The Value of Data Visualization
In this brief video, Dr. David Cieslak, Chief Data Scientist at Aunalytics, discusses the value that data visualization brings to data analytics. Whether you’re using a simple tool such as Excel or a BI software such as Tableau, creating a visual representation of your data allows it to be consumed by a much broader and less technical audience. Whether you’re a marketing specialist, a loan officer, or a bank president, a well-designed and up-to-date dashboard greatly improves your ability to understand and work with your data in a way that lists and spreadsheets can’t.
David Cieslak, PhD, is the Chief Data Scientist at Aunalytics since its inception and leads its Innovation Lab in the development and delivery of complex algorithms designed to solve business problems in the manufacturing/supply chain, financial, healthcare, and media sectors. Prior to Aunalytics, Cieslak was on staff at the University of Notre Dame as part of the research faculty where he contributed on high value grants with both the federal government and Fortune 500 companies. He has published numerous articles in highly regarded journals, conferences, and workshops on the topics of Machine Learning, Data Mining, Knowledge Discovery, Artificial Intelligence, and Grid Computing.
Increasingly Difficult Security Requirements Complicate Cyber Insurance Renewal
Have you received a cyber insurance renewal notice with a shocking sticker price? With an ever-increasing number of security incidents involving data breaches, ransomware, phishing scams and more, the cyber insurance landscape has changed. It’s no longer possible to get premium discounts for implementing certain security controls—more is now required. And, without enhanced security measures, you may not get cyber insurance at all.
Threats evolve over time, meaning your security posture needs to evolve in order to not only remain operational, but also be compliant to qualify for most insurance policies.
Insurance companies are now requiring more precautionary measures than ever before due to the constant—and costly—increase of threats. Premiums are increasing and coverage is being denied even for companies that have no history of breaches or claims—cyber insurance renewal rates have increased by up to 200% over the past two years, even for companies who have not made any claims.
The average cost of a data breach has raised from a massive $3.86 million in 2020 to a staggering $4.24 million in 2022.
The Solution
With the risks of operating in an increasingly digital world, cyber insurance is essential for your business to function and remain protected in the event of an attack. Aunalytics’ Advanced Security experts have the talent and technology to audit your security and discuss precautionary measures an insurance company may want you to take before renewal. With a dedicated team, your business can avoid costly data breaches, ransomware, and get your security up to snuff.
