Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Investing in digital transformation technologies can be a waste of money if your company forgets one important point. That point is, no matter how cutting edge the tech or tool may be, people are needed with specific technical expertise in order to derive true business value from these investments.
Unlike large enterprises, mid-market companies often try to find this expertise in their IT manager, hoping a jack-of-all-trades approach will take care of it. This is an unfortunate mistake, since it would require the IT manager to have unusual command over a long laundry list of duties, from data integration, ingestion, and preparation to data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on-premises environments. This is not just a tall order for a mid-market IT manager to pull off, but likely an impossible one.

At the same time, it’s unreasonable to expect that most mid-market firms can hire an entire division of data experts—who each need to be highly compensated—in order to achieve the organization’s digital transformation goals. Even if a mid-market player could afford it—which is unlikely to make economic sense—these talent resources are scarce and in high demand.
If you’re still wondering whether your IT manager’s skill set, leveraged by your in-house IT technicians, can properly run the gamut required to achieve value from your data technology investments, consider that the person in this position would need the ability to master a wide range of skill sets, from cloud architecture, database engineering, and master data management to data quality, data profiling, and data cleansing. More specifically, your IT manager would need to take on five additional specialized roles for technical talent that are critical for achieving value from data technology investments.
These roles are:
Chief Data Officer/Chief Digital Officer
A chief data officer (CDO) is focused on—you got it—data. Most mid-market companies understandably don’t have a CDO, which means they don’t have anyone who assures regulatory compliance for data handling while managing and exploiting information assets, reducing uncertainty and risk, and applying data and analytics to drive cost optimization and revenue objectives. For IT managers to fulfill a CDO role, they’d have to be equipped to bring a global perspective to company data, help their organization gain competitive advantage over peers, and manage data and analytics. They’d also need the ability to secure data, transform it into valuable business information, lead digital transformation initiatives, and use data for growth and operational efficiency.
Cloud Engineer
The primary job of a cloud engineer is to keep cloud data centers operational and secure for ecosystem users to be able to store and access their data. Cloud engineers are experts in minimizing downtime, managing access to data, managing compute and storage, and setting up cloud architectures for clients, tenants, and containers. They also monitor data center hardware, servers, networks, and communications systems for operational continuity and efficiency.
Data Security Expert
Mid-market firms also need a way to channel the talents of a data security expert, CISO, or cybersecurity director to ensure cyber-security for the company’s data. Data security experts must keep current on emerging threats while executing data security strategies to fend off and remediate attacks. This involves a wide range of duties, including working closely with the IT team to run the company’s Security Operations Center (SOC), constantly monitoring servers, networks, and workstations for security threats, and staying up to date on the changing compliance laws and regulations for the business, to name a few. While larger IT teams have bandwidth to fill cybersecurity needs inhouse, many midmarket IT teams do not have capacity for the 24/7/365 monitoring and security edits needed to thwart attacks, let alone bandwidth for executing on mitigation and response strategies needed to overcome them.
Data Engineer
A data engineer’s primary job is to prepare data for analysis or operational uses, which involves integrating data from different sources, as well as implementing and executing data profiling, cleansing, transforming, and normalizing data. Data engineers also work with data in motion and use master data management to ensure data consistency across an organization. Finally, a data engineer is your go-to technical resource for database construction and management, helping to optimize the company’s data ecosystem.
Data Scientist
It should be clear now why a mid-market IT manager should not be expected to take on these additional professional roles, but in case there’s any doubt, keep in mind that a data scientist is also needed. Data scientists develop algorithms and leverage deep learning models to analyze data with artificial intelligence and machine learning. The data scientist creates the “brain” of the data analytics solution to position it for providing accurate answers based on business information. Data scientists also mine data to find opportunities for business growth and efficiency. Ideally, the data scientist uses tools that enable non-technical business users to query data sets without having to write SQL or other code.
Master of One
If you’ve correctly determined that your mid-market IT department does not have enough time to absorb these data roles into their regular duties of keeping your company systems stable and responding to help desk tickets from your team, don’t despair. There’s a viable solution for mid-market businesses with this dilemma: they can partner with data experts who provide a side-by-side model coupling technology with talent. This allows the mid-market to efficiently compete, leveraging the necessary skillsets to achieve digital transformation success.
