for Aunalytics
(925) 858-5198
dnelson@theventanagroup.com
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Investing in digital transformation technologies can be a waste of money if your company forgets one important point. That point is, no matter how cutting edge the tech or tool may be, people are needed with specific technical expertise in order to derive true business value from these investments.
Unlike large enterprises, mid-market companies often try to find this expertise in their IT manager, hoping a jack-of-all-trades approach will take care of it. This is an unfortunate mistake, since it would require the IT manager to have unusual command over a long laundry list of duties, from data integration, ingestion, and preparation to data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on-premises environments. This is not just a tall order for a mid-market IT manager to pull off, but likely an impossible one.


To read more, please fill out the form below:
2022 Annual CUSO Conference
2022 Annual CUSO Conference
TradeWinds Island Grand Resort, St. Petersburg, FL
Aunalytics to attend the 2021 Annual CUSO (Credit Union Service Organization) Conference
Aunalytics will be attending the Annual CUSO (Credit Union Service Organization) Conference as a lunch sponsor. Aunalytics has developed Daybreak™ for Financial Services, which enables credit unions to more effectively identify and deliver new services and solutions for their members so they can better compete with large national banks.

2022 Technology First Taste of IT Conference
2022 Technology First Taste of IT Conference
Sinclair Conference Center, Dayton, OH
Aunalytics to Attend Technology First's 2022 Taste of IT Conference as a Gold Sponsor
Aunalytics is proud to be a Gold Sponsor, and excited to join over 400 IT professionals at the Technology First Taste of IT Conference on in Dayton, Ohio. Aunalytics provides a wide variety of managed IT and security solutions, such as our Secure Managed Services offering which combines mission critical IT services leveraging zero trust end-to-end security to ensure people and data are protected regardless of location. In addition, our Advanced Security solution gives organizations access to cutting-edge technology and expertise of Aunalytics professionals to prevent and mitigate cyberattacks.

2022 Ohio Bankers League Annual Meeting
2022 Ohio Bankers League Annual Meeting
Hyatt Regency, Columbus OH
Aunalytics Excited to Attend the 2022 OBL Annual Meeting as a Reception Sponsor
Aunalytics is excited to attend the 2022 Ohio Bankers League (OBL) Annual Meeting as a Reception Sponsor. Aunalytics will be demonstrating Daybreak™ for Financial Services, a cloud-native data platform which enables community banks to focus on critical business outcomes and make data-driven business decisions in order to compete with large financial institutions.