Are you ready to assess your security before your company is the victim of a bad actor, costing you upward $4.24 million dollars? See if an audit by our security experts makes sense, and whether your insurance company has outright dictated (or hinted by their renewal questionnaires) new precautionary measures that they expect your enterprise to adopt to obtain coverage.
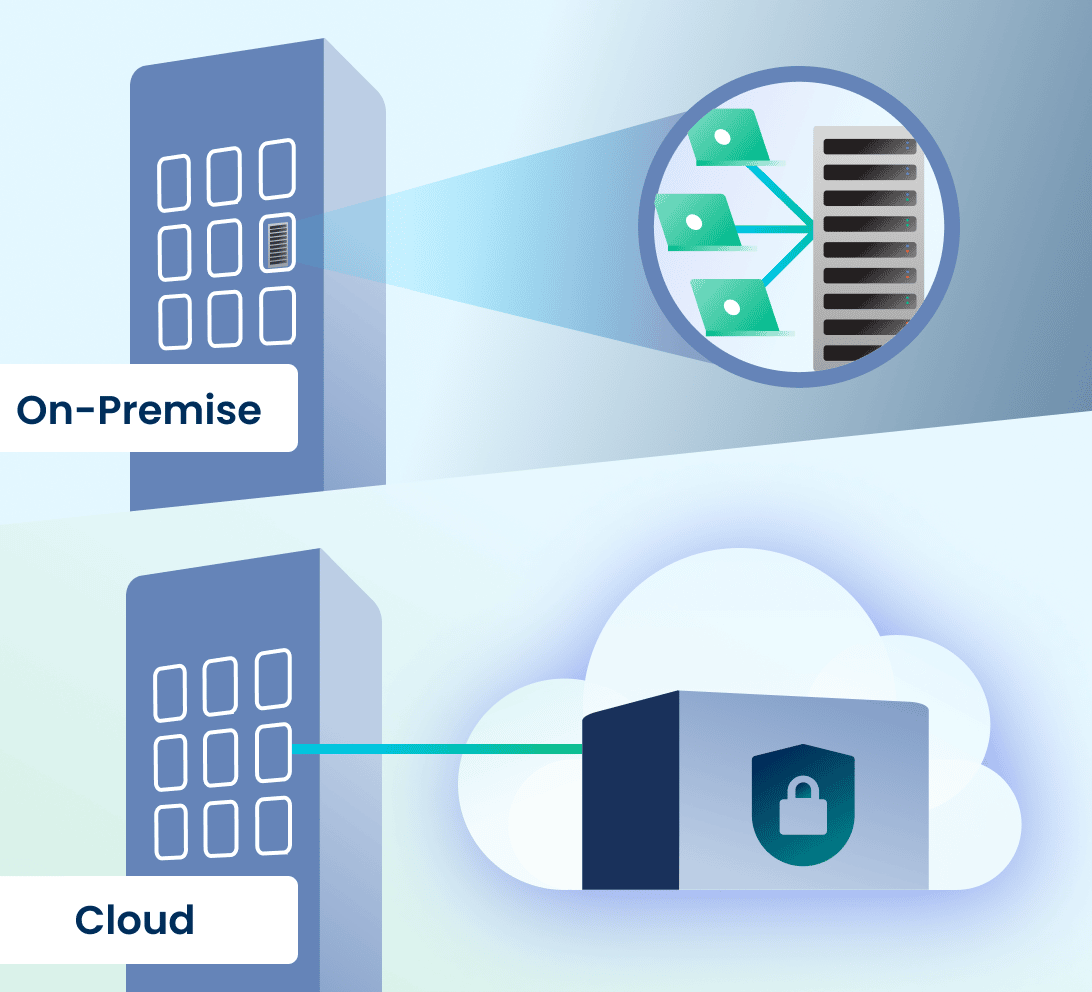
Cloud or On-Prem Servers—Which Is Better for Your Company?
Every organization needs to manage its data to get its desired business outcomes. For a company to access its data and use it in day-to-day operations, dashboards, reporting, and data analytics, it either needs a cloud or on-premises solution to facilitate compute, storage, and data management strategies.
What’s The Difference Between The Cloud And On-Premises Data Storage?
An on-premises data server is hardware that you maintain on your company’s premises for storing, processing, and accessing information through your organization’s networks. An in-house IT department is needed to maintain, turn over/replace, and upgrade the hardware, keep it stable and operational, and secure it.
A cloud storage solution run by an expert and backed by a cutting-edge data center provides the same functions as an on-premises server and more. It does not exist on your company’s premises and the data on it is accessed through the internet. All updates and maintenance tasks are performed by the cloud provider, who owns and operates its own hyper-secure data centers to safeguard your data in case of failure, cyberattack, or outage. Like on-premises servers, access to cloud data can be set by administrators to be permission-based to allow access only by authorized personnel.
On-Premises vs. Cloud—Which Option Best Suits Modern Business Needs?
There are more factors when choosing between using a cloud computing solution or keeping servers on-premises, including customizability and scalability, security concerns, and the budget for your organization’s data management strategy. While on-premises data servers regularly require hardware upgrades in your physical locations to expand alongside your business’s growing needs, a cloud storage and computing solution with access to highly advanced data centers is scalable based upon your workload. Unlike an on-premises server that can take a lot of time and money to set up and ready for operation, cloud service providers ensure you can access your cloud for computing and storage needs almost instantly.
In some mid-sized companies, server rooms tend to be used for multiple purposes, which means that they are sometimes unlocked, unsecured, and allow for unauthorized access that compromises data security. Many mid-sized companies do not have 24/7/365 monitoring of their server rooms, specialized climate controls needed for a data center, and do not consistently deploy or regularly schedule hardware upgrades to keep the systems reliable before something goes down.