What does successful mid-market digital transformation require? The key is to have a cloud-based data center, a cloud native data management platform, and cloud native analytics, thus shifting the burden of procuring and maintaining the infrastructure to a third-party vendor in the data industry. Instead of attempting to reinvent the wheel in house, mid-market players should ensure they’re partnered with the right infrastructure to maximize the data-center capabilities, and data storage and management, for effective digital transformation.
Mid-market firms can gain the benefits of working with a wide range of experts including cloud engineers, data engineers, security experts, data scientists, and other highly skilled technical resources if they establish a partnership with a data platform company. By opting for this type of side-by-side expert help, the mid-market can achieve true business value—without needing to hire an entire data team.
The Cost of Skimping on Security in 2022
From 2020 to 2021, the number of ransomware attacks on organizations increased by 78% and more than 10% of those attacks resulted in ransoms of $1 million or higher. According to the Sophos State of Ransomware 2022 report, ransomware attacks take an average of one month to fully recover from and frequently result in downtime and loss of revenue, the impact of which leads to an average recovery cost of $1.4 million. That’s about 640 vacations to Disney World. The cost of skimping on security is great.
While you could take your entire team to Disney World for a week, possibly even a few times over, a better idea might be to invest in preventing a security breach in the first place. Be it ransomware, a phishing attack, or an insider threat, proactive threat and risk prevention takes dedicated time, well-trained people, and cutting-edge technology, so it is no surprise that it can be confusing and costly. As we’ve already seen, it can be even more costly to ignore those risks.
Keeping Up with Technology
It took 2 million years for humans to progress from the first tools to discovering fire, yet it only took 130 years to go from the telegraph to the internet and another 33 years to get to the iPhone. Technology now changes at a blistering pace and, alongside that thrives the unfortunately fruitful business of cybercrime. One of the most critical factors in combating this is having, understanding, and fully utilizing the latest technology. Based on Gartner’s 2022 report of Top Strategic Trends, some of the newest technologies that will impact the cybersecurity field include:
- Cybersecurity Mesh: A scalable, integrated architecture that enables security tools to work cooperatively throughout an environment
- Autonomic Systems: Self-managing systems that take in information from the network to modify algorithms without manual updates, allowing for rapid changes and scalability
Source: Gartner
Partnering with the Experts

Whether you are intimately familiar with the concepts presented here or they sound like something from the USS Enterprise, partnering with experts is what will give you an advantage over bad actors and cyber criminals. Admittedly, most organizations struggle to keep up with regular patching, let alone investing the time and resources into implementing these types of technology. While cybersecurity and understanding cyber risk are likely not your area of expertise, working with a trusted partner can ensure that your online business and IT landscape are as secure as technology and expertise allow. Having security that stands up to the worst of ransomware, hackers, and more is a must.
The criminals don’t take a break, so your security monitoring can’t either, which is why it is critical to have both the technology to meet the needs of today’s risks as well as the people to understand, implement, and manage that technology to its fullest potential. Aunalytics has you covered. With expert toolsets and talent, your business can depend on us to have highly trained professionals and the newest technology and information to protect your business in the ongoing threat landscape.
Bridging the Mid-Market Talent Gap for Digital Transformation
Bridging the Mid-Market Talent Gap for Digital Transformation
To achieve business value from data technology investments, mid-market companies need the right technical expertise and talent. Yet many mid-market firms push this onto their IT manager, assuming that since it is technology related, IT has it. This is a mistake because most IT departments do not have time for data analytics. They are busy full time keeping company systems stable and secure, and providing support to your team members. This by necessity results in IT deprioritizing data queries over crucial cybersecurity attack prevention. Business analysts and executives get frustrated waiting for data query results, and the data is stale or the business opportunity has passed by the time query results are in.

But even if your IT team had time for it, it still is a mistake to rely on traditional technology administrators for data analytics success. This is unless your IT department has expertise across a wide range of skill sets, from cloud architecture, database engineering, master data management, data quality, data profiling, and data cleansing. What’s more, your IT manager would need to have command over data integration, data ingestion, data preparation, data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on premises environments.
When you read this laundry list of needs, it becomes clear that most mid-market IT departments lack the specialized experts needed to derive business value from their data. Unlike larger enterprises that have the resources to hire skilled staff for these roles, the mid midsize organization requires another option that provides access to the right tools, resources, and support. One that integrates, enriches and is trained in utilizing AI, machine learning, and predictive analytics to achieve more useful results.

