The State of Ransomware in Financial Services 2022 - PDF
The State of Ransomware in Financial Services 2022
Related Content
Nothing found.
4 Questions Mid-market Companies Should Ask Themselves About Data Protection
4 Questions Mid-market Companies Should Ask Themselves About Data Protection
 When the working world went remote due to the COVID-19 pandemic, many never returned to the office. This created new data-security challenges for many businesses, with an increasing amount of sensitive data now being stowed in the cloud, and workers continuing to access company data from off-site locations.
When the working world went remote due to the COVID-19 pandemic, many never returned to the office. This created new data-security challenges for many businesses, with an increasing amount of sensitive data now being stowed in the cloud, and workers continuing to access company data from off-site locations.
How safe is cloud security, which now often relies on “zero trust” security principles based on a user’s location rather than user credentials? While some worry that cloud security is less reliable than on-premise security, that’s not actually the case, particularly for mid-market businesses. The fact is that your data is actually more secure in a remote data center managed by security experts than by your in-house IT team.
You may feel a false sense of security by having your IT department guard your servers in a closet — but this strategy is extremely risky when it comes to data protection. It’s not standard for mid-market IT departments to possess expert skills in cloud security and data security, which are needed to properly safeguard data. Many mid-market companies, particularly those not in highly regulated industries, do not currently have Security Operations Centers.

To read more, please fill out the form below:
Learn More
Nothing found.
4 Questions Mid-market Companies Should Ask Themselves About Data Protection
4 Questions Mid-market Companies Should Ask Themselves About Data Protection
 When the working world went remote due to the COVID-19 pandemic, many never returned to the office. This created new data-security challenges for many businesses, with an increasing amount of sensitive data now being stowed in the cloud, and workers continuing to access company data from off-site locations.
When the working world went remote due to the COVID-19 pandemic, many never returned to the office. This created new data-security challenges for many businesses, with an increasing amount of sensitive data now being stowed in the cloud, and workers continuing to access company data from off-site locations.
How safe is cloud security, which now often relies on “zero trust” security principles based on a user’s location rather than user credentials? While some worry that cloud security is less reliable than on-premise security, that’s not actually the case, particularly for mid-market businesses. The fact is that your data is actually more secure in a remote data center managed by security experts than by your in-house IT team.
You may feel a false sense of security by having your IT department guard your servers in a closet — but this strategy is extremely risky when it comes to data protection. It’s not standard for mid-market IT departments to possess expert skills in cloud security and data security, which are needed to properly safeguard data. Many mid-market companies, particularly those not in highly regulated industries, do not currently have Security Operations Centers.
What’s more, it came to light at the end of 2021 that cyber-insurance renewals are becoming at times prohibitively expensive for all industries due to the exponential increase in cyber-attacks seen last year. The only way for mid-market companies in all industries to lower cyber-insurance premiums and ensure coverage is to implement enhanced data security measures.
Since data protection has become the most prevalent challenge in the cybersecurity market, it’s no surprise to see that according to Insights for Professionals, data protection is the main focus in 2022 for 85 percent of businesses surveyed; 37 percent plan to invest up to $500,000 on data protection in 2022, and 31 percent plan to invest more than $500,000 on data protection over the next 18 months. McKinsey also reports that 85 percent of midsize enterprises plan to boost their IT security spend until 2023.
All-Time High Cybercrime
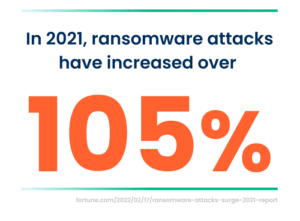 Still, it would be misleading to imply that cloud security comes with no challenges. One of the biggest ongoing concerns are ransomware attacks, which increased over 105 percent in 2021. Cybercriminals continue to attain new levels of sophistication, with payment demands skyrocketing into tens of millions of dollars. According to McKinsey, the costs related to cybercrime will continue to ascend in the coming years, with a 15 percent yearly increase leading to cybercrime costs reaching $10.5 trillion a year in 2025. Looking ahead over the next decade, by 2031, Cybersecurity Ventures estimates ransomware costs alone should reach $265 billion.
