Cloud or On-Prem Servers—Which Is Better for Your Company?
Every organization needs to manage its data to get its desired business outcomes. For a company to access its data and use it in day-to-day operations, dashboards, reporting, and data analytics, it either needs a cloud or on-premises solution to facilitate compute, storage, and data management strategies.
What’s The Difference Between The Cloud And On-Premises Data Storage?
An on-premises data server is hardware that you maintain on your company’s premises for storing, processing, and accessing information through your organization’s networks. An in-house IT department is needed to maintain, turn over/replace, and upgrade the hardware, keep it stable and operational, and secure it.
A cloud storage solution run by an expert and backed by a cutting-edge data center provides the same functions as an on-premises server and more. It does not exist on your company’s premises and the data on it is accessed through the internet. All updates and maintenance tasks are performed by the cloud provider, who owns and operates its own hyper-secure data centers to safeguard your data in case of failure, cyberattack, or outage. Like on-premises servers, access to cloud data can be set by administrators to be permission-based to allow access only by authorized personnel.
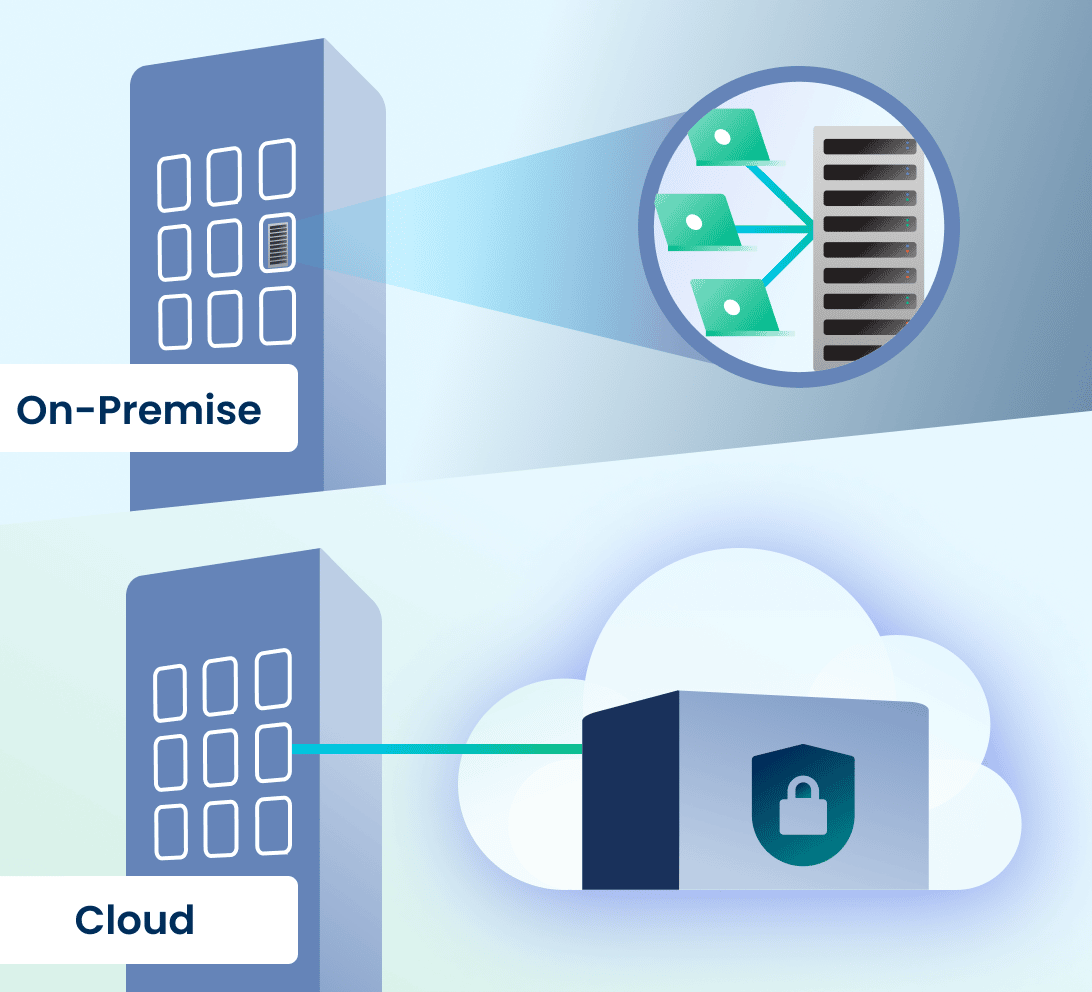
On-Premises vs. Cloud—Which Option Best Suits Modern Business Needs?
