Understanding the Hackers' Playbook: How to Prevent Cyberattacks and Adopt Good Practices
As increasingly sophisticated cyber threats pose risks to companies of all sizes, understanding how to prevent cyberattacks and implement good safety practices is important for any organization. This blog post discusses the common threats that companies face, effective cybersecurity strategies, and best practices for maintaining robust defenses. We’ll also explore how to foster a culture of security awareness and prepare for rapid recovery after an incident.

Understanding Common Cyberattacks
To effectively combat cyberthreats and develop smart strategies, organizations must be able to recognize common threats. One increasingly common type of attack is an opportunistic attack—attacks based on available opportunities rather than specific targets. One of the most prevalent opportunistic attacks involves exploiting known vulnerabilities—weaknesses in software or systems that, if left unpatched, can be leveraged by hackers to gain unauthorized access. For example, the Experian data breach demonstrated the dangers of neglecting known vulnerabilities. Despite being aware of the issue for weeks, Experian’s IT team failed to act, resulting in a massive compromise of personal data. This incident highlights the importance of timely patch management and proactive security measures.
Another critical threat is the compromise of business email accounts, often leading to the exploitation of platforms like Office 365. Common risk factors include the lack of Multi-Factor Authentication (MFA) and poor security practices. While MFA can significantly reduce the risk of unauthorized access, many organizations still avoid implementing it, often due to perceived inconvenience. However, the benefits of MFA far outweigh the hassle, making it a fundamental component of a strong security posture.
While technologies such as MFA are extremely effective at preventing cyberattacks, it doesn’t prevent all breaches. Phishing, though a simple, well-known concept, remains one of the most effective and damaging methods of cyberattack. Phishing emails trick recipients into divulging sensitive information or clicking on malicious links. It is all too easy for a single employee to have a brief lapse in judgement that puts an organization at risk. To combat this, phishing-resistant MFA and ongoing employee training are essential.
Key Components of an Effective Cybersecurity Strategy
To build a robust cybersecurity strategy, it’s essential to implement layered defenses and understand the key principles of security management. Phishing-resistant MFA adds an extra layer of security by requiring multiple forms of verification before granting access. This makes it significantly harder for attackers to gain unauthorized access through stolen credentials.
Additionally, understanding the shared responsibility model is crucial. Organizations must know their responsibilities and choose technology providers that align with their security needs. This includes ensuring that all security measures are covered and that responsibilities are clearly defined.