Still, it would be misleading to imply that cloud security comes with no challenges. One of the biggest ongoing concerns are ransomware attacks, which increased over 105 percent in 2021. Cybercriminals continue to attain new levels of sophistication, with payment demands skyrocketing into tens of millions of dollars. According to McKinsey, the costs related to cybercrime will continue to ascend in the coming years, with a 15 percent yearly increase leading to cybercrime costs reaching $10.5 trillion a year in 2025. Looking ahead over the next decade, by 2031, Cybersecurity Ventures estimates ransomware costs alone should reach $265 billion.
McKinsey reports that there are multiple motivations for these attacks, headed by the fact that pandemic-weary companies have become ripe for security vulnerabilities. Also, as advancing digitization continues to drive connectivity and employees now log in from anywhere — including unsecured home networks — it makes life easier for ransomware hackers. The traditional smash and grab approach is now being replaced with bad actors “dwelling” undetected within victims’ environments, which gives cybercriminals the lay of the land in understanding where the highest value information resides before selling it to the highest bidder.
Another motivation for the continued attacks is their success: as more companies are forced to pay ransoms, hackers are further incentivized to build on their well-paid victories and continue innovating on this lucrative threat. Specific sectors are particularly at risk; keep in mind that in the U.S., supply-chain attacks rose 42 percent in Q1 of 2021, victimizing as many as 7 million people, while McKinsey shared that “security threats against industrial control systems and operational technology more than tripled in 2020.” The war in Ukraine has taught us lessons about attacks compromising infrastructure, utilities and government that can debilitate nations and be weaponized.
Paying Up
These massive numbers can seem overwhelming, and can also make it difficult to tell how much a ransomware attack can affect an individual company. To give you some perspective, consider these stats:
- NPR reported that Colonial Pipeline paid a $4.4 million ransom after the company shut down operations.
- CNBC reported that global meat producer JBS paid ransomware hackers $11 million.
- Insider reported that global insurance provider CNA Financial forked over a reported mind-blowing $40 million post-cyber-attack.
- The Washington Post reported that a ransomware attack on U.S. software provider Kaseya targeted the firm’s remote-computer-management tool and endangered up to 2,000 companies globally.
These costs are also just the tip of the iceberg for the companies victimized by ransomware hackers. Additional costs of such an attack include everything from paying third parties (like legal, PR, and negotiation firms), not to mention the opportunity costs of having executives, staff, and teams disconnected from their day-to-day roles for weeks or months to deal with the attack’s aftermath. Perhaps the biggest unaccounted-for expense is the resulting lost revenue.
Ask These 4 Questions
What can mid-market companies do in the face of these threats to their data’s safety? They should focus on strategies that address ransomware prevention, preparation, response, and recovery. Since this is an ongoing journey, threats continue to evolve and improve — so it’s critical to keep up to date with new threats of increasing sophistication, while being ready with cybersecurity strategies and best practices. The goal is to continue to build cyber maturity that creates a resilient approach. You may not be able to stop attacks from occurring, but when they do, they won’t have the same impact if you’ve prepared in this way.
As a starting point, these are four questions that every mid-market company should ask itself to determine the organization’s readiness for data defense:
- When it comes to our people, do we have security focused IT leadership, trained cloud security experts, and data security experts?
- When it comes to our process, do we have defined IT security processes for proactively managing the security posture of our environments?
- When it comes to our technology, are we 100 percent confident in our security tech and our ability to actively monitor and detect threats around the clock?
- When it comes to our cloud architecture, are we confident that it allows for scalability without sacrificing security assurances?