To read more, please fill out the form below:
Don’t Let Your Sensitive Data Go Unprotected
Every business has sensitive data that should not be shared with the world at large. Credit card information, personal details, company records—all of this data can be exposed or stolen and ransomed via a single bad actor.
Is Your Data Safe?
Everyone from banks and credit unions to government agencies and utility companies need one basic thing that can stop bad actors: good data security. With hackers and ransomware encroaching on your network, it’s more important than ever before that you have proactive data protection in place.
Good data security includes 24/7/365 monitoring of your network, constant threat and vulnerability scanning, a functioning Security Operations Center (SOC) and more. The problem? It’s hard to find talent to maintain a functional SOC, and when you do find talent your mid-market business may not be able to compete with offers from large enterprises.
While finding, paying, and retaining high quality talent is hard, partnering is not. A side-by-side approach with a knowledgeable partner allows you to actively react to the ever-changing digital landscape—not after your company’s security has been left behind and open for bad actors.
How Can You Protect Your Data?
Many security tools are made for experts—security engineers, network engineers, and others with specific technical expertise. Because the security landscape keeps changing, as bad actors evolve techniques and new threats are constantly emerging, security requires full time dedication to researching and staying up to date with threats, new prevention measures and remediation best practices. Most IT departments do not have time for the research and adaption that security requires. If you don’t have a team that can constantly update your security to provide your company with the best security possible, your security posture will begin to sag. A sagging posture isn’t good for any industry or company—and it needs to be fixed immediately.
By hiring a trusted partner, you can ensure that your sensitive data is secure. Having security that stands up to the worst of ransomware, hackers, and more is a must. An SOC takes care of things for you.
If your company doesn’t have an SOC, it is falling behind. Out of date security means injury to your network becomes more and more likely, and a security event can cause you to lose clients and prospects, large sums of money, and even tarnish your company’s reputation.
Partnering Up
You should already have an internal IT team. Aunalytics’ SOC isn’t meant to replace your IT team, but to supplement and support your team’s security initiatives. An SOC can stop threats before they enter your network and cause chaos, keeping your data out of the hands of bad actors everywhere.
When you need to protect your data, Aunalytics has you covered. With expert toolsets and talent, your business can depend on us to have highly trained experts and the newest technology and information to protect your business in the ongoing threat landscape.
Bridging the Mid-Market Talent Gap for Digital Transformation
Bridging the Mid-Market Talent Gap for Digital Transformation
To achieve business value from data technology investments, mid-market companies need the right technical expertise and talent. Yet many mid-market firms push this onto their IT manager, assuming that since it is technology related, IT has it. This is a mistake because most IT departments do not have time for data analytics. They are busy full time keeping company systems stable and secure, and providing support to your team members. This by necessity results in IT deprioritizing data queries over crucial cybersecurity attack prevention. Business analysts and executives get frustrated waiting for data query results, and the data is stale or the business opportunity has passed by the time query results are in.

But even if your IT team had time for it, it still is a mistake to rely on traditional technology administrators for data analytics success. This is unless your IT department has expertise across a wide range of skill sets, from cloud architecture, database engineering, master data management, data quality, data profiling, and data cleansing. What’s more, your IT manager would need to have command over data integration, data ingestion, data preparation, data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on premises environments.
When you read this laundry list of needs, it becomes clear that most mid-market IT departments lack the specialized experts needed to derive business value from their data. Unlike larger enterprises that have the resources to hire skilled staff for these roles, the midsize organization requires another option that provides access to the right tools, resources, and support. One that integrates, enriches and is trained in utilizing AI, machine learning, and predictive analytics to achieve more useful results.
Achieving Digital Transformation
Digital transformation has been defined by some as the integration of digital technology into all areas of a business, fundamentally changing how employees operate and deliver value to customers. Some of the challenges midsize businesses have with building an internal team to initiate this concept are employee pushback, lack of expertise to lead digitization initiatives, improper organizational structure, the absence of a digitization strategy and limited budget. As an alternative to building an internal operation, a more efficient way for mid-market businesses is to leverage the skillsets of experts by partnering with a consolidated group of experts, leveraging a side-by-side model that couples technology with talent. Look for solution providers that offer the following:
- Powerful cloud data centers paired with engineers skilled in architecting cloud-based applications and processes that better serve critical business requirements. These data centers are optimized for true multi-tenancy, built on seamlessly integrated hardware and software, offer business-driven configurability, world-class security and performant systems.