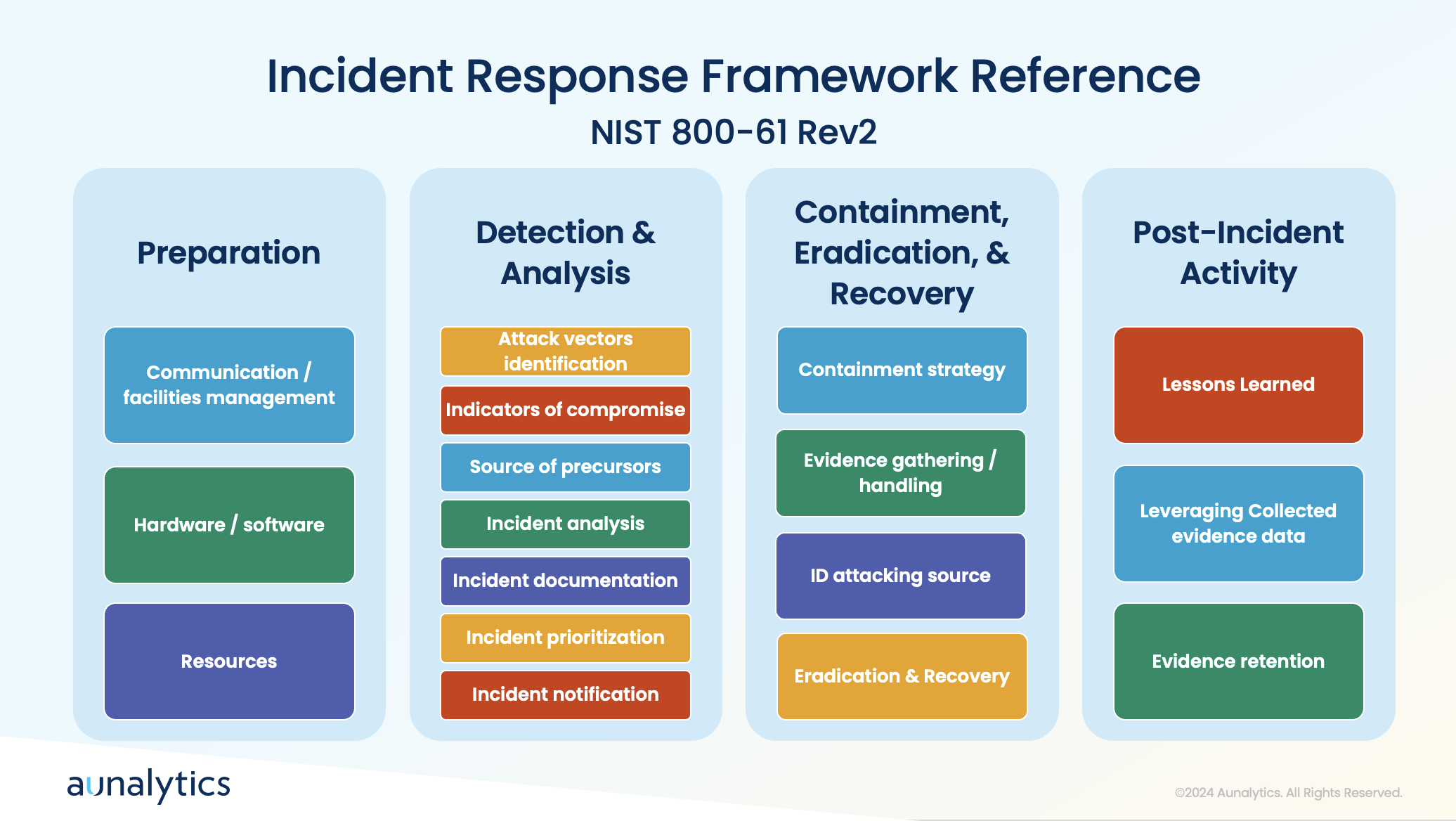
Employing established security frameworks, such as the NIST Cybersecurity Framework (CSF), can also provide a structured approach to managing and mitigating cybersecurity risks. These frameworks offer guidelines on identifying, protecting, detecting, responding to, and recovering from cybersecurity incidents.
Keeping Cybersecurity Policies Up-to-Date
Security threats are constantly evolving as hackers develop increasingly complex methods and uncover new vulnerabilities. To maintain a strong cybersecurity posture, organizations must continuously adapt their strategies—regularly reviewing and updating policies is essential. This includes conducting periodic assessments and audits to ensure that policies remain effective and relevant. It is also beneficial to regularly test and refine response plans by conducting tabletop exercises to simulate cybersecurity incidents. These exercises help organizations prepare for real-world scenarios and improve their incident response strategies.
As tactics evolve and new vulnerabilities are uncovered, organizations must stay informed of the latest security news and intelligence. This can include gathering threat intelligence from partners and industry sources, and staying informed through news articles, social media, and threat intelligence feeds. Additionally, engaging in a crowdsourced approach to security allows organizations to tap into a broader pool of knowledge and expertise. Participating in cybersecurity forums and collaborating with external security experts can take this knowledge a step further and helps organizations learn how to proactively address potential risks.
Best Practices for Incident Response
While putting safeguards in place to prevent cyberattacks from occurring is imperative, it is also equally important to prepare your organization to respond appropriately when an incident does occur. During a cyberattack, it’s crucial to have tools in place to detect anomalies and communicate effectively. Quick actions include containing the incident by taking affected systems offline, blocking access to malicious platforms, and assessing the scope of the breach.
A clear communication plan and understanding of the attack’s attribution are essential for effective recovery. Preparation involves establishing processes for detection, analysis, containment, eradication, and recovery, followed by post-incident activities to improve future responses.
Employee Training and Awareness

To ensure that all areas of a company take an active role to prevent cyberattacks, it’s crucial to foster a strong security culture. Unfortunately, employees often make mistakes that lead to breaches, such as falling for phishing schemes or responding to solicitation calls. Educating staff about the tactics used by attackers, such as impersonation and social engineering, can help prevent these errors.
Therefore, it is crucial to ensure that all employees have access to cybersecurity training—this training covers the basics of recognizing bad actors and avoiding common traps.