One mid-market employee shares the story of a server closet that her company had in a previous workplace. For starters, it could be accessed by nearly every employee of the company. She recounted that the IT department placed portable dehumidifiers in the room to keep moisture down. The IT department’s regular practice was to empty the server closet dehumidifiers in the office’s kitchen sink. Unfortunately, a new IT employee happened to trip while carrying one of the dehumidifiers and spilled water all over the server room. Every employee of the company was affected—they found out that the work they had done since the last backup, which happened to be 5 days ago, had disappeared. Even worse, their servers were down for several days after the incident, further impacting their daily business operations.
Although in the past, people feared that cloud would not be secure, or a company would lose control over its data—cloud has proven to be more secure than on-premises hardware. First, cloud vendors host their own data centers and because this is their main business, they have cutting-edge climate control environments to protect their clients’ data. Cloud vendors adhere to frequent hardware replacement turn-over schedules to keep uptime maximized and cloud operations state-of-the-art. Cloud vendors monitor their data centers 24/7/365, are security experts, and have strict controls in place in order to service clients in highly regulated industries with rigorous data security needs. For most mid-sized businesses, it is more cost effective to rely upon the expertise of a cloud vendor for data security and uptime than to host and maintain its own servers, stay on top of the latest security threats, and staff its data center (or data closet) for monitoring to prevent downtime and security breaches.
Large enterprises often can afford to build their own data centers providing them an alternative to an external cloud provider. However, this is incredibly expensive and can set organizations back by USD $10-25 million on yearly setup and operation costs. This infrastructure also takes a lot of time to be implemented and in today’s fast-paced business environment, this might not be entirely acceptable for decision-makers.
Yet, even for enterprises, on-premises solutions no longer make the most sense. Most modern business applications are cloud-native. Cutting-edge data analytics solutions are cloud-native and connect and integrate data sources using cloud technologies. Clouds are better suited for analytics than on-premises hardware, due to scalability and ability to absorb compute spikes (instead of having to invest in hardware with capacity for compute spikes as machine learning algorithms converge—which leads to excess capacity at other times).
According to Insights for Professionals, 63% of senior IT leaders and company executives who were surveyed expected to invest in cloud infrastructure-as-a-service in 2022. Considering the state of on-premises servers, which are becoming an obsolete technology that require an IT department to keep a constant eye on it, cloud technology is a natural progression in infrastructure for better data management. Gartner reports by 2025 almost 85% of companies will have moved to a cloud-first approach. Cloud technology has now evolved to a point where it provides better stability and security at a more economical price than on-premises solutions.
Mid-Market Company Considerations
Many organizations are operating in hybrid and multi-cloud environments. This means that they have some data in on-site servers, some data in cloud based line of business applications (relying on the application provider for data storage in whichever cloud the application vendor uses for its product), and many have some data in a public cloud.
However, mid-market companies have added considerations when choosing a cloud solution. Most public cloud service providers do not offer data management services. You need to do this yourself. Yet, mid-market companies often do not have this expert talent in-house. For success, mid-market companies need a cloud hyper-scaler that also provides data engineering services to build data connectors and pipelines, warehouses, data lakes, and the like. This skill set is different from a typical IT employee. Hyper-scalers—who can help organizations with data management, transform data from disparate sources into a decision and analytics-ready status, and bring transactional data into the forefront using a cost-effective cloud solution—tend to be private cloud vendors. For this reason, private cloud solutions make more sense than public cloud for mid-sized organizations.

A side-by-side partnership with an experienced cloud-native data platform company will have a measurable and positive impact on mid-market company data management strategies, with built-in access to technical resources and experts, so that your company does not need to hire new FTEs to support data management. Rely on the data management companies for data management so that your company can focus on your main line of business.
Aunalytics’ high performance private cloud provides a highly redundant and scalable platform for hosting servers, data, analytics, and applications at any performance level. Aunalytics delivers data management in a side-by-side service model, bringing companies the technology and the talent needed for data management success. To learn more about our Enterprise Cloud solution, click here.