- Active Monitoring and Thoroughly Integrated Security. Monitoring and security should be pervasive across system infrastructure to defend against cyberattacks and provide remediation when required. Business customers will also expect full-time monitoring and on-demand help desk to address unexpected events. The data management platform underpinning applications should be monitored by experienced data engineers with success in building data warehouses, data lakes, and data pipes. They should also be able to integrate, cleanse, and transform data into decision-ready and analytics-ready business information.
- High ROI Business Insights that Drive Results. Data analytics investments need to provide real business value by giving actionable insights and finding opportunities within your data. With this in mind, data analytics should include access to data scientists and business analysts versed in your industry. These experts should be equipped to design AI-powered algorithms that answer the most pressing questions based on real-world business challenges.
Mid-Market Data Transformation for Enterprise-Class Results
Ensuring the right mix of hardware, software and resulting services are available to maximize the data center capabilities—and their ability to manage and protect data—is crucial to effective mid-market digital transformation. To compete and drive value, the cloud data center provider must deliver at all levels, with customizable business intelligence solutions powered by an effective data management platform that is secure and compliant. Successful mid-market digital transformation thus requires a shift of responsibilities for infrastructure procurement and maintenance to a third-party provider backed by experienced staff and best-in-class infrastructure.
When implementing a digital transformation project, your company gains from the many benefits this brings, such as a higher return on your IT investment, increased employee and customer experience, and greater business agility. This is further enhanced by leveraging experienced cloud engineers, data engineers, security experts, data scientists, and other highly skilled technical resources—achieving true business value from the investment. And by partnering with experts, your company’s time, resources, and innovation can be focused on its core competencies.
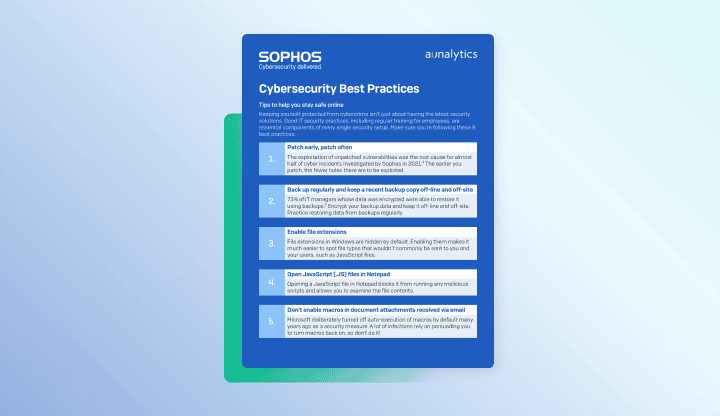
Cybersecurity Best Practices - PDF
Cybersecurity Best Practices
Tips to help you stay safe online
Best Practices for Securing Your Network from Ransomware - PDF
Best Practices for Securing Your Network from Ransomware
Elevate your protection against ransomware and other network attacks
How to Keep Your Business Thriving in a World of Risks - PDF
How to Keep Your Business Thriving in a World of Risks
Managed security can protect your Business from cyber attacks
Cybersecurity for you - PDF
Cybersecurity for you
Enterprise-class IT protection for the small- to mid-size company
See Yourself in Cyber—How Individuals Can Reduce Security Risk
It seems like just yesterday our biggest security risk was a ‘long lost relative’ claiming we had millions of dollars waiting for us if only we would send them a little money up front. The world and technology have come a long way since then, and not always for the better. Now we are inundated with spam in the form of calls, texts, emails, and every other form of communication in existence—all alongside our actual conversations. Your grandma might message you on Facebook to ask for your help and it turns into requiring a trip to Walmart to buy $500 in Apple gift cards. Your CEO might text you with an urgent request when they’ve never texted you before. With this constant barrage of threats that continue to get more and more believable, is it even possible to be safe online? It most certainly is, but it requires vigilance and a keen, informed eye.