Tailoring training to specific roles and conducting phishing email simulations can enhance employees’ ability to identify and respond to threats. Creating a culture of cybersecurity awareness involves emphasizing the importance of security to employees and their families. This helps instill a sense of personal responsibility for maintaining security practices.
For IT and cybersecurity professionals, it is greatly beneficial to focus on developing a strong understanding of network engineering, including routing, switching, and firewall management. Additionally, the ability to visualize and comprehend data flows and security information is crucial for effective security management. IT teams must avoid cutting corners and ensure robust security measures are in place. They play a critical role in enforcing security policies and preventing breaches, making their diligence essential.
Conclusion
Understanding the tactics used by attackers and implementing robust preventive measures is key to safeguarding your organization. By adopting best practices such as phishing-resistant MFA, regularly updating policies, leveraging threat intelligence, and training employees effectively, companies can significantly reduce their risk of cyberattacks. Additionally, having a well-defined incident response plan and fostering a culture of security awareness ensures preparedness for any potential breaches. By following these guidelines, organizations can better protect their data and maintain a strong defense against cyber threats.

Partnering with Aunalytics ensures your data privacy and security through a comprehensive approach that includes advanced risk assessments, phishing-resistant Multi-Factor Authentication (MFA), and continuous updates to align with industry standards like the NIST Cybersecurity Framework. Our expert team provides 24/7 monitoring and rapid threat response, leveraging cutting-edge technology and threat intelligence to preemptively address risks. With Aunalytics, you benefit from top-tier protective measures and a commitment to adapting strategies to emerging threats, ensuring your data remains secure and confidential.
2023 misecCON
2023 misecCON
Radisson Hotel Lansing at the Capital, Lansing, MI
Aunalytics Is Excited to Attend the 2023 MisecCON as a Bronze Sponsor
Aunalytics is excited to attend 2023 misecCON in Lansing, MI. The Aunalytics team is excited to connect with fellow security experts and discuss new developments and innovation in the field.

2023 Technology First Taste of IT Conference
2023 Technology First Taste of IT Conference
Sinclair Conference Center, Dayton, OH
Aunalytics Is Excited to Attend the 2023 Technology First Taste of IT Conference
Aunalytics is excited to attend the 2023 Technology First Taste of IT Conference in Dayton, OH as a Gold Sponsor. The Aunalytics team is excited to connect with fellow IT professionals to discuss security and innovation in the technology field.

2023 IBA Security & Technology Conference
IBA Security & Technology Conference
Renaissance Indianapolis North Hotel, Carmel, IN
Aunalytics Is Proud to Be a Breakfast Sponsor at the 2023 IBA Security & Technology Conference
Aunalytics is excited to attend the Indiana Bankers Association Security & Technology Conference in Carmel, IN. Aunalytics is participating as a Breakfast Sponsor and our team is excited to connect with fellow IT professionals to discuss security and innovation in the technology field.

Think You Know Ransomware? Fighting Cybercrime: Weapons and Warriors
Cybercrime is no longer an inconvenience for an unlucky few—rather, it has far-reaching implications for the global economy, as well as national security. According to the World Economic Forum, the annual cost of cybercrime is projected to reach $10.5 trillion in 2025. In addition to economic consequences, hostile countries such as North Korea have been known to fund their weapons programs through cyberattacks and crypto theft. Therefore, fighting cybercrime should be a top priority for both governments and organizations of all sizes.
It is almost impossible to find an organization, or even an individual, who does not deal with the storage and transmission of data in one way or another. That makes anyone a target. And, unfortunately, the weakest links in the chain are oftentimes the users themselves. Anyone can mistakenly open a dangerous email or click on a malicious link, and that is all it can take to compromise an entire organization.
So how can organizations fight back and protect themselves from this looming threat?
As technology enables more complex attacks, experts say that combatting cybercrime requires a human skillset—including security awareness education for each and every individual, as well as advanced cybersecurity technology paired with 24×7 monitoring. In the last video of their three-part series on ransomware, Sophos, an Aunalytics technology partner, explores ways the security community is fighting cybercrime—from blockchain analytics to advanced prevention techniques.
View the episode on Vimeo.
Are you certain your organization is fully protected? If you aren’t sure, the security experts at Aunalytics can help you determine your organization’s risk. We offer a complete suite of managed security services and maintain a highly secure cloud environment utilizing security best practices. Aunalytics partners with leading technologies in the security field, such as Sophos, to ensure that your organization always stays a step ahead of hackers and other bad actors. Don’t leave your organization vulnerable—contact Aunalytics today.