There are more factors when choosing between using a cloud computing solution or keeping servers on-premises, including customizability and scalability, security concerns, and the budget for your organization’s data management strategy. While on-premises data servers regularly require hardware upgrades in your physical locations to expand alongside your business’s growing needs, a cloud storage and computing solution with access to highly advanced data centers is scalable based upon your workload. Unlike an on-premises server that can take a lot of time and money to set up and ready for operation, cloud service providers ensure you can access your cloud for computing and storage needs almost instantly.
In some mid-sized companies, server rooms tend to be used for multiple purposes, which means that they are sometimes unlocked, unsecured, and allow for unauthorized access that compromises data security. Many mid-sized companies do not have 24/7/365 monitoring of their server rooms, specialized climate controls needed for a data center, and do not consistently deploy or regularly schedule hardware upgrades to keep the systems reliable before something goes down.
One mid-market employee shares the story of a server closet that her company had in a previous workplace. For starters, it could be accessed by nearly every employee of the company. She recounted that the IT department placed portable dehumidifiers in the room to keep moisture down. The IT department’s regular practice was to empty the server closet dehumidifiers in the office’s kitchen sink. Unfortunately, a new IT employee happened to trip while carrying one of the dehumidifiers and spilled water all over the server room. Every employee of the company was affected—they found out that the work they had done since the last backup, which happened to be 5 days ago, had disappeared. Even worse, their servers were down for several days after the incident, further impacting their daily business operations.
Although in the past, people feared that cloud would not be secure, or a company would lose control over its data—cloud has proven to be more secure than on-premises hardware. First, cloud vendors host their own data centers and because this is their main business, they have cutting-edge climate control environments to protect their clients’ data. Cloud vendors adhere to frequent hardware replacement turn-over schedules to keep uptime maximized and cloud operations state-of-the-art. Cloud vendors monitor their data centers 24/7/365, are security experts, and have strict controls in place in order to service clients in highly regulated industries with rigorous data security needs. For most mid-sized businesses, it is more cost effective to rely upon the expertise of a cloud vendor for data security and uptime than to host and maintain its own servers, stay on top of the latest security threats, and staff its data center (or data closet) for monitoring to prevent downtime and security breaches.
Large enterprises often can afford to build their own data centers providing them an alternative to an external cloud provider. However, this is incredibly expensive and can set organizations back by USD $10-25 million on yearly setup and operation costs. This infrastructure also takes a lot of time to be implemented and in today’s fast-paced business environment, this might not be entirely acceptable for decision-makers.
Yet, even for enterprises, on-premises solutions no longer make the most sense. Most modern business applications are cloud-native. Cutting-edge data analytics solutions are cloud-native and connect and integrate data sources using cloud technologies. Clouds are better suited for analytics than on-premises hardware, due to scalability and ability to absorb compute spikes (instead of having to invest in hardware with capacity for compute spikes as machine learning algorithms converge—which leads to excess capacity at other times).
According to Insights for Professionals, 63% of senior IT leaders and company executives who were surveyed expected to invest in cloud infrastructure-as-a-service in 2022. Considering the state of on-premises servers, which are becoming an obsolete technology that require an IT department to keep a constant eye on it, cloud technology is a natural progression in infrastructure for better data management. Gartner reports by 2025 almost 85% of companies will have moved to a cloud-first approach. Cloud technology has now evolved to a point where it provides better stability and security at a more economical price than on-premises solutions.
Mid-Market Company Considerations
Many organizations are operating in hybrid and multi-cloud environments. This means that they have some data in on-site servers, some data in cloud based line of business applications (relying on the application provider for data storage in whichever cloud the application vendor uses for its product), and many have some data in a public cloud.
However, mid-market companies have added considerations when choosing a cloud solution. Most public cloud service providers do not offer data management services. You need to do this yourself. Yet, mid-market companies often do not have this expert talent in-house. For success, mid-market companies need a cloud hyper-scaler that also provides data engineering services to build data connectors and pipelines, warehouses, data lakes, and the like. This skill set is different from a typical IT employee. Hyper-scalers—who can help organizations with data management, transform data from disparate sources into a decision and analytics-ready status, and bring transactional data into the forefront using a cost-effective cloud solution—tend to be private cloud vendors. For this reason, private cloud solutions make more sense than public cloud for mid-sized organizations.