Don’t Ghost Your Network—Begin Your Security Maturity Journey
Is your security keeping up with the rapidly changing threat landscape? If not, your security is becoming more obsolete by the day—and more vulnerable to scary things like hackers and ransomware by the second. When a company is fully protected with the most up to date hardware, software, monitoring, and consistent patching it begins to reach security maturity.
Security maturity is a consistent state of awareness concerning your network security and can only be achieved when you:
- Have an SOC to monitor and remediate threats
- Have looped vulnerability management
- Employ active defense with security intelligence from multiple sources to protect applications, networks, servers and workstations
- Are willing to adapt your security environment to new and changing threats on a constant basis, and more.

Be Proactive
Instead of relying on a passive security model—or worse, waiting until after a companywide infection—take an active role in your company’s security. The main goal of security maturity is to avoid or reduce the number of security incidents haunting your network. It’s kind of like painting San Francisco’s Golden Gate Bridge. As soon as the painting crew gets from one end to the other with a fresh coat of paint, it is time to start again to repaint the bridge. Security maturity requires constant action and change as your organization adapts to protect against the latest evolving threats.
We all observed remote work access change security and IT on a mass scale in 2020, and security changes continue to become more necessary as bad actors and threats become more and more dangerous to your business as it continues to grow and change—and more dangerous for your customers to do business with you.
October WSJ headlines highlight a Chicago healthcare system, one of the largest in the U.S., being the victim of ransomware that is forcing it to shut down electronic records, systems, and cancel patient appointments. It is now working with law enforcement and outside cybersecurity experts to remediate. A security maturity journey is hard to make on your own, and a good partner can ensure you are meeting the highest security standards possible. Here at Aunalytics, we include security in everything we do because we believe it is a basic building block of IT.
Find A Trusted Security Partner
Without a secure network, you cannot even begin to consider moving further into a security maturity journey. Fortunately, a partner can give you the peace of mind that you will be working with a talented security team that is watching your network 24/7/365, helping to ensure bad actors are caught and eradicated before your company is compromised.
A standard, one size fits all security solution simply doesn’t work anymore—it often leaves cracks, holes, and even chasms for hackers and cyberattacks to slip through. You can improve your journey from cybersecurity to security maturity with a trusted partner.
Click here to learn more.
Ransomware Attacks Now Target Community Businesses
If you think that your business will not be a target for ransomware attackers, think again. This is no longer a problem only for large enterprises—now, ransomware attacks target community businesses as well.
The Battle Creek, Michigan community woke up to a May Day attack that forced its Kellogg Community College (KCC) to close all operations. In the middle of preparations for final exams, all five campuses serving approximately 6900 students closed and all operations came to a screaming halt.
The community college posted alerts on its website and social media:
Eric Greene, the Vice President for Strategy, Relations, and Communications at KCC said: “We are still working to understand the full extent of this incident, but as soon as we became aware of it, we immediately assembled a multi-disciplinary team and engaged independent legal counsel and external forensic experts.”
Greene continued, “KCC had backups in place, and we are working systematically with our IT experts to restore our operations.” But even though KCC had backups, “As a precautionary measure, all campuses have been disconnected and our systems will remain offline until they are deemed secure by our IT experts. As a result, our students and staff might experience delays accessing our services, including campus emails, online classes, and resources,” Greene said.
Back-ups alone are not sufficient to prevent business disruption when a ransomware attack hits. Preventing the attack, rather than having to respond to it, is key. KCC remained closed for three days while IT scrambled. All computer access to university systems had to be shut down in an attempt to stop further damage. The response and mitigation included a forced password reset for all students, faculty and staff, and adding multi-factor authentication (MFA) for all users.
Enable Multi-factor Authentication
MFA is an important security measure when people access systems remotely. It provides an extra level of verification to make sure that the user attempting to access the system is really an authorized user and not a bad actor trying to get in. Modern business regularly includes employees logging in from home, travel and mobile devices to access data and systems from their organization. As such, the old firewall security perimeter around your place of business does not protect you. Modern security requires focus on users and access. MFA is something that is easy to add to your security stack. The protection benefit from MFA far outweighs the resource cost of installing and using the technology. Really, there is no excuse for not having MFA in today’s threat landscape. It is standard.