Think You Know Ransomware? The Faces of Cybercrime: The Hunters and The Hunted
Ransomware attacks are not simply a nuisance—a single attack can affect thousands of computers and servers, cost companies huge sums of money, or prevent businesses from operating altogether. And it’s not just large corporations that are at risk. Governments, universities, police forces, healthcare organizations, and even small businesses are brought to their knees by cybercrime. Anyone can be a victim—it can be as simple as one person clicking on a malicious link in an email.
Once attacked, organizations are faced with a dilemma. Either pay a large ransom and hope the attacker will actually provide the key to recover their data, or try to mitigate the loss of data on their own, which can be expensive and extremely time consuming. Yet, even if an organization chooses to pay a ransom to recover data right away, they will likely still face negative consequences from the breech, including lost productivity, risk of litigation, and loss of customer trust.
Despite the magnitude of this issue, it has been very difficult for authorities to catch and prosecute cybercriminals. In fact, the problem is only getting worse as these individuals continue to succeed in making large sums of money from the comfort of their own homes—without facing any consequences.
Why are cybercriminals able to flourish, and what can we do to stop them? Part two of Sophos‘ documentary series on ransomware explores the risks of cybercrime to organizations both large and small, and examines the various factors that have led to an increase in ransomware attacks.
View the episode on Vimeo.
Are you certain your organization is fully protected? If you aren’t sure, the security experts at Aunalytics can help you determine your organization’s risk. We offer a complete suite of managed security services and maintain a highly secure cloud environment utilizing security best practices. Aunalytics partners with leading technologies in the security field, such as Sophos, to ensure that your organization always stays a step ahead of hackers and other bad actors. Don’t leave your organization vulnerable—contact Aunalytics today.
Think You Know Ransomware? The Origins of Cybercrime
How well do you know ransomware? Security hacks and ransomware attacks are constantly in the news. In fact, in June 2023, a zero-day vulnerability in Progress Software’s MOVEit Transfer managed file transfer (MFT) product affected over 130 organizations and millions of individuals. And that is only the latest in a constant stream of cybercrime.
Since the advent of the internet, hackers have been developing increasingly sophisticated attacks. But what is most concerning may be that what was once only achievable by highly-skilled hackers is now accessible to anyone. Would-be cybercriminals can easily access the tools and knowledge via the internet to mount an attack. Currently, that most often takes the shape of a ransomware attack—which makes any industry with data a target. Despite this fact, many organizations and individuals continue to remain vulnerable.

Sophos, a leading security software and hardware company, and one of Aunalytics’ technology partners, has released a three-part documentary series examining the history of cybercrime and how it affects everyone—from small businesses to local and national governments. The first episode examines origins of cybercrime and explores why many interconnected systems are susceptible to ransomware attacks. Watch it below:
View the episode on Vimeo.
Are you certain your organization is fully protected? If you aren’t sure, the security experts at Aunalytics can help you determine your organization’s risk. We offer a complete suite of managed security services and maintain a highly secure cloud environment utilizing security best practices. Aunalytics partners with leading technologies in the security field, such as Sophos, to ensure that your organization always stays a step ahead of hackers and other bad actors. Don’t leave your organization vulnerable—contact Aunalytics today.
Local and State Government Cyberattacks Prove that Security is a Necessity
Cyberattacks are a constant threat to organizations of all sizes. State and local governments are no different, having experienced significantly more cyberattacks than they did in previous years, and are at very high risk of bad actors slipping into their networks. To gain a better understanding of the current attack environment and track changes over time in ransomware trends, Aunalytics security partner Sophos commissioned an independent, vendor-agnostic survey of 5,600 IT professionals across multiple industries in mid-sized organizations across 31 countries. While it’s true cyber insurance has been playing a greater role in helping organizations improve their ability to recover from attacks, survey responses clearly indicate that ransomware poses a rising threat to government organizations.