A side-by-side partnership with an experienced cloud-native data platform company will have a measurable and positive impact on mid-market company data management strategies, with built-in access to technical resources and experts, so that your company does not need to hire new FTEs to support data management. Rely on the data management companies for data management so that your company can focus on your main line of business.
Aunalytics’ high performance private cloud provides a highly redundant and scalable platform for hosting servers, data, analytics, and applications at any performance level. Aunalytics delivers data management in a side-by-side service model, bringing companies the technology and the talent needed for data management success. To learn more about our Enterprise Cloud solution, click here.
Don’t Ghost Your Network—Begin Your Security Maturity Journey
Is your security keeping up with the rapidly changing threat landscape? If not, your security is becoming more obsolete by the day—and more vulnerable to scary things like hackers and ransomware by the second. When a company is fully protected with the most up to date hardware, software, monitoring, and consistent patching it begins to reach security maturity.
Security maturity is a consistent state of awareness concerning your network security and can only be achieved when you:
- Have an SOC to monitor and remediate threats
- Have looped vulnerability management
- Employ active defense with security intelligence from multiple sources to protect applications, networks, servers and workstations
- Are willing to adapt your security environment to new and changing threats on a constant basis, and more.

Be Proactive
Instead of relying on a passive security model—or worse, waiting until after a companywide infection—take an active role in your company’s security. The main goal of security maturity is to avoid or reduce the number of security incidents haunting your network. It’s kind of like painting San Francisco’s Golden Gate Bridge. As soon as the painting crew gets from one end to the other with a fresh coat of paint, it is time to start again to repaint the bridge. Security maturity requires constant action and change as your organization adapts to protect against the latest evolving threats.
We all observed remote work access change security and IT on a mass scale in 2020, and security changes continue to become more necessary as bad actors and threats become more and more dangerous to your business as it continues to grow and change—and more dangerous for your customers to do business with you.
October WSJ headlines highlight a Chicago healthcare system, one of the largest in the U.S., being the victim of ransomware that is forcing it to shut down electronic records, systems, and cancel patient appointments. It is now working with law enforcement and outside cybersecurity experts to remediate. A security maturity journey is hard to make on your own, and a good partner can ensure you are meeting the highest security standards possible. Here at Aunalytics, we include security in everything we do because we believe it is a basic building block of IT.
Find A Trusted Security Partner
Without a secure network, you cannot even begin to consider moving further into a security maturity journey. Fortunately, a partner can give you the peace of mind that you will be working with a talented security team that is watching your network 24/7/365, helping to ensure bad actors are caught and eradicated before your company is compromised.
A standard, one size fits all security solution simply doesn’t work anymore—it often leaves cracks, holes, and even chasms for hackers and cyberattacks to slip through. You can improve your journey from cybersecurity to security maturity with a trusted partner.
Click here to learn more.
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Does Your Mid-Market Firm Have the Right Talent to Maximize Its Data Tech Investments?
Investing in digital transformation technologies can be a waste of money if your company forgets one important point. That point is, no matter how cutting edge the tech or tool may be, people are needed with specific technical expertise in order to derive true business value from these investments.
Unlike large enterprises, mid-market companies often try to find this expertise in their IT manager, hoping a jack-of-all-trades approach will take care of it. This is an unfortunate mistake, since it would require the IT manager to have unusual command over a long laundry list of duties, from data integration, ingestion, and preparation to data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on-premises environments. This is not just a tall order for a mid-market IT manager to pull off, but likely an impossible one.

At the same time, it’s unreasonable to expect that most mid-market firms can hire an entire division of data experts—who each need to be highly compensated—in order to achieve the organization’s digital transformation goals. Even if a mid-market player could afford it—which is unlikely to make economic sense—these talent resources are scarce and in high demand.
If you’re still wondering whether your IT manager’s skill set, leveraged by your in-house IT technicians, can properly run the gamut required to achieve value from your data technology investments, consider that the person in this position would need the ability to master a wide range of skill sets, from cloud architecture, database engineering, and master data management to data quality, data profiling, and data cleansing. More specifically, your IT manager would need to take on five additional specialized roles for technical talent that are critical for achieving value from data technology investments.
These roles are:
Chief Data Officer/Chief Digital Officer
A chief data officer (CDO) is focused on—you got it—data. Most mid-market companies understandably don’t have a CDO, which means they don’t have anyone who assures regulatory compliance for data handling while managing and exploiting information assets, reducing uncertainty and risk, and applying data and analytics to drive cost optimization and revenue objectives. For IT managers to fulfill a CDO role, they’d have to be equipped to bring a global perspective to company data, help their organization gain competitive advantage over peers, and manage data and analytics. They’d also need the ability to secure data, transform it into valuable business information, lead digital transformation initiatives, and use data for growth and operational efficiency.