So if you do nothing else this year to improve your security posture, add MFA. But considering that community businesses are becoming targets for cybercrimes, unless you can afford a complete shut-down of your business, it is becoming a must to have modern security technologies (including robust monitoring so that you are equipped to prevent attacks and are better positioned to respond and mitigate), in addition to back-up and disaster recovery plans.
Shift Applications to the Cloud
Mid-market businesses are shifting security and data center responsibilities from on premise servers and security maintained by their IT department, to partnering with cloud experts who run data centers, keeping client systems stable and secure as their full time business. The trend with line of business applications used by your team for daily operations is cloud. As more and more community businesses use cloud based apps for functions like accounting, customer portals, ERP, CRM and HR, having cloud experts with the tools and the skills to be able to secure your organization’s data (from multiple sources) for safe use by remote users makes more sense than trying to build a security fortress yourself at your place of business.
Partner with Experts
If cybersecurity is not your main line of business, partner with security experts unless you want cybersecurity to become your main line of business. It will consume your resources to stay current with emerging threats, protective means, 24/7/365 monitoring, best practices and constantly evolving security measures. The ever increasing sophistication and volume of attacks has shifted the answer to the “buy it or build it” question for this critical business service from the solution being your in-house IT department to the solution requiring managed security services to supplement your in-house IT team.
Don’t become the next ransomware attack headline. Community businesses can take steps to avoid ransomware attacks. An ounce of prevention, after all, is less costly than the cost of operational shut-down, PR scramble, customer service disruption, brand reputation tarnishment, and emergency security consultant fees paid when you are in the middle of an attack that succeeded.
Managed IT Services and Data Recovery Offerings from Aunalytics Solve Emergency IT Challenges for EMI

Managing business-critical IT environments is a time-consuming process that many times can require specialists with the experience to deliver the highest performing infrastructure possible. EMI has seen this first-hand over the past several years as the company has had to recover from destroyed network infrastructure caused by a catastrophic lightning strike, a disruptive cyberattack involving ransomware with the encryption of important company information, and the need to reconfigure its computing endpoints quickly because of the occurrence of Covid-19 to accommodate “work from home” environments for its team.
Aunalytics provides a broad range of managed IT solutions, including network, server management, and PC management, as well as Office 365, data recovery and business continuity support. EMI employed several services which have helped to positively transform the company’s operations.
The side-by-side support model employed by Aunalytics has been an especially impactful benefit of this partnership. “While there are many important services provided, perhaps the most widely used and important for EMI is the 24×7 help desk which is essentially an IT department on demand,” said Tom Kiefer, CFO for EMI. “Whether it’s an employee who accidentally deleted a file or a catastrophic lightning strike, the team behind the Aunalytics Ohio help desk has been insightful and fast to act, allowing our employees to remain online and productive.”
Read the full case study to see how EMI further benefitted from the managed IT and data recovery services provided by Aunalytics Ohio.
Why Cybersecurity Should Be a Top Priority for Mid-market Businesses

At the same time, the number of cybersecurity attacks has increased to its highest levels ever. It has been reported that ransomware attacks increased over 90% in 2021. Ransomware has hit new levels of sophistication, with demands for payment skyrocketing into the tens of millions. McKinsey reports that attacks are motivated by:
- Vulnerabilities posed by pandemic weary organizations and workers logging in from unsecured home networks
- Ever advancing connectivity driven by advancing digitization
- Threat actors are now “dwelling” undetected within victims’ environments (instead of using a smash and grab approach) to better understand where the highest value data and information lives and then selling that to the highest bidder
- More companies have been forced to pay ransoms to regain control of their networks and data, so hackers are further incentivized to innovate on this lucrative threat
Companies need to ensure they remain resilient by focusing on ransomware prevention, preparation, response, and recovery strategies. This is a journey—threats continue to evolve and staying ready means staying up to date with new threats of increasing sophistication, cyber security strategies, and best practices. Over time, increasing cyber maturity creates a resilient environment where attacks may still occur but do not have the same impact they would otherwise.
Mid-market businesses need expert skills in cloud security and data security, which is not standard in mid-market IT department skillsets. Keeping servers in a closet guarded by your IT department is extremely risky for data protection. With constantly looming cyber threats, organizations should make cybersecurity best practices a top business priority—and Aunalytics is here to help.
Financial institutions are frequently targeted in cyberattacks—here’s how to protect your bank or credit union

Attacks are increasingly sophisticated and cyber criminals continue to invest in new and complex criminal strategies and campaigns. Hackers in banking often take advantage of the interdependencies of financial institutions to service products such as credit cards and mortgages for other banks. From one bank breach, the cyber cartels jump to the partnered financial institution to steal its data as well.
In some types of cyberattacks, criminals make slight changes to data, which may not be immediately detectable. Because nothing is stolen at the time, users may not recognize the attack. However, once the criminals gain access to this data, they can manipulate algorithms in the system for their own financial gain. Timestamp manipulation is a newer strategy, whereby criminals have found that they are more likely to evade detection if they manipulate time for an otherwise valid transaction. Changing timestamps can alter the value of capital and trades. Because the parties to the transaction appear to be legitimate, this type of fraud is harder to detect.
Other criminals outright steal data for financial gain by selling it, hold data hostage for ransom profit, or pilfer intellectual property such as an organization’s competitive strategy and business plans to sell to interested parties. But the main goal in banking cyber-criminal activity is direct profit from a modern-day bank heist—stealing money from the bank.
Despite the increasing complexity of cyberattacks against financial institutions, there are some tools and best practices that banks and credit unions can use to protect themselves from these threats:
- Continuously update security technology and protocols as threats evolve and adapt with the help of a dedicated full-time security team.
- Employ 24/7/365 monitoring with remote remediation to quickly stop attacks in their tracks
- Monitor endpoint devices to stop attacks before they hit networks.
- Monitor cloud security including application use across the financial institution.
- Monitor email and Office 365 using tools specially designed to thwart attacks on these platforms, such as proactively recognizing and removing phishing scams.
- Have a dedicated security team and SOC, or hire an expert outside managed security services firm that embeds tools, technology and 24/7/365 monitoring to serve as your SOC.
- Push frequent patches so that user devices are equipped with the latest security protections.
- Adopt deep learning or AI monitoring, mitigation and context investigation that can more quickly identify threats.
- Encrypt data so that it is not compromised even if a breach occurs.
- Use multi-factor authentication to protect against unauthorized access.
- Instruct employees and customers to only access bank data in a secure location over a non-public Internet connection.
- Train employees on cybersecurity threats quarterly.
- Develop a solid business recovery plan for when an attack occurs.
Learn more about how Aunalytics Advanced Security helps protect financial institutions, and businesses in other highly regulated industries, from cyberattacks.
Marketing pitfalls can damage customer relationships—here's how to avoid them
While the main goal of marketing is to gain new customers or increase spend from existing customers, at times, marketing effort can do more harm than good. Unfortunately, a marketing campaign could not only fail to entice customers, but certain pitfalls could actively damage customer relationships. Fortunately, there are ways to avoid them. Below are three major mistakes that marketers are prone to making.
#1 Duplicate Mailers

This leaves you to focus on the wasted paper and postage instead of the product or service being marketed. And if the company sending the mailer knew more about the target customer, perhaps the target is someone who does not respond well to snail mail and doesn’t like it. Mailed promotional materials go straight into the recycling bin without even entering houses in many households. This type of waste would be avoided by intel on channel preference of prospects.
When you receive duplicate mailings from a company that you do not do business with currently, it can be viewed as a sign that the customer experience would lack attention to detail, personalization and efficiency. This is a turnoff. That company is likely to be put on a mental list of those you do not want to do business with – period.