If the answer is “no” or “I don’t know” to any of these questions, it is time to get your house in order — you are at risk. To stay alive, compete, and drive value, mid-market companies should shift their focus to data analytics, data management, security, and compliance. This requires a cloud-based data center, a cloud-native data management platform, and cloud-native analytics. Ensuring the right infrastructure to maximize the capabilities of data centers — and how they are able to manage and store data — is crucial to effective mid-market digital transformation.
Learn More
Nothing found.
Lowering Cybersecurity Insurance Premiums with Managed Security Services
Lowering Cybersecurity Insurance Premiums with Managed Security Services
Midmarket organizations face the threat of cyberattacks that put every organization at great risk. As a result, a greater number of IT professionals are turning to managed security services to lower cybersecurity insurance premiums.
Fill out the form below to receive a link to the article.
Aunalytics is a data platform company. We deliver insights as a service to answer your most important IT and business questions.
Featured Content
Nothing found.
Lowering Cybersecurity Insurance Premiums with Managed Security Services - PDF
Lowering Cybersecurity Insurance Premiums with Managed Security Services
Midmarket organizations face the threat of cyberattacks that put every organization at great risk. As a result, a greater number of IT professionals are turning to managed security services to lower cybersecurity insurance premiums.
Related Content
Nothing found.
What Mid-Market Companies Need for Data-Driven Success and How to Get It
What Mid-Market Companies Need for Data-Driven Success and How to Get It
Using your data as an asset to drive competitive business growth and achieve cost cutting operational efficiencies is imperative for a company to compete, survive, and thrive. Increasingly, data and analytics have become a primary driver of business strategy and the potential of data-driven business strategies is greater today than ever.
Related Content
Nothing found.
Aunalytics Managed IT Services Safeguard Logan County Ohio Against Disruptive Weather, Cyber, and Pandemic Events
Aunalytics Managed IT Services Safeguard Logan County Ohio Against Disruptive Weather, Cyber, and Pandemic Events
Fill out the form below to receive an email with a link to the case study.
Aunalytics is a data platform company. We deliver insights as a service to answer your most important IT and business questions.
Featured Content
Nothing found.
Aunalytics Managed IT Services Safeguard Logan County Ohio Against Disruptive Weather, Cyber, and Pandemic Events - PDF
Aunalytics Managed IT Services Safeguard Logan County Ohio Against Disruptive Weather, Cyber, and Pandemic Events
Related Content
Nothing found.
Ransomware Attacks Now Target Community Businesses
If you think that your business will not be a target for ransomware attackers, think again. This is no longer a problem only for large enterprises—now, ransomware attacks target community businesses as well.
The Battle Creek, Michigan community woke up to a May Day attack that forced its Kellogg Community College (KCC) to close all operations. In the middle of preparations for final exams, all five campuses serving approximately 6900 students closed and all operations came to a screaming halt.
The community college posted alerts on its website and social media:
Eric Greene, the Vice President for Strategy, Relations, and Communications at KCC said: “We are still working to understand the full extent of this incident, but as soon as we became aware of it, we immediately assembled a multi-disciplinary team and engaged independent legal counsel and external forensic experts.”
Greene continued, “KCC had backups in place, and we are working systematically with our IT experts to restore our operations.” But even though KCC had backups, “As a precautionary measure, all campuses have been disconnected and our systems will remain offline until they are deemed secure by our IT experts. As a result, our students and staff might experience delays accessing our services, including campus emails, online classes, and resources,” Greene said.
Back-ups alone are not sufficient to prevent business disruption when a ransomware attack hits. Preventing the attack, rather than having to respond to it, is key. KCC remained closed for three days while IT scrambled. All computer access to university systems had to be shut down in an attempt to stop further damage. The response and mitigation included a forced password reset for all students, faculty and staff, and adding multi-factor authentication (MFA) for all users.