Government Cyberattacks Increase From Previous Years
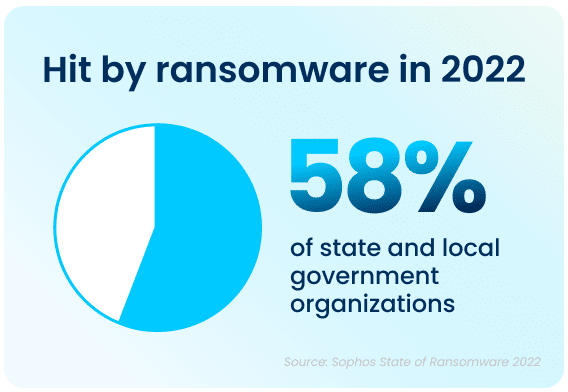
Ransomware attacks have increased significantly over the past year—58% of state and local government organizations surveyed were hit by an attack in 2021, up 70% from 2020. Bad actors are now considerably more capable of attacking organizations and executing harmful tactics at scale. The Ransomware-as-a-Service (RaaS) model is one cause of last year’s increased attacks, as the required skill level for bad actors to hamper the day-to-day operations of an organization has gone down significantly.
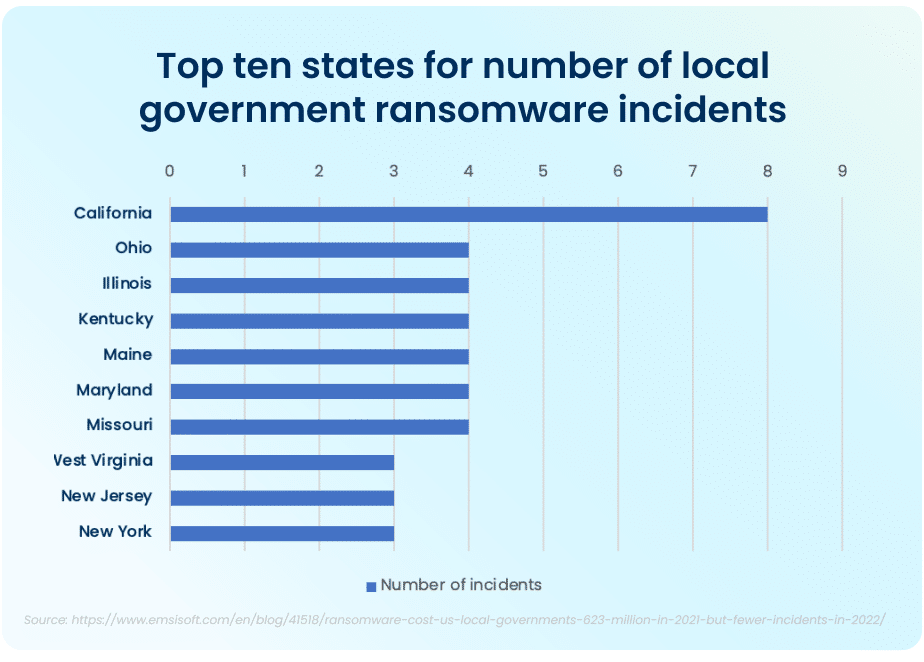
The top ten states that had to deal with the maximum amount of total ransomware attacks in the public sector in 2021 were California, who experienced the most attacks total, Ohio, Illinois, Kentucky, Maine, Maryland, and Missouri. While California took the lion’s share of attacks, with 8 major ransomware incidents, the other six states had four major incidents each.
FBI Cyber Division Survey Lists Examples of Ransomware Attacks
The Federal Bureau of Investigation (FBI) Cyber Division lists examples of several ransomware attacks that impacted state and local government organizations in their 2022 Private Industry Notification. This list contains evidence showing the impact these attacks can have on local communities.
For example, in January 2022, following a ransomware attack, a US county had to take all their systems offline and close all public locations in order to run an emergency response plan and restore all their data from backups. This action disabled all the cameras in the local county jail and deactivated automatic doors, resulting in severe safety concerns and a complete lockdown of the facility. A different county had their data—with residential and personal data—held ransom in an attack. When the ransom was not paid, all of the data was posted on the Dark Web in retaliation.