Cloud Engineer
The primary job of a cloud engineer is to keep cloud data centers operational and secure for ecosystem users to be able to store and access their data. Cloud engineers are experts in minimizing downtime, managing access to data, managing compute and storage, and setting up cloud architectures for clients, tenants, and containers. They also monitor data center hardware, servers, networks, and communications systems for operational continuity and efficiency.
Data Security Expert
Mid-market firms also need a way to channel the talents of a data security expert, CISO, or cybersecurity director to ensure cyber-security for the company’s data. Data security experts must keep current on emerging threats while executing data security strategies to fend off and remediate attacks. This involves a wide range of duties, including working closely with the IT team to run the company’s Security Operations Center (SOC), constantly monitoring servers, networks, and workstations for security threats, and staying up to date on the changing compliance laws and regulations for the business, to name a few. While larger IT teams have bandwidth to fill cybersecurity needs inhouse, many midmarket IT teams do not have capacity for the 24/7/365 monitoring and security edits needed to thwart attacks, let alone bandwidth for executing on mitigation and response strategies needed to overcome them.
Data Engineer
A data engineer’s primary job is to prepare data for analysis or operational uses, which involves integrating data from different sources, as well as implementing and executing data profiling, cleansing, transforming, and normalizing data. Data engineers also work with data in motion and use master data management to ensure data consistency across an organization. Finally, a data engineer is your go-to technical resource for database construction and management, helping to optimize the company’s data ecosystem.
Data Scientist
It should be clear now why a mid-market IT manager should not be expected to take on these additional professional roles, but in case there’s any doubt, keep in mind that a data scientist is also needed. Data scientists develop algorithms and leverage deep learning models to analyze data with artificial intelligence and machine learning. The data scientist creates the “brain” of the data analytics solution to position it for providing accurate answers based on business information. Data scientists also mine data to find opportunities for business growth and efficiency. Ideally, the data scientist uses tools that enable non-technical business users to query data sets without having to write SQL or other code.
Master of One
If you’ve correctly determined that your mid-market IT department does not have enough time to absorb these data roles into their regular duties of keeping your company systems stable and responding to help desk tickets from your team, don’t despair. There’s a viable solution for mid-market businesses with this dilemma: they can partner with data experts who provide a side-by-side model coupling technology with talent. This allows the mid-market to efficiently compete, leveraging the necessary skillsets to achieve digital transformation success.
What does successful mid-market digital transformation require? The key is to have a cloud-based data center, a cloud native data management platform, and cloud native analytics, thus shifting the burden of procuring and maintaining the infrastructure to a third-party vendor in the data industry. Instead of attempting to reinvent the wheel in house, mid-market players should ensure they’re partnered with the right infrastructure to maximize the data-center capabilities, and data storage and management, for effective digital transformation.
Mid-market firms can gain the benefits of working with a wide range of experts including cloud engineers, data engineers, security experts, data scientists, and other highly skilled technical resources if they establish a partnership with a data platform company. By opting for this type of side-by-side expert help, the mid-market can achieve true business value—without needing to hire an entire data team.
Learn More
Bridging the Mid-Market Talent Gap for Digital Transformation
Bridging the Mid-Market Talent Gap for Digital Transformation
To achieve business value from data technology investments, mid-market companies need the right technical expertise and talent. Yet many mid-market firms push this onto their IT manager, assuming that since it is technology related, IT has it. This is a mistake because most IT departments do not have time for data analytics. They are busy full time keeping company systems stable and secure, and providing support to your team members. This by necessity results in IT deprioritizing data queries over crucial cybersecurity attack prevention. Business analysts and executives get frustrated waiting for data query results, and the data is stale or the business opportunity has passed by the time query results are in.

But even if your IT team had time for it, it still is a mistake to rely on traditional technology administrators for data analytics success. This is unless your IT department has expertise across a wide range of skill sets, from cloud architecture, database engineering, master data management, data quality, data profiling, and data cleansing. What’s more, your IT manager would need to have command over data integration, data ingestion, data preparation, data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on premises environments.
When you read this laundry list of needs, it becomes clear that most mid-market IT departments lack the specialized experts needed to derive business value from their data. Unlike larger enterprises that have the resources to hire skilled staff for these roles, the mid midsize organization requires another option that provides access to the right tools, resources, and support. One that integrates, enriches and is trained in utilizing AI, machine learning, and predictive analytics to achieve more useful results.