October is Cybersecurity Awareness Month in the US and this year’s theme is ‘See Yourself in Cyber’. Whether you’re the head of IT, a bank teller, a homemaker, or anything in between, you’re at risk of a cybersecurity attack. However, the industries experiencing the highest number of incidents are finance, healthcare, and public administration. As scammers, hackers, and generally ‘bad actors’ hone their craft, we also need to sharpen our detective skills. It’s an unfortunate truth, but we need to learn how to spot the red flags because it’s expected that, by 2025, there will be an average of 10 devices per person connected to the internet globally. All of which become a playground for cybercriminals if the devices aren’t well guarded by technology—and you.
Types of Threats
There are as many reasons bad actors attack as there are ways they do it. Understanding the most common methods will help you better avoid them in the wild. Here are some of the most widespread attacks you might see:
- Phishing: When a bad actor sends an email that appears to be from a reputable source or someone you are likely to trust in the hopes that you will open an infected attachment or follow a malicious link. This could allow them access to your system or persuade you to divulge personal information, such as passwords or credit card information.
- Spear Phishing: When a bad actor sends a phishing attack specifically targeting you. Typically, it will include information they’ve learned about you from social media or other online public forums.
- Smishing: This is phishing in the form of a text message.
- Vishing: This is phishing in the form of a phone call.
Spotting the Red Flags
For these types of threats, you’ll need to be able to identify something out of place to make you pause before taking any harmful actions. However, this is where vigilance is critical because these red flags are becoming increasingly more difficult to spot. Below you will find guidance on where you are most likely to spot a threat:
- Email is the most likely path a scammer will take. When identified separately, these signs may not seem concerning, but when combined, they are a sure sign of a phishing attack.
- Does the subject line or content of the email seem alarming or urgent?
- Is the email from someone unexpected or unknown?
- Is the ‘reply-to’ address different from the ‘from’ address?
- Did the email come in at an unusual time or day, such as in the middle of the night or on a weekend?
- Are there grammar or spelling mistakes?
- Does the wording seem unnatural?
- Are there unexpected or suspicious links or attachments?
- Are they offering you money or gift cards in exchange for an action?
- Is the email unexpected or out of place?
- Text messages may come in a different format, but they can still open you to the same security risks. Many of the red flags above still apply, but these are the most common examples in smishing.
- Is the sender claiming to be an executive at your company with an urgent need?
- If you know the sender, is the text from the number you have for them?
- Are you being asked personal information?
- Are you being asked to follow a link?
- Phone call scams commonly prey on the elderly and are more common outside of the workplace. Common signs to look for in vishing are:
- Is the call unexpected?
- Does the caller request access to your device to solve an issue?
- Does the caller threaten legal action or claim to be from a governmental body such as the IRS?
- Does the caller claim you have won money or a prize?
- Does the caller request payment in the form of gift cards or money orders?
Protecting Yourself
This feels like a lot of effort; what’s really the worst that can happen if you fall for one of these scams? If you click on a malicious link or download an infected attachment, you leave the door wide open for a hacker to access not only your device, but your entire network of devices and data. If they are able to access your personal information, they could potentially access your bank account, credit card information, or other private accounts. Shockingly, 88% of data breaches are caused by employee mistakes. Here are some steps you can take to ensure you aren’t part of that 88%:
- If an email comes from someone you work with, but you are noticing red flags, especially links or attachments, contact the person directly to verify they actually sent it.
- If there are links in the email, hover over them to ensure they match what is being displayed.
- Ensure links point to a trustworthy site. For example, you might receive an email from Microsoft asking you to reset your Outlook password, but when you hover over the link, it shows http://www.microsoftt.com/. Notice the misspelling in Microsoft.
- If you are unsure of a link, navigate to the website through your browser rather than clicking the link.
- If you receive an attachment that you didn’t expect, such as a financial statement when you don’t work in finance or a UPS shipping confirmation when you didn’t order anything, don’t open it until you can confirm its validity.
- Always remember, it is truly better safe than sorry when it comes to suspicious links or attachments.
This is just a small window into an ever-changing landscape of security threats. It might feel impossible to keep up as threats evolve, but there are ways to stay informed and vigilant for both you and your company. Through its Secure Managed Services Solution, Aunalytics provides the tools and talent you need to stay protect from outside threats, include a streamlined training platform to ensure you and your team can stay up-to-date with current threats and reduce security risk. When you are able to ‘See Yourself in Cyber’, you become critical in fighting against bad actors and the cyber threats they pose.