Rising Complexity of Ransomware Attacks
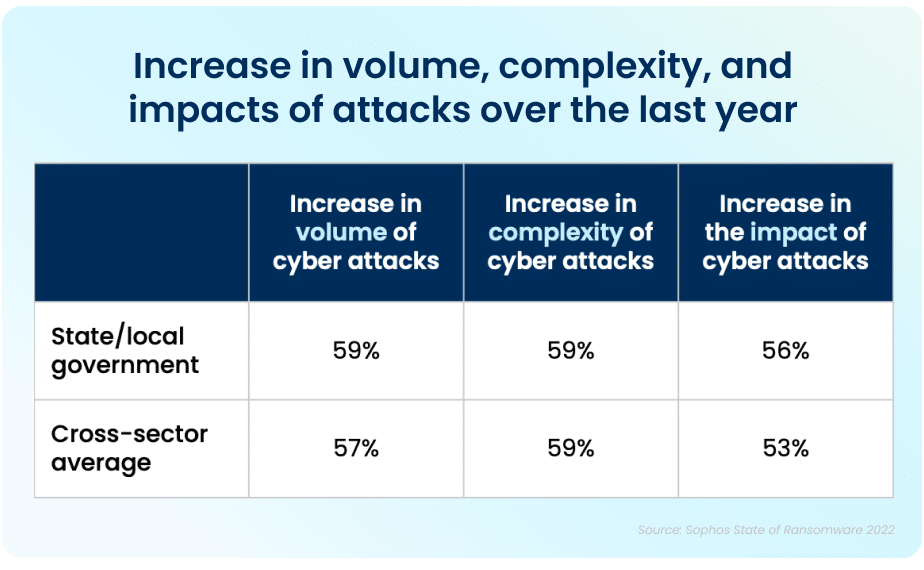
Apart from the rising prevalence of these attacks, the sheer complexity of each attack is also on an upwards trajectory. While the manufacturing and production industry reported the lowest rate of ransomware attacks, over half of all respondents reported their organization was injured by bad actors. The reality is that every organization is at high risk of cyberattack. In 2021, 59% percent of government organizations who experienced cyberattacks saw the complexity of the attacks increase, while a similar 59% saw an increase in the overall volume of cyberattacks.
Data Recovery Rates Are Improving
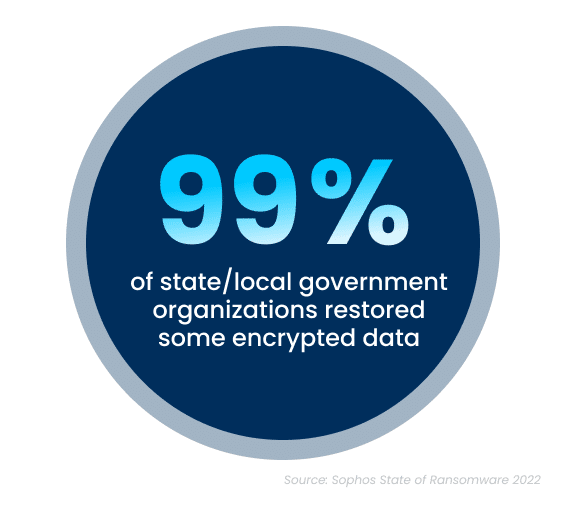
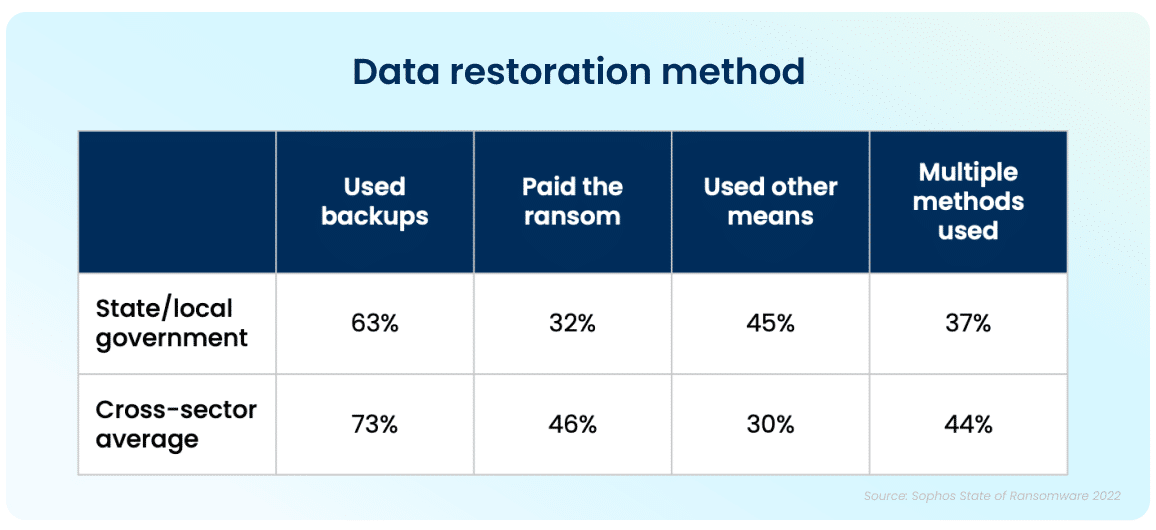
While the increase in cyberattacks paints a bleak picture, there is a silver lining to this dark cloud. Ninety-nine percent of government organizations were able to get at least some of their encrypted data back. The top method used to restore data was performed via existing backups, which were used by 63% of organizations whose data was encrypted in an attack. Unfortunately, despite the utilization of backups, 32% of the affected organizations still had to pay a ransom to ensure that more of their data was restored.