To read more, please fill out the form below:
Bridging the Mid-Market Talent Gap for Digital Transformation
Bridging the Mid-Market Talent Gap for Digital Transformation
To achieve business value from data technology investments, mid-market companies need the right technical expertise and talent. Yet many mid-market firms push this onto their IT manager, assuming that since it is technology related, IT has it. This is a mistake because most IT departments do not have time for data analytics. They are busy full time keeping company systems stable and secure, and providing support to your team members. This by necessity results in IT deprioritizing data queries over crucial cybersecurity attack prevention. Business analysts and executives get frustrated waiting for data query results, and the data is stale or the business opportunity has passed by the time query results are in.

But even if your IT team had time for it, it still is a mistake to rely on traditional technology administrators for data analytics success. This is unless your IT department has expertise across a wide range of skill sets, from cloud architecture, database engineering, master data management, data quality, data profiling, and data cleansing. What’s more, your IT manager would need to have command over data integration, data ingestion, data preparation, data security, regulatory compliance, data science, and building pipelines of data ready for executive reporting from multiple cloud and on premises environments.
When you read this laundry list of needs, it becomes clear that most mid-market IT departments lack the specialized experts needed to derive business value from their data. Unlike larger enterprises that have the resources to hire skilled staff for these roles, the midsize organization requires another option that provides access to the right tools, resources, and support. One that integrates, enriches and is trained in utilizing AI, machine learning, and predictive analytics to achieve more useful results.
Achieving Digital Transformation
Digital transformation has been defined by some as the integration of digital technology into all areas of a business, fundamentally changing how employees operate and deliver value to customers. Some of the challenges midsize businesses have with building an internal team to initiate this concept are employee pushback, lack of expertise to lead digitization initiatives, improper organizational structure, the absence of a digitization strategy and limited budget. As an alternative to building an internal operation, a more efficient way for mid-market businesses is to leverage the skillsets of experts by partnering with a consolidated group of experts, leveraging a side-by-side model that couples technology with talent. Look for solution providers that offer the following:
- Powerful cloud data centers paired with engineers skilled in architecting cloud-based applications and processes that better serve critical business requirements. These data centers are optimized for true multi-tenancy, built on seamlessly integrated hardware and software, offer business-driven configurability, world-class security and performant systems.
- Active Monitoring and Thoroughly Integrated Security. Monitoring and security should be pervasive across system infrastructure to defend against cyberattacks and provide remediation when required. Business customers will also expect full-time monitoring and on-demand help desk to address unexpected events. The data management platform underpinning applications should be monitored by experienced data engineers with success in building data warehouses, data lakes, and data pipes. They should also be able to integrate, cleanse, and transform data into decision-ready and analytics-ready business information.
- High ROI Business Insights that Drive Results. Data analytics investments need to provide real business value by giving actionable insights and finding opportunities within your data. With this in mind, data analytics should include access to data scientists and business analysts versed in your industry. These experts should be equipped to design AI-powered algorithms that answer the most pressing questions based on real-world business challenges.
Mid-Market Data Transformation for Enterprise-Class Results
Ensuring the right mix of hardware, software and resulting services are available to maximize the data center capabilities—and their ability to manage and protect data—is crucial to effective mid-market digital transformation. To compete and drive value, the cloud data center provider must deliver at all levels, with customizable business intelligence solutions powered by an effective data management platform that is secure and compliant. Successful mid-market digital transformation thus requires a shift of responsibilities for infrastructure procurement and maintenance to a third-party provider backed by experienced staff and best-in-class infrastructure.
When implementing a digital transformation project, your company gains from the many benefits this brings, such as a higher return on your IT investment, increased employee and customer experience, and greater business agility. This is further enhanced by leveraging experienced cloud engineers, data engineers, security experts, data scientists, and other highly skilled technical resources—achieving true business value from the investment. And by partnering with experts, your company’s time, resources, and innovation can be focused on its core competencies.