If a company that you are doing business with sends multiple duplicative mailers to your home, this can be even worse. In this digital world, many businesses ask customer profile questions including preferred contact method. If you opt in for electronic communications and e-bills, sending a mailer shows that the company is either not listening to its customers or the company is not communicating well within its internal teams. You took the time to complete the profile, yet the business can’t be bothered with using your input. Did anyone read your form fill results? Again, this shows lack of personalized customer experience, inefficiency and lack of cohesiveness in operations. As a current customer, you feel even more devalued than the business that does not have a relationship with you.
Sometimes the duplicate mailings are sent to your name using slight variations of your address, such as “Street” versus “St.” If the business cleaned up its mailing list and recognized that this is the same location, it would save on operational costs and make the company look smarter.
#2 Marketing Products to Customers Who Just Bought Them
A second frustration is receiving a mailer from a company that you currently do business with asking you to purchase products or services that you already have purchased from them. For example, a bank sends a mailer to open a HELOC account or a credit card account when you already have that product from that bank. Is the bank carpet bombing mailings to everyone? How wasteful. Is it that the bank does not care enough about you as a customer to take the time to realize which products you already have with them?
The misdirected marketing may cause customers to begin to think that they should place their business with a bank that cares about their business enough to know which accounts a customer has with them. Really, the relationship would be better if the bank stopped trying to engage its customers than continue to do so with communications that miss the mark.
#3 Bad Timing
A third pet peeve with marketing is when the offers are untimely. For example, if you just refinanced your mortgage with your bank, the bank should not send you a mailer 10 days later for a refinancing opportunity. Yes, customers appreciate notification of interest rates becoming more favorable. But given that you just paid closing costs (or folded them into your loan), refinancing 10 days later is not likely. Instead, you run the risk that the customer sees even better terms being offered and feels dissatisfied with his new product or even mad. From the customer’s perspective, if the bank had told him to wait 10 days, he’d have better terms. Marketing can do better on timing.
Marketing should not damage customer relations.
The Digital Data Challenge
Many businesses have a plethora of data that is typically siloed across many systems throughout the organization. Aggregating and integrating this data for marketing purposes is a major challenge that can be difficult and time-consuming, if not nearly impossible.
Hyper-personalized services that factor in intelligence about a customer holistically should form the core of customer relationships. To achieve this goal, businesses can integrate their disparate data architecture across lines of business and functions to create a 360-degree view of customers and allow for targeted marketing based upon data.
New and advanced data analytics powered by artificial intelligence (AI) are available today that enable customer intelligence to drive marketing. Aggregate your data and ensure that it is cleansed to remove duplicate customer lists for mailings. AI-powered analytics recognizes when people with different names are part of the same household to further eliminate duplicate mailings.
Harness the power of your data to personalize a customer’s experience with your company and not only avoid these pitfalls, but enable smarter targeted marketing.
Data Analytics Helps Midsize Financial Institutions Thrive

It is unlikely that midsize and community banks will “out tech” large banks and fin-techs on their own. However, with the right partners, they have an opportunity to thrive by redefining the local experience and digitally transforming how they operate. Using the right data analytics, they can leverage their local knowledge with personalized customer intelligence to regain competitive advantage.
Customer Intelligence within Reach
Auna offers the ability to target, discover and offer the right services to the right people, at the right time. Built from the ground up for midsize community banks and credit unions, Auna is powered by the Intelligent Data Warehouse. The solution cleanses data for accuracy, ensures data governance across the organization, and employs AI and machine learning (ML) driven analytics to glean customer intelligence and insights from volumes of transactional data created in the business and updated daily. The daily insights and industry intelligence enable a variety of analytics solutions for fast, easy access to credible data, users can find the answers to such questions as:
- Which current customers that have a loan but not a deposit account?
- Who has a mortgage or wealth account with one of my competitors?
- Which customers with a credit score above 700 are most likely to open a HELOC?
- Which loans were modified from the previous day?
- Who are current members with a HELOC that are utilizing less than 25% of their line of credit?
Harnessing their data with Auna enables community banks and credit unions to discover patterns, insights, trends, and usage strategies helps to strengthen their position in regional markets and compete with large national banks. With Aunalytics, they are enabled to deliver timely personalized messages to customers, make data-driven product recommendations, measure campaign ROI, and grow net dollar retention.