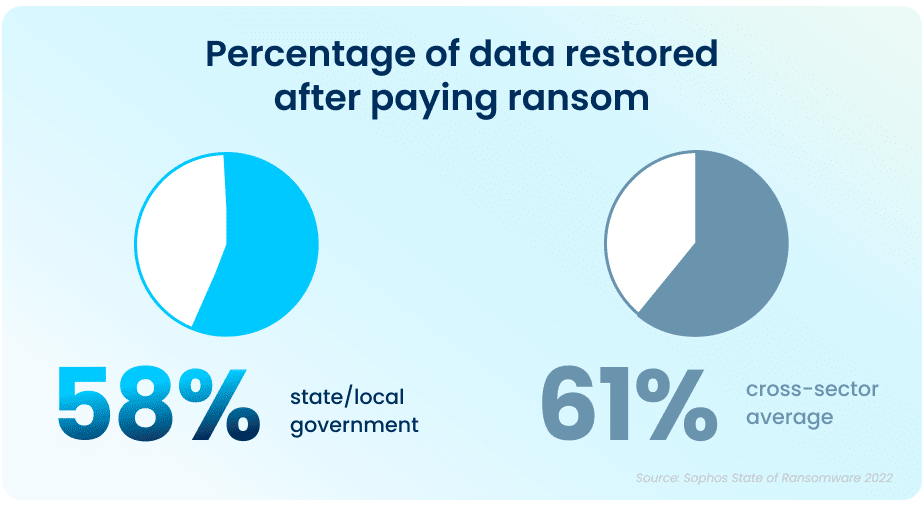
While paying a ransom typically allows organizations to get some data back, it is proving to be less effective than in years past. On average, in 2021, organizations that paid a ransom only got back 58% of their data, a considerable drop from 70% in 2020.
In April and June 2022, respectively, the states of North Carolina and Florida were the first states to prohibit state and local government organizations from paying ransoms to any bad actors. Arizona, Pennsylvania, Texas and New York are considering similar legislation. While the exact impact of this cannot be determined yet, this is expected to dissuade ransomware attacks on all organizations.
This highlights the importance of employing multiple methods to restore data—utilizing backups in particular can improve the speed of recovery and increase the amount of data that can be recovered in the event of an attack.
But It Doesn’t End There
The Sophos State of Ransomware In State and Local Government 2022 survey has revealed that ransomware continues to be an imminent threat for state and local government organizations. For many, choosing to work with an experienced partner with expertise in cybersecurity not only improves your chances of getting approved for the right amount of cyber insurance coverage, but can also ensure that companies see a higher return on investment, and improved ability to both prevent and mitigate attacks in the future. Aunalytics provides Disaster Recovery Services, which is further coupled with a comprehensive backup and archival strategy. This allows state and local government organizations like yours to remain confident so that you are prepared should you encounter a disaster event. We partner with industry leaders to replicate your critical infrastructure so you are prepared for anything.
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
While advancing technology offers significant benefits, it has also made it easier for those who seek to gain an advantage by exploiting others. An attack can be devastating for any business and impact it for many years to come—today’s organizations need to move toward security maturity by utilizing multiple lines of defense against cybercrime.
Fill out the form below to receive a link to the article.
Aunalytics is a data platform company. We deliver insights as a service to answer your most important IT and business questions.
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
While advancing technology offers significant benefits, it has also made it easier for those who seek to gain an advantage by exploiting others. An attack can be devastating for any business and impact it for many years to come—today’s organizations need to move toward security maturity by utilizing multiple lines of defense against cybercrime.