Learn More
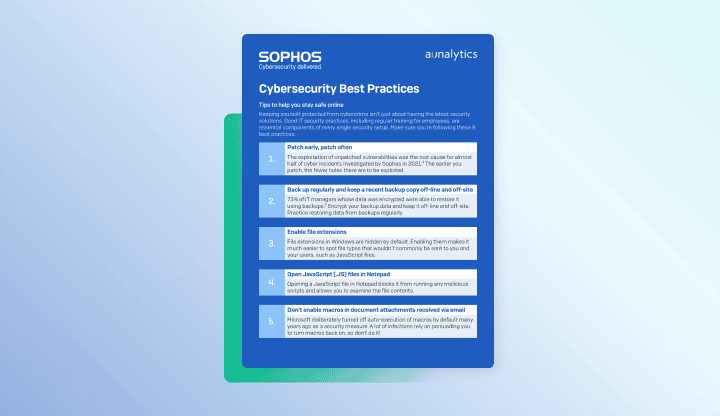
Cybersecurity Best Practices - PDF
Cybersecurity Best Practices
Tips to help you stay safe online
Best Practices for Securing Your Network from Ransomware - PDF
Best Practices for Securing Your Network from Ransomware
Elevate your protection against ransomware and other network attacks
Cybersecurity for you - PDF
Cybersecurity for you
Enterprise-class IT protection for the small- to mid-size company
Unlocking the Value of Data Analytics: What Mid-Market Companies Need to Understand
Unlocking the Value of Data Analytics: What Mid-Market Companies Need to Understand
 Most mid-market companies make one mistake or another when investing in a data analytics platform, not understanding the many intricacies associated with preparing their data to get the best results. Some of the most common mistakes include:
Most mid-market companies make one mistake or another when investing in a data analytics platform, not understanding the many intricacies associated with preparing their data to get the best results. Some of the most common mistakes include:
- Not realizing they need to build pipelines to get the data from their multiple data sources to the analytics platform
- Tasking IT with implementing a data analytics solution, when the IT department does not have data science skillsets
- Basing analytics on data that is riddled with errors, incomplete, or stale, which compromises quality of decision-making due to the inaccuracy and tardiness of the underlying data.
- Relying on the reporting function of one data source and not taking into account data beyond that source for decision-making
- Using dashboards that provide insights into the past only, and not the future – a gap that needs to be bridged to compete with larger enterprises
It should also be noted that analytics requires massive storage and compute to mine data for actionable insights. Even in a cloud environment, which is less costly to maintain than on-premise servers, data analytics takes up a huge amount of compute to mine transactional data for AI-driven insights. Most data warehouses used by mid-market companies are not built for analytics, and their contracts with public cloud vendors for data storage often incur huge overage charges for compute spikes as millions of calculations are being completed for algorithms to converge for analytics results. Data analytics needs a cloud built for analytics. The mid-market should demand a built-in analytics cloud from an analytics solution, without a third-party public cloud contract to make it work (or attempt to host it in their regular institution data storage).
Industry Knowledge is Key
One of the most important aspects to understand is that there is no one-size-fits-all when it comes to data analytics. The value lies in industry specific data models, which must be built with algorithms using salient data points for a specific industry and appropriately weighted for that industry. For example, to build customer revenue in financial services, mining transactional banking data is important to reveal if a customer is doing business with competing financial institutions so that action can be taken to win this business over. In manufacturing, comparing product inventory at various channels and channel or retail sales locations is important for discerning sales performance and growth opportunities. In healthcare, mining insurance reimbursement claims for underpayments to recapture lost revenue requires comparisons of contracted amounts and fee schedules for multiple private insurance companies, plan coverages, and more. The true business value of analytics lies in industry specific data models and the data enrichment made possible by deep learning and the generation of actionable insights.
The Importance of Having the Right Expertise
This brings us to the requirement for data scientists and business analysts, which assist with achieving powerful and current actionable insights that lead to AI-driven decision-making and better business outcomes. Data scientists build algorithms to detect trends, patterns and predictions based upon the data, to position an enterprise for the future. Business analysts are industry specific and connect the dots between the data points relevant for answering business questions in that particular industry. They also help to design dashboards and other data visualizations to ensure that the insights generated answer questions important to that industry using industry-specific terminology, and analyze analytics results in the context of industry knowledge to reveal growth drivers and other opportunities for driving revenue. Typical IT departments do not have these skill sets.
Data Analytics Platform Requirements
Consider these questions when evaluating a data analytics platform:
- Which data sources are forming the basis for the insights: Is the analysis based upon only some of the data, leaving out important data sources? Do the analytics use the most important data points? Is too much data or the wrong data being used?
- How is the data cleansed for accuracy: To judge the accuracy of the insights, know what is being done to eliminate errors in the underlying data being analyzed. Garbage in leads to exponential garbage out when data is turned over to AI. Can the data be trusted?
- Which algorithms are being used to find insights: Is it a specialized or generic deep learning model? Is it optimized for the type of inquiry or result being sought? Is it tailored to a specific industry and weighted appropriately for that industry and the question posed? Can the results be trusted?