Enable Multi-factor Authentication
MFA is an important security measure when people access systems remotely. It provides an extra level of verification to make sure that the user attempting to access the system is really an authorized user and not a bad actor trying to get in. Modern business regularly includes employees logging in from home, travel and mobile devices to access data and systems from their organization. As such, the old firewall security perimeter around your place of business does not protect you. Modern security requires focus on users and access. MFA is something that is easy to add to your security stack. The protection benefit from MFA far outweighs the resource cost of installing and using the technology. Really, there is no excuse for not having MFA in today’s threat landscape. It is standard.
So if you do nothing else this year to improve your security posture, add MFA. But considering that community businesses are becoming targets for cybercrimes, unless you can afford a complete shut-down of your business, it is becoming a must to have modern security technologies (including robust monitoring so that you are equipped to prevent attacks and are better positioned to respond and mitigate), in addition to back-up and disaster recovery plans.
Shift Applications to the Cloud
Mid-market businesses are shifting security and data center responsibilities from on premise servers and security maintained by their IT department, to partnering with cloud experts who run data centers, keeping client systems stable and secure as their full time business. The trend with line of business applications used by your team for daily operations is cloud. As more and more community businesses use cloud based apps for functions like accounting, customer portals, ERP, CRM and HR, having cloud experts with the tools and the skills to be able to secure your organization’s data (from multiple sources) for safe use by remote users makes more sense than trying to build a security fortress yourself at your place of business.
Partner with Experts
If cybersecurity is not your main line of business, partner with security experts unless you want cybersecurity to become your main line of business. It will consume your resources to stay current with emerging threats, protective means, 24/7/365 monitoring, best practices and constantly evolving security measures. The ever increasing sophistication and volume of attacks has shifted the answer to the “buy it or build it” question for this critical business service from the solution being your in-house IT department to the solution requiring managed security services to supplement your in-house IT team.
Don’t become the next ransomware attack headline. Community businesses can take steps to avoid ransomware attacks. An ounce of prevention, after all, is less costly than the cost of operational shut-down, PR scramble, customer service disruption, brand reputation tarnishment, and emergency security consultant fees paid when you are in the middle of an attack that succeeded.
Managed IT Services and Data Recovery Offerings from Aunalytics Solve Emergency IT Challenges for EMI
 Over the past several years, information technology has taken center stage at Ohio-based landscaping company Environmental Management Inc. (EMI). Established more than two decades ago, EMI has grown to be one of the largest landscape companies in Central Ohio. Serving major business and governmental customers throughout the region, EMI continues to grow, thereby increasing demand for managed IT services in multiple business areas.
Over the past several years, information technology has taken center stage at Ohio-based landscaping company Environmental Management Inc. (EMI). Established more than two decades ago, EMI has grown to be one of the largest landscape companies in Central Ohio. Serving major business and governmental customers throughout the region, EMI continues to grow, thereby increasing demand for managed IT services in multiple business areas.
Managing business-critical IT environments is a time-consuming process that many times can require specialists with the experience to deliver the highest performing infrastructure possible. EMI has seen this first-hand over the past several years as the company has had to recover from destroyed network infrastructure caused by a catastrophic lightning strike, a disruptive cyberattack involving ransomware with the encryption of important company information, and the need to reconfigure its computing endpoints quickly because of the occurrence of Covid-19 to accommodate “work from home” environments for its team.
Aunalytics provides a broad range of managed IT solutions, including network, server management, and PC management, as well as Office 365, data recovery and business continuity support. EMI employed several services which have helped to positively transform the company’s operations.
The side-by-side support model employed by Aunalytics has been an especially impactful benefit of this partnership. “While there are many important services provided, perhaps the most widely used and important for EMI is the 24×7 help desk which is essentially an IT department on demand,” said Tom Kiefer, CFO for EMI. “Whether it’s an employee who accidentally deleted a file or a catastrophic lightning strike, the team behind the Aunalytics Ohio help desk has been insightful and fast to act, allowing our employees to remain online and productive.”
Read the full case study to see how EMI further benefitted from the managed IT and data recovery services provided by Aunalytics Ohio.