- Are the analytics results providing actionable insights such as how to grow revenue, improve efficiency or achieve other business outcomes? Are the results tied to solving business challenges, and not just AI for the sake of being cool?
Side-by-Side Approach
 Most mid-market companies are not in the business of IT or data science. IT is a necessary administrative function for operating a business, but should not become the main focus of most non-tech mid-market companies. However, given the expertise needed to use and maintain most analytics solutions, and the cost of data expert professionals as FTEs, the cost of data management and analytics can quickly overtake mainline business COGS expenses. Given all the complexities and challenges associated with unlocking the true value of data analytics, a new approach is needed that mid-market businesses can afford, enabling them to leverage AI-driven analytics and more effectively compete.
Most mid-market companies are not in the business of IT or data science. IT is a necessary administrative function for operating a business, but should not become the main focus of most non-tech mid-market companies. However, given the expertise needed to use and maintain most analytics solutions, and the cost of data expert professionals as FTEs, the cost of data management and analytics can quickly overtake mainline business COGS expenses. Given all the complexities and challenges associated with unlocking the true value of data analytics, a new approach is needed that mid-market businesses can afford, enabling them to leverage AI-driven analytics and more effectively compete.
A side-by-side service model offers an alternative that goes beyond most tools and platforms on the market by providing a data platform with built-in data management and analytics, as well as access to human intelligence in data engineering, machine learning, and business analytics. Ideally it should operate as a cloud-based platform with a subscription service that places the burden of the data engineering expertise, technical tooling, and building and maintaining the infrastructure on the data management provider.
While many companies offer tools, and many consulting firms can provide guidance in choosing and implementing the tools, integration of all the tools and expertise in one end-to-end solution built for non-technical business users is key for digital transformation success for midmarket businesses.
Learn More
Mid-Market Companies: Here’s How to Manage Your Data for the Best Business Outcomes
Mid-Market Companies: Here’s How to Manage Your Data for the Best Business Outcomes
 To make data usable, you need data management. While some think of data management simply moving your data into a cloud or a data lake, it’s much more than this. True data management should focus on making data informative by correlating and integrating data from multiple disparate sources and systems across your organization, adding third-party sources and transactional data created in daily operations.
To make data usable, you need data management. While some think of data management simply moving your data into a cloud or a data lake, it’s much more than this. True data management should focus on making data informative by correlating and integrating data from multiple disparate sources and systems across your organization, adding third-party sources and transactional data created in daily operations.
Data management should also include:
- Cleansing the data to reduce errors
- Normalizing it so that aggregated information may be used for reporting, analytics, and better decision-making
- Governance for compliance with regulated industry and data privacy laws, and to ensure authorized access
- An audit trail of changes made to the data and which systems are using it
Cost Concerns
It’s a big job, so it’s no surprise that enterprise-sized companies often have a financial advantage over the mid-market when it comes to data management. That’s because while enterprises likely have in-house teams with the necessary data management skillsets, it’s cost-prohibitive for most mid-market companies to invest in the technical talent needed for data engineering and management. Most mid-market companies do not have the data engineering expertise needed to use data management tools and technologies within their in-house IT team, or their IT team is too busy vigilantly keeping systems stable and secure—which should be IT’s primary and full-time focus.
Nearly half of IT professionals believe that data management is a significant barrier to digital transformation because digital processes and technologies such as the cloud are rapidly evolving and increasingly sophisticated. McKinsey & Company points out that the COVID-19 pandemic significantly accelerated these trends. This means successful data integration and management requires advanced data experts whose job is to stay current on quickly evolving data management technologies, which can be challenging for the mid-market to acquire. And even if you can find this talent, it often does not make financial sense for the mid-market to hire FTEs to obtain the skillsets needed for success.
Heavy Investment
 Nevertheless, finding an effective way to integrate data management is non-negotiable for organizations of any size. Our modern way of doing business includes multiple decentralized data sources and applications, often chosen by separate business units for what works best in their daily operations. This means that in order to get a complete picture of your business, data from multiple cloud sources, on premise sources and third party sources needs to be integrated to keep corporate information consistent across the organization and ensure that decision-making is based on an accurate complete picture of the business. Insights for Professionals found that in 2022, 62 percent of senior IT leaders and company executives surveyed plan to invest in data management, with three-quarters honing in on digital technology and data integration. Gartner reported that in 2021, each company’s average spend on data management tools was close to $250,000. Insights for Professionals results show that in 2022, 30% of IT experts intend to invest up to $500,000 on data management, with around one-quarter planning to spend even more.
Nevertheless, finding an effective way to integrate data management is non-negotiable for organizations of any size. Our modern way of doing business includes multiple decentralized data sources and applications, often chosen by separate business units for what works best in their daily operations. This means that in order to get a complete picture of your business, data from multiple cloud sources, on premise sources and third party sources needs to be integrated to keep corporate information consistent across the organization and ensure that decision-making is based on an accurate complete picture of the business. Insights for Professionals found that in 2022, 62 percent of senior IT leaders and company executives surveyed plan to invest in data management, with three-quarters honing in on digital technology and data integration. Gartner reported that in 2021, each company’s average spend on data management tools was close to $250,000. Insights for Professionals results show that in 2022, 30% of IT experts intend to invest up to $500,000 on data management, with around one-quarter planning to spend even more.
Looking ahead to 2024, Gartner also reports that cloud-native platforms will serve as the foundation for more than 75 percent of new digital workloads. This statistic is particularly meaningful for mid-market companies, where end-to-end solutions become a lifeline to leverage cloud technology efficiencies and advancements without the need for hiring in-house expert skill sets. The right end-to-end solution for the mid-market pairs the right combination of tools and technologies with access to the expert talent needed to achieve value and success. The right end to end solution includes everything so that mid-market companies need not spend years trying to piece together a solution out of countless possible tools and technologies. Building it just takes too much time and resources away from the primary business of most mid-market companies—and the mid-market does not have time to wait for this and thrive against competitive pressure from large enterprises.
By 2024, Gartner predicts that three quarters of organizations will have deployed multiple data hubs to drive data and analytics, since companies should only make decisions based on a complete picture of their data. But for mid-market companies with affordability concerns, few solutions meet the need for data management technology that enables companywide data integration as well as third-party data.
Solutions for the Mid-Market
 Since mid-market firms that want to stay competitive can’t afford to fall behind enterprise-sized companies when it comes to data management, what can they do? Mid-market companies need technical experts to help build solutions, and research shows these solutions will be cloud-based. Insights for Professionals found that in 2022, close to two-thirds (63 percent) of senior IT leaders and company executives surveyed expect to invest in cloud infrastructure as a service. It makes sense over trying to maintain servers on-premise, recognizing that on-premise solutions have morphed into dinosaurs. According to Gartner, 85 percent of companies will have moved to a cloud-first approach by 2025.
Since mid-market firms that want to stay competitive can’t afford to fall behind enterprise-sized companies when it comes to data management, what can they do? Mid-market companies need technical experts to help build solutions, and research shows these solutions will be cloud-based. Insights for Professionals found that in 2022, close to two-thirds (63 percent) of senior IT leaders and company executives surveyed expect to invest in cloud infrastructure as a service. It makes sense over trying to maintain servers on-premise, recognizing that on-premise solutions have morphed into dinosaurs. According to Gartner, 85 percent of companies will have moved to a cloud-first approach by 2025.
Yet most hyper-scaler cloud service providers are priced for large enterprises, particularly to get the level of help that mid-market companies require. What’s more, many enterprise hyperscalers don’t offer data management, since their services focus only on migrating data to third-party cloud vendor platforms. Mid-market businesses need a hyperscaler capable of providing data management within a mid-market budget.
To ensure that important business decisions are not made based on inaccurate information, the mid-market needs an affordable data-cleansing solution.
Ideally, this means that data management would transform the data into decision-ready, analytics-ready status, including transactional data that sheds light on operations and customer behaviors. Gartner predicts that through 2024, half of organizations will adopt modern data quality solutions to better support digital business initiatives. To keep from falling behind, the mid-market must follow suit.
The Key to Consistency
In order to keep data consistent across the organization, another solution for the mid-market is to adopt master data management (MDM). MDM helps to ensure that if a customer’s contact information is updated through customer support, for example, then accounting and all other functional business units will receive the updated information. If data is kept in multiple siloes, operational efficiency decreases as employees spend time trying to track down data for reporting, analyzing, and determining which details are correct.
MDM technology has traditionally only been accessible to large enterprises due to its high cost, as most MDM platforms are a huge expense and implementation takes more than a year to achieve. These platforms typically also require highly skilled FTEs to use and maintain, which can be another cost consideration that rules out mid-market companies.
The answer to successful mid-market data management is to establish a side-by-side partnership with a data platform company to gain the benefits of working with experts and gain access to highly skilled technical resources to achieve true business value. By getting this help, you can devote your company’s time, resources, and innovation to your business and focus on